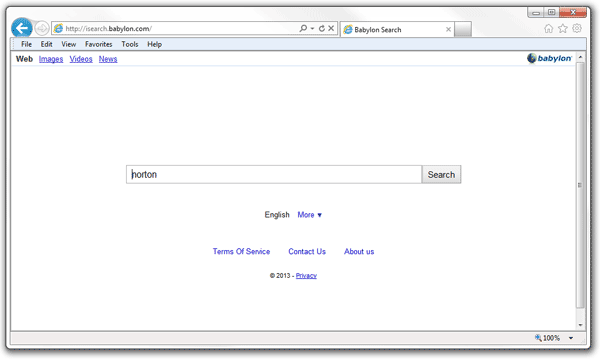
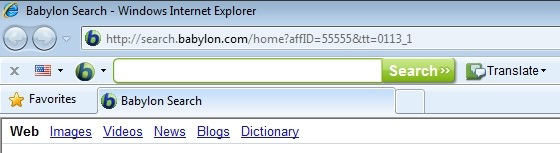
Isearch.babylon.com is a latter version of www.search.babylon.com, search.babylon.com and www.babylon.com hijacker. They share almost the same interface. According to the complaints posted on various PC help forums, isearch.babylon.com has been alive on the Internet for more than a year so far to ruin surfing experience on IE, Firefox, Chrome and other non-IE-kernel browsers:
Isearch.babylon.com is strictly speaking a traffic exchanging site (whose salient features are duplicate content, redirection and random ads attached to the interface) and it is classified as browser hijacker. Such browser hijacker is actually working to improve the rating and ranking of a Babylon software, a computer dictionary and multi-task translator developed by an Israeli public company – Babylon Ltd by frequently directing people to associated products and its partners’ web sites.
As a browser application to boost exposure rate, isearch.babylon.com would introduce in additional web applications for a reinforced operation. Among them, babylon toolbar is the commonly seen third-party software to be brought in by isearch.babylon.com browser hijacker.
Apart from babylon toolbar, other web apps can be anticipated when isearch.babylon.com takes controls. VilmaTech Online Support would like to recommend a continuous reading for a correct knowledge on its insidious dangers. Click on the button below to live chat with VilmaTech specialized professor for exclusive help whenever it is ever required.
Though isearch.babylon.com is not technically a virus, its injection of startup item, modifications on DNS and other browser settings would be sufficient to result in vulnerability on browsers. Such vulnerability can be easily found by other infections including ransomware (the one has long been detected to spread through the Internet).
If any notice of the advertisement on isearch.babylon.com has ever been taken, it can be readily inferred that adware would pops up after a while when isearch.babylon.com settles. PUP.Optional.Babylon might be then flagged by installed security utilities. All these would definitely drag down the general PC performance with an unreasonably consumed CPU by more and more exotic items piling up in both browser settings and local disk without permission.
Additional vicious infiltration can be dangerous enough, but the real danger lies in the techniques adopted by isearch.babylon.com:
Once those two technologies are taken advantage by the infections that have successfully exploited the vulnerability, the technologies will be utilized to preload virulent items automatically and record log-in credentials without your knowledge, leading to severe mechanical damages, money loss and identity theft.
Anti-virus program usually comes into one’s head when something is wrong with a computer. Some reported that isearch.babylon.com went back to “Trusted” list offered by a security program soon after it was blocked; and some said that removing babylon extension and the babylon.exe from browser setting would bring no success. Isearch.babylon.com is not a cunning infection that manages to escape automatic removal; it is the technologies introduced in the above section that help isearch.babylon.com not to be identified as malicious when it is making troubles.
VilmaTech Online Support would like to kindly remind you that isearch.babylon.com is more than a browser application as it makes other modifications in system configurations. That’s why cleaning up browser settings is not sufficient to stop isearch.babylon.com from coming back. Below is the tech support to assisting in removing isearch.babylon.com and restoring homepage. Stick to the steps and help yourself. On the occurrence of difficulty, please get specialized technical help from security assistance by starting a live chat here.
