
What websearch.searchinweb.info does seem to be simple and confined to browsers, there are some hidden dangers that should be notified. The advertisement on its interface manifests that websearch.searchinweb.info is a freeware that needs fund to keep running. By posting ads with its arbitrary character, websearch.searchinweb.info manages to obtain funds, which indicates that more pop up ads can be expected before long. Some may pop-up, pop-in or pop-under and some may underline in-text message with hyperlinks directing to ads.
There are hundreds of thousands of browser hijackers nowadays, among them Babylon (read more) and conduit are the most notorious. Websearch.searchinweb.info is merely a new version to execute the same deeds. It is thus believed that the hijacker possesses loose programming and language; bugs can be found anytime, which give infections big chance to worm into the computer harassed by websearch.searchinweb.info.
Once websearch.searchinweb.info being exploited, its JS technology will be utilized to help collect log-in credentials, making it possible to spread other virulent code in the name of the victim’s without knowledge; or even worse, empty out bank card without authorization. It is always recommended by VilmaTech Online Support that any potential safety hazard should be eliminated as soon as possible. Live chat with senior technician if any specialized technical help is wanted.
What all anti-virus programs base on to kill infections is malicious attribute code. They are man-made and not that smart enough to tell if the explorer.exe (system running process) being modified by websearch.searchinweb.info is guilty or not. Besides, there’s no malicious attribute code injected in websearch.searchinweb.info as it doesn’t takes typical way to affect a system. All websearch.searchinweb.info wants is no more than traffic. Therefore, removing websearch.searchinweb.info with automatic method by security utilities is unworkable. Below are the manual removal steps to follow up that could help with a complete removal. It should be widely advised that specialized computer knowledge is required to complete the procedures correctly and integrallty so that no vicious piece generated by websearch.searchinweb.info or no incidental items would be left to help with its survival.
