Usually, feed.helperbar.com would redirect victims to isearch.babylon.com (read more) and snap.do search engine page. When done, feed.helperbar.com disappears, bridging the gap between user end and rogue web sites. Therefore, whenever search is made, whether it is trough URL or search bar, feed.helperbar.com redirects the request to its destinations and no anti-virus program will pick it up, needless to say remove it.
The reason for creating virus has always been profitable income. By redirecting user end to designated web sites, feed.helperbar.com assists in accumulating traffic for a higher rating on the Internet and obtaining easy money thereby for its backstage author. There’s a widely accepted statement that feed.helperbar.com was created by the same author owning various browser hijacker and rogue search engine; it is no more than an auxiliary means to get those rogue sites exposed to as more PC users as possible so that they are enabled to bombard users with a wide variety of products for sales promotion.
In spite of the auxiliary means it takes and its short span of time, feed.helperbar.com remains as a hazardous item to both security and computer health. Keep reading to find out the risk and acquire recommended way to remove feed.helperbar.com. In case of error, mistake or difficulty, live chat with senior technician at VilmaTech Online Support to get instant help.
To ensure a permanent redirect, feed.helperbar.com has to put its service as well as startup item into system configuration and to manipulate DNS settings with JavaScriot technology. Such modification would degrade the browsing security and give rise to vulnerability (Insecure configuration management). Web vulnerability has been taken as one of the major ways to spread vicious codes rapidly and efficiently.
Besides, as an auxiliary means, feed.helperbar.com is programmed loosely where bug can be found and exploited anytime. Once a bug is being exploited when feed.helperbar.com is redirecting, the target machine will be attacked definitely. What’s worse, JS technology adopted by feed.helperbar.com will be utilized to collect log-in credentials so that hacker can send spread virulent codes easily to all contacts in the user’s name to dodge arrest.
Under the circumstances where additional items worming into the target machine through web vulnerability, memory leak and other issues can be expected; thus much of CPU will be directed to tackle the mess thereby, leaving a fraction of internal storage to support installed security utilities and restricting its full play. The target computer will be consequently weakened to susceptible to aggressive infections.
Carrying malicious ActiveX, Applet and JavaScript documents, feed.helperbar.com is capable of escaping complete removal by installed anti-virus programs that are programmed to remove vicious attribute code. Virus like feed.helperbar.com is getting smarter to inject its code into Windows protected zone and drivers concerning system processes (svchost.exe for example) and security service to confuse “protectors”.
Considering the fact that feed.helperbar.com manages to dodge automatic removal and return after each reboot, manual removal method is highly recommended. However, advanced computer skill is required to differentiate the genuine system items and the verisimilar ones generated and affected by feed.helperbar.com so that a complete and thorough removal can be achieved without incidental issues. Below are the recommended steps to help remove feed.helperbar.com without its re-image. On the occurrence of unexpected situation, get quick fix according to your concrete situation from VilmaTech specialized professor.
Step One – end rung processes and services related to feed.helperbar.com.
Windows
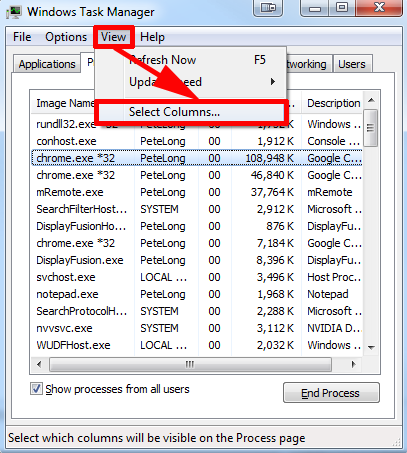
Process to exterminate:
- End the processes with the path referring startup section, C:\Program Files\ feed.helperbar.com, C:\Users\AppData\Local\ feed.helperbar.com, C:\Users\AppData\LocalLow\ feed.helperbar.com and C:\Users\AppData\Roaming\[browser that has feed.helperbar.com]\Profiles\.