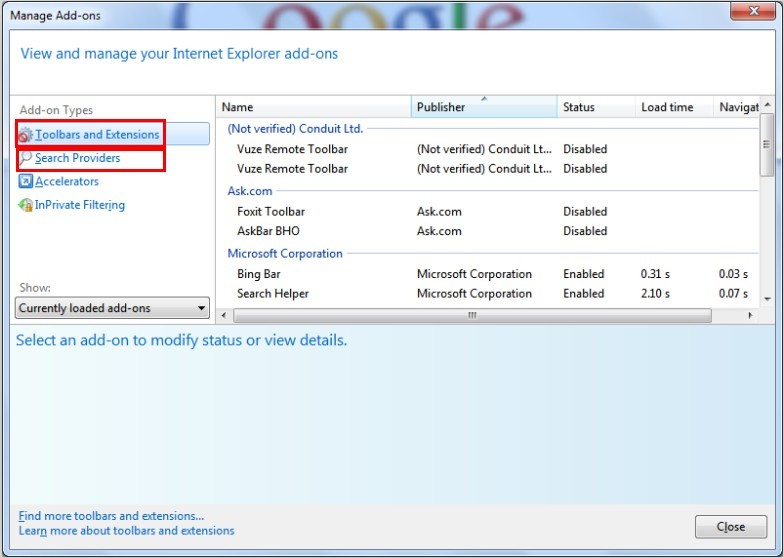
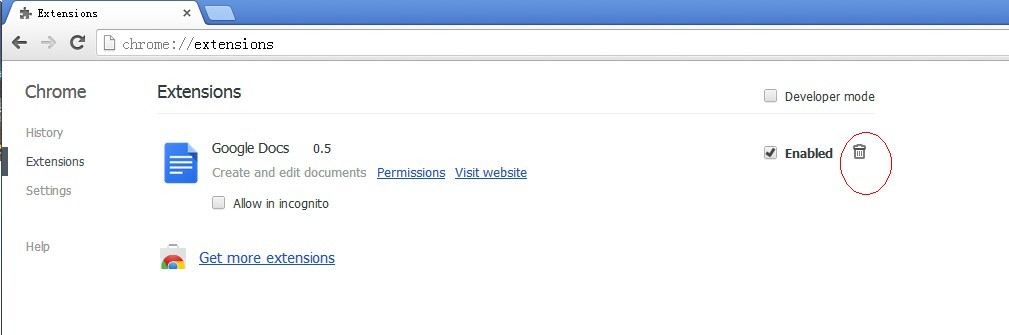
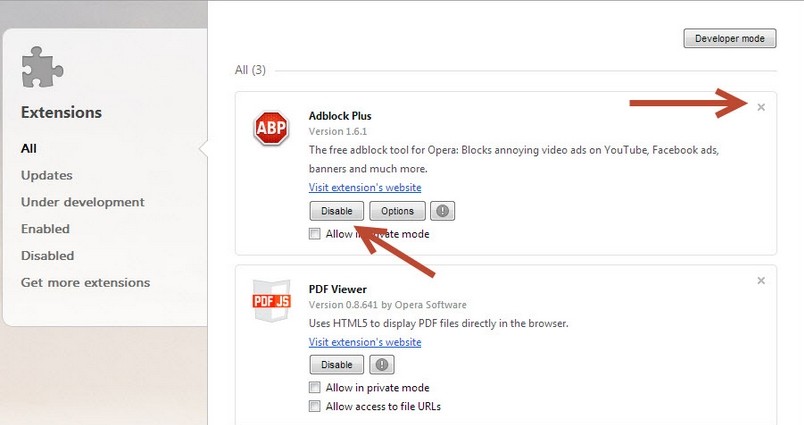
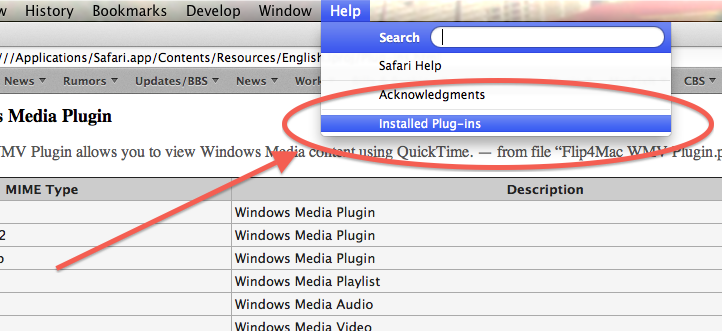
Step One : remove Babylon extension/plug-in/add-on from browser settings.