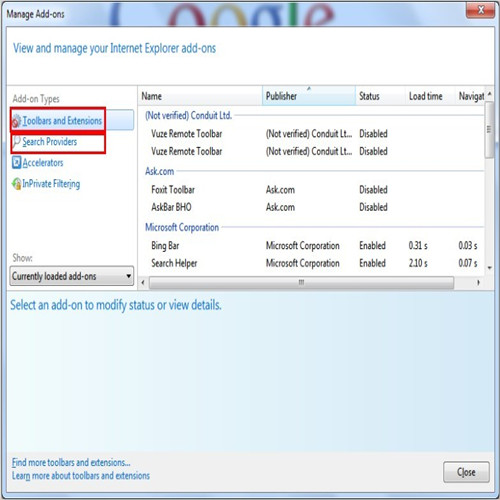
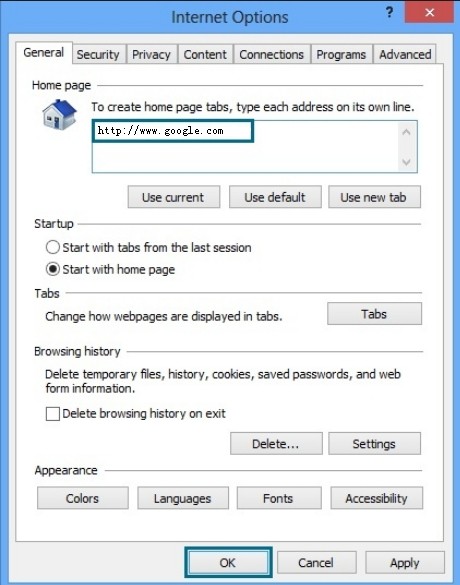
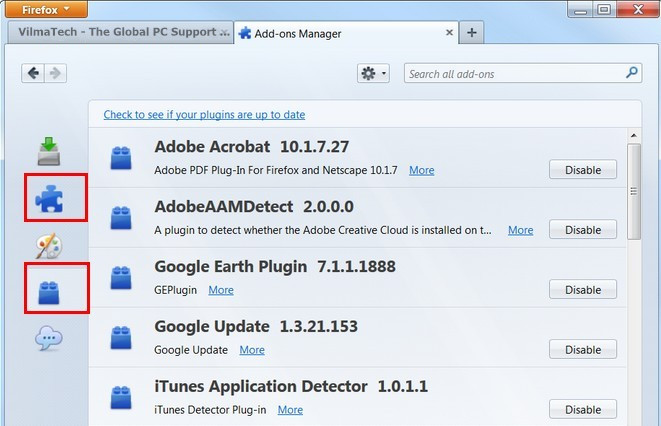
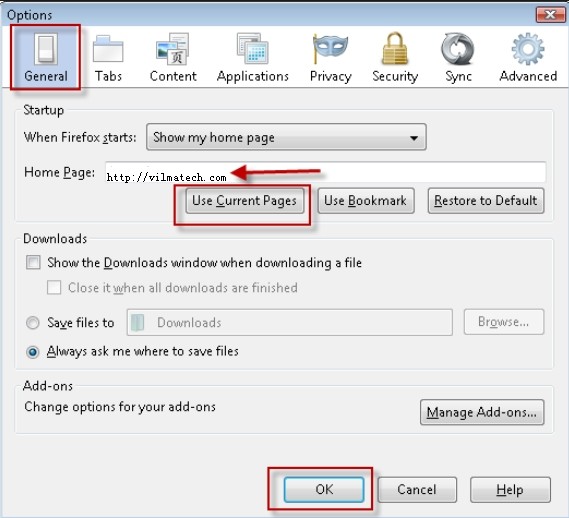
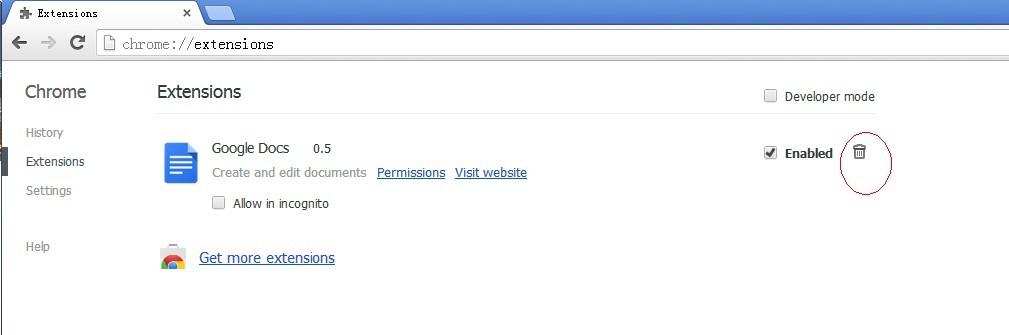
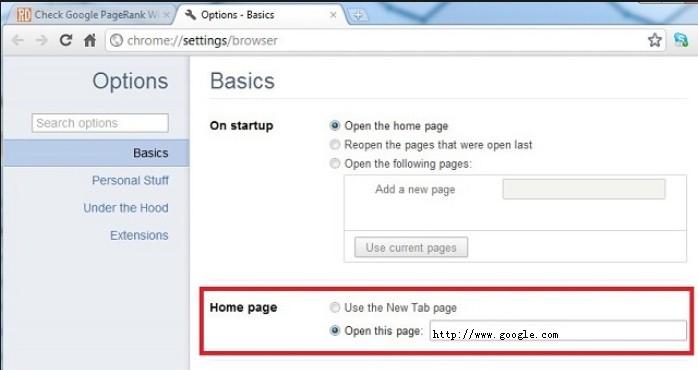
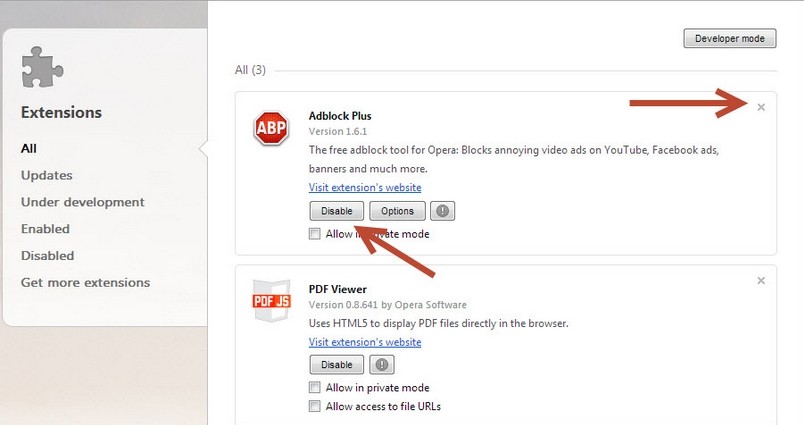
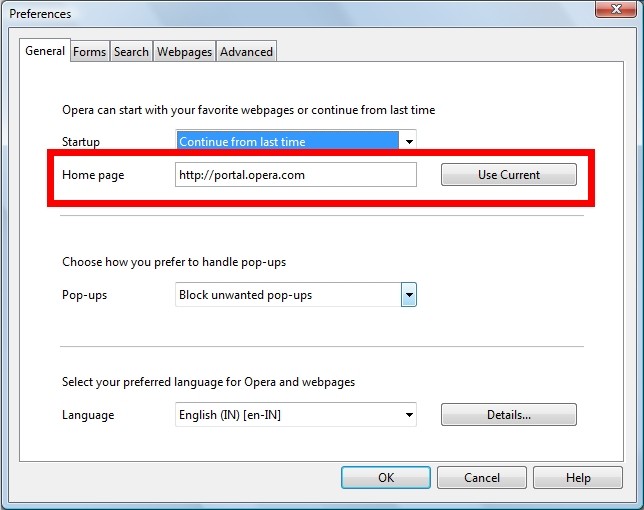
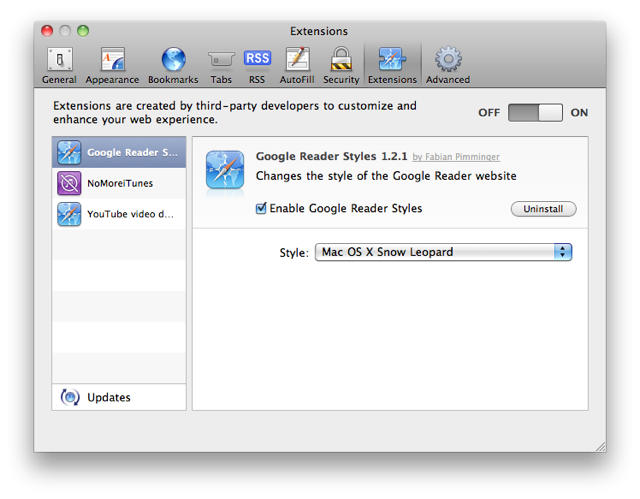
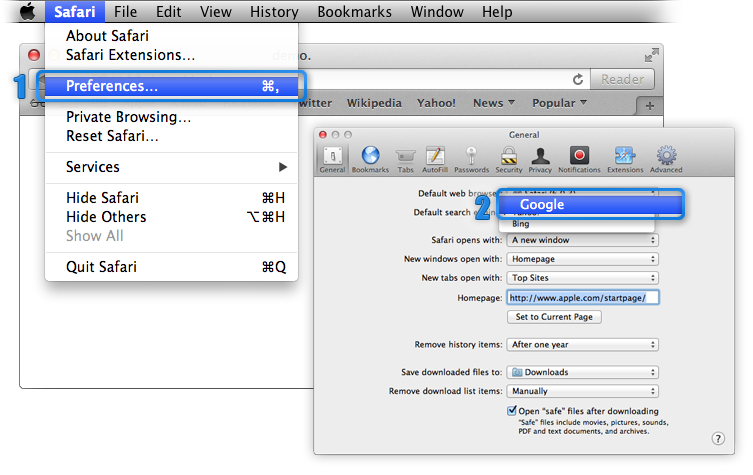
Step1. remove websearch.searchinweb.info’s extension from browser settings and change default homepage.
Internet Explorer
Mozilla Firefox
Google Chrome
Opera
Safari
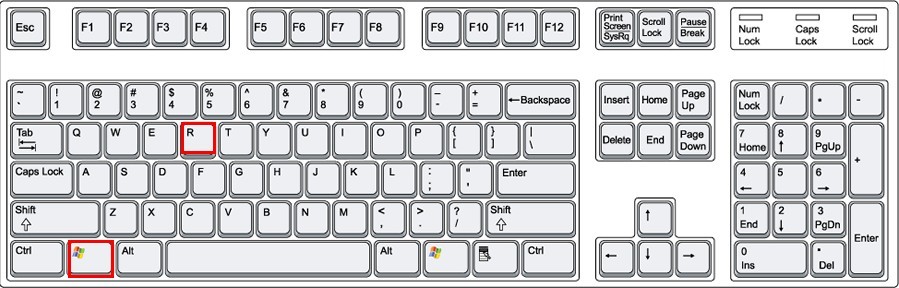
Step2. close out browser and access Database to remove the items associated with websearch.searchinweb.info.
Windows
Tip: For Mac OS X users, there isn’t a Registry Editor in the Mac like in Windows to change settings. However, one could remove websearch.searchinweb.info from “/Users/YourUserName/Library/Preferences”, /Safari/ Preferences/extensions/, /Safari/Help/Installed Plug/Ins & list, /Library/Internet Plug-Ins/ and ~/Library (in home folder)/Internet Plug-Ins/.