- End WINLOGON.EXE, iexplorer.exe and load32.exe if any.
- End non-system running process after exiting all programs.
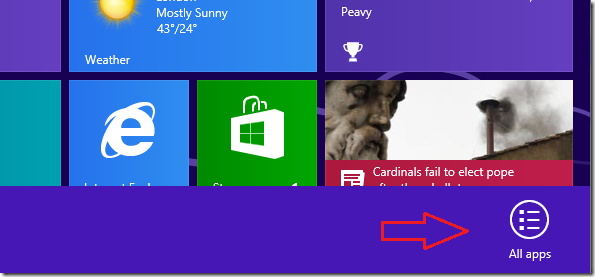
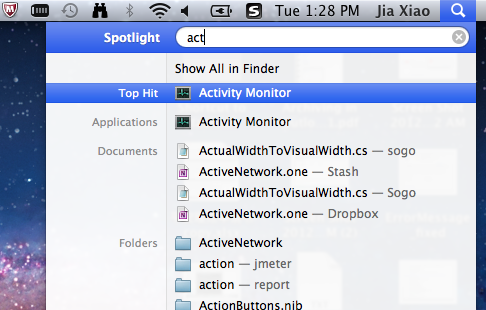
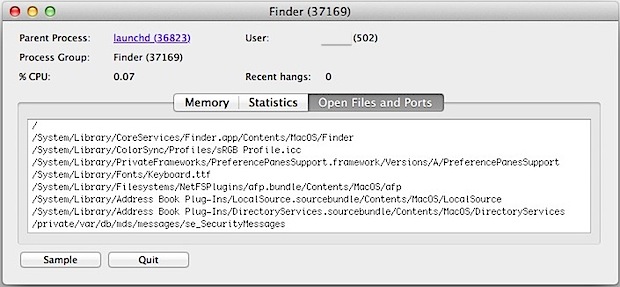
Mac OS X
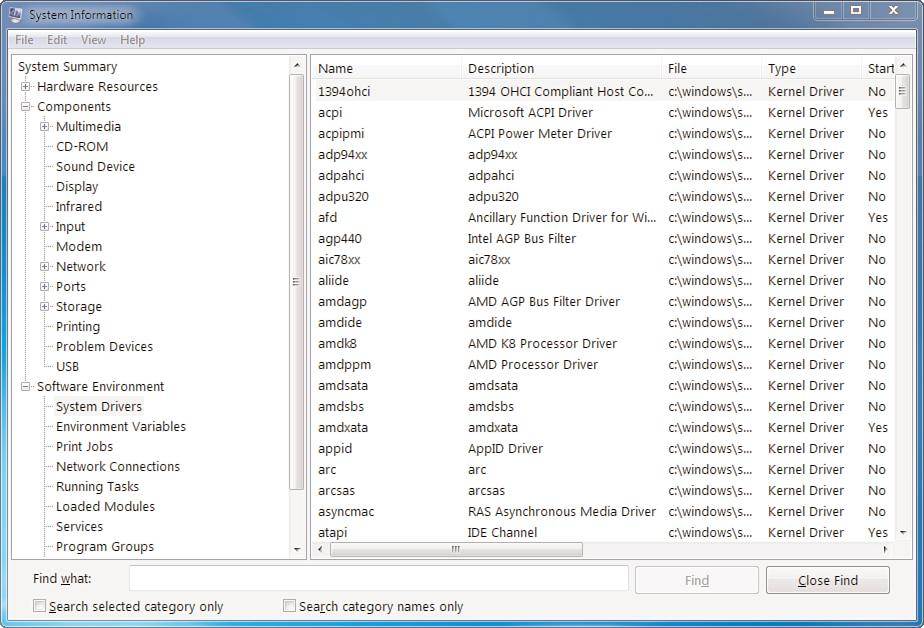
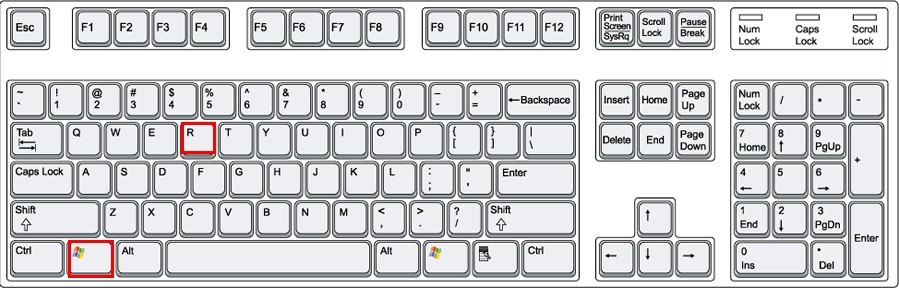
Step Two – remove the entries generated by feed.helperbar.com from Database.