Internet Explorer
Mozilla Firefox
Google Chrome
Opera
Safari
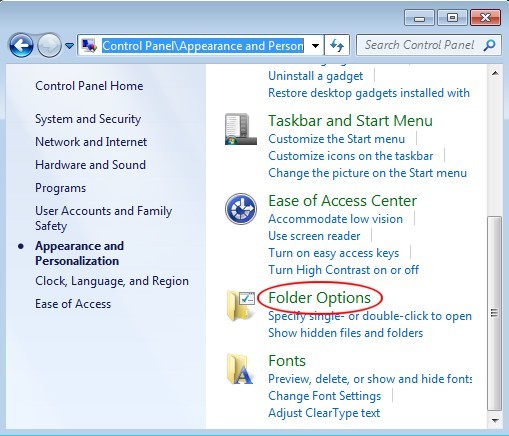
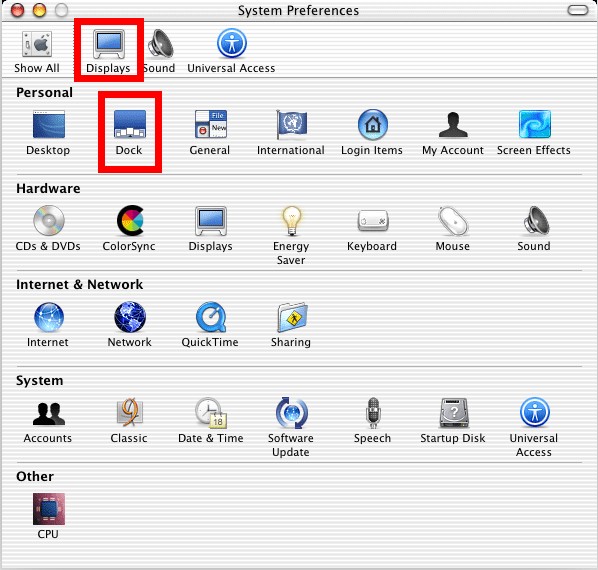
Step Two: show hidden items to remove the ones generated by Isearch.babylon.com in local disk.
Windows 7/XP/Vista
Windows 8
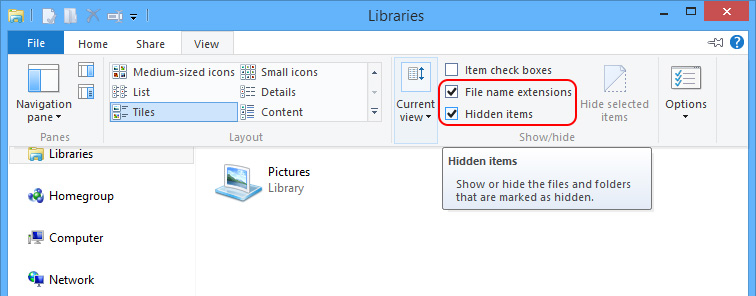
Files and folders to delete:
newdotnet2_91.dll (C:\WINDOWS\system32)
Mac OS X
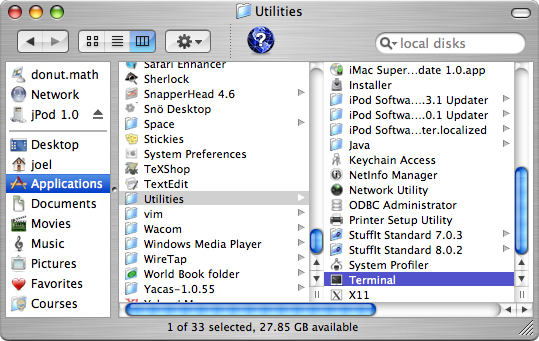
Files and folders to delete:
Items related to isearch.babylon.com located in “/Library/Internet Plug-Ins/” (hard disk icon -> Library folder).