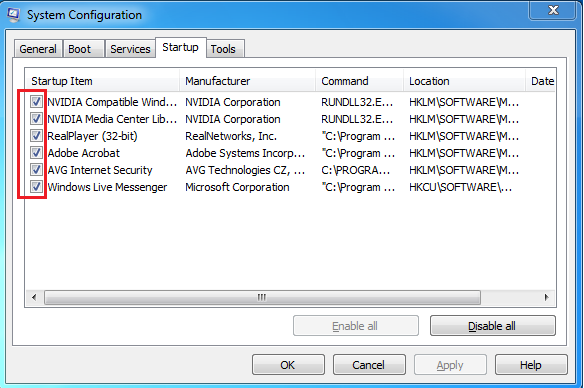
Step3. Manage start up items to speed up starting up and disable websearch.searchinweb.info’s malicious start up items by using in-built utility.
Windows 7/XP/Vista
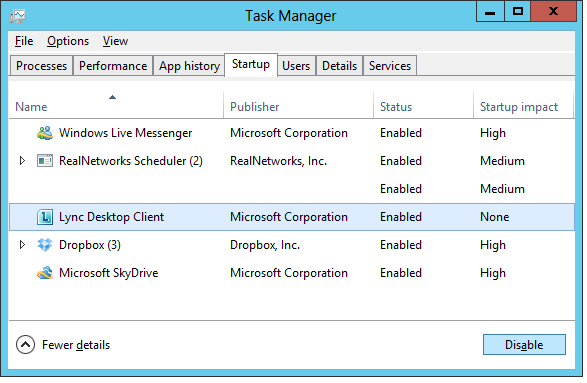
Windows 8
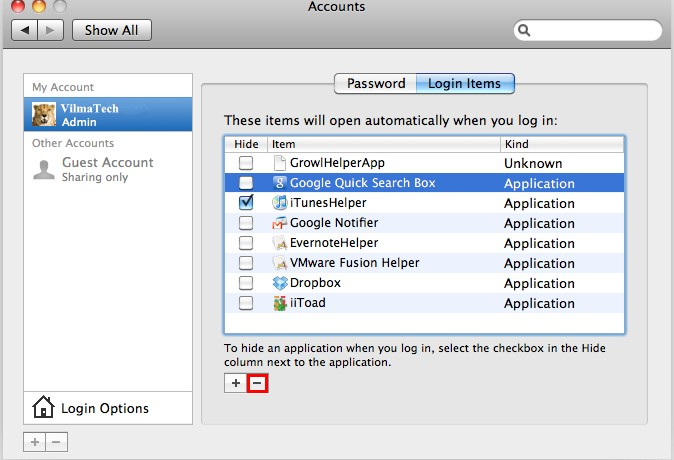
Mac OS X
“How websearch.searchinweb.info enters a machine” has not yet been widely known by PC users, which brings to crazy spread of the browser hijacker. As a web application, there’s a big chance for websearch.searchinweb.info to be brought in by other web applications such as toolbar, extension and adware as nowadays web applications are in relation network to promote sales online. Therefore, attention should be drawn to drive-by download when installing a third-party program.
Though websearch.searchinweb.info is no more than a browser hijacker serving as a traffic exchanging site to intercept traffic, it manages to worm into a machine through vulnerability among installed programs or in the target system. With BHO technology, websearch.searchinweb.info preloads its information, Applet and executable files into browser setting and next takes control of ActiveX and JavaScript to manipulate searching. This implies that the target machine is so vulnerable to be hijacked by websearch.searchinweb.info.
Websearch.searchinweb.info can also be taken advantage by virus, especially the Trojan Horse like Win64:Bot-A (read more) that aims to collect log-in credentials and other confidential information. In sum, do not throw your ignorance to websearch.searchinweb.info hijacking problem even when it stays silent and keeps running just like a normal search engine.
With more infections coming onto the target machine controlled by websearch.searchinweb.info, more exotic files, folders, documents and data will be settled as well to occupy limited space and modify build-in settings, thus the below mechanical problems can be anticipated:
The above steps are designed exclusively to websearch.searchinweb.info rather than other incidental infections or problems. One should avoid deviation and mistake to finish the instruction without triggering more problems and should be well equipped with computer knowledge when rectifying Database so that no permanent damages would appear over time. No matter how expert you are, it is advisable to backup registry beforehand, just in case. Since few people know how to back up registry in Windows 8, here’s the video to show clearly.