Items related to isearch.babylon.com located in “~/Library/Internet Plug-Ins/” (hard disk icon -> home folder -> Library folder).
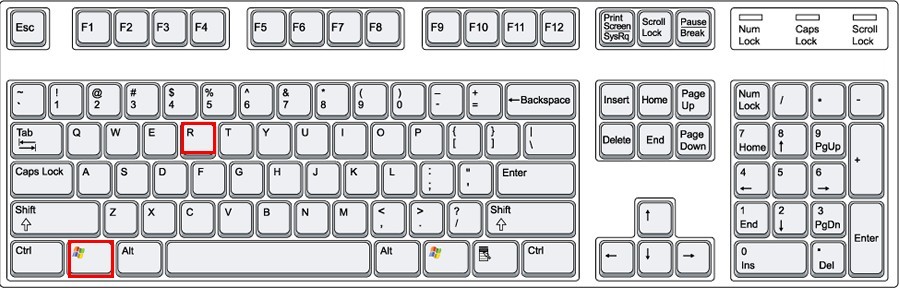
Step Three: navigate to Database (there’s no such configuration on Mac OS X) to rectify or remove items associated with Isearch.babylon.com.
(Tip: professional computer skills and knowledge are required when modifying registry requires; otherwise Registry backup is recommended to remedy mistake, if any, before making rectifications. The video is hereby offered to mainly shows registry backup in Win8 since most people don’t know how to do so with Windows8 OS.)
Step Four: remove all items related to Isearch.babylon.com from control panel.
Windows 7/Vista/XP
Windows 8
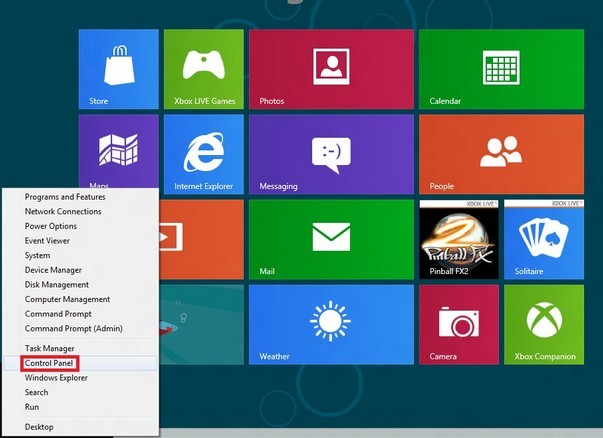
Mac OS X

With huge traffic, isearch.babylon.com is capable of convincing third-party programs to bundle with it so that ratings can be significantly improved within a short period of time. As a freeware, isearch.babylon.com hijacker needs fund to sustain life, which well explains why there are random ads posted on its interface and that why more and more ads are caught in sight before long. Apart from driver-by downloads, isearch.babylon.com can be brought in by other related web applications, Babylon toolbar for instance; or it is able to worm into a machine with vulnerability/backdoor/loophole. All these can be prevented if:
Be noted that brought in items and some remnants relevant to isearch.babylon.com have the capability of calling the browser hijacker back after the above provided instruction. More technical skills and knowledge are required to dig out extra malicious items after removing isearch.babylon.com with the exclusive tech support guide. In the event that incidental issues block the way to remove isearch.babylon.com completely, please do feel free to contact VilmaTech Online Support and seek peace after a quick fix.