Windows
HKCR\CLSID\{random number}
HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Browser Helper Objects\{random number}
HKCR\CrossriderApp{random number}.BHO
HKCU\Software\InstalledBrowserExtensions\{random number} Apps|{random number}
add DisableRegistryTools to the following entry with the value named DWORD and set its value as “1”:
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System
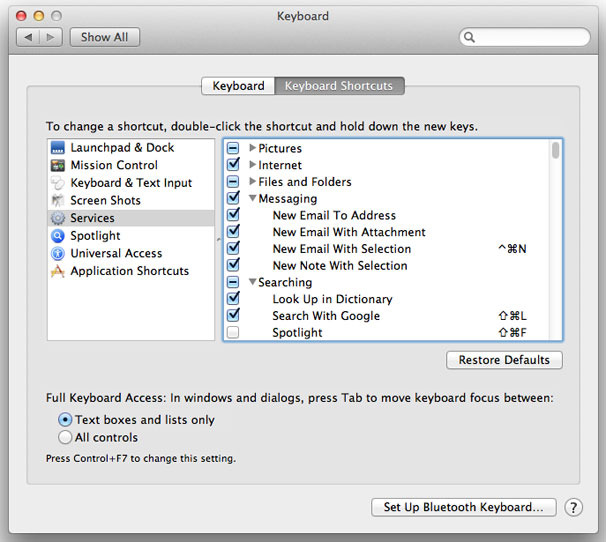
Tip: For Mac OS X users, there isn’t a Registry Editor in the Mac like in Windows to change settings. However, one could remove feed.helperbar.com from “/Users/YourUserName/Library/Preferences”, /Safari/ Preferences/extensions/, /Safari/Help/Installed Plug/Ins & list, /Library/Internet Plug-Ins/ and ~/Library (in home folder)/Internet Plug-Ins/.
Step Three – eradicate all the extensions and items generated by feed.helperbar.com from browser settings.
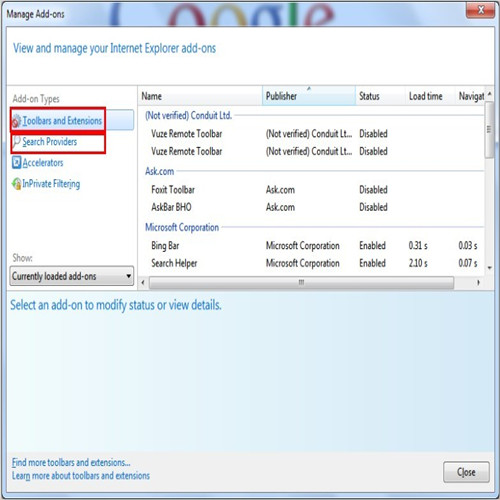
Internet Explorer
Access IE’s Tools and navigate to “Manage add-ons”; search for items related to feed.helperbar.com and remove them from ‘Toolbars and Extensions’ and ‘Search Providers’ respectively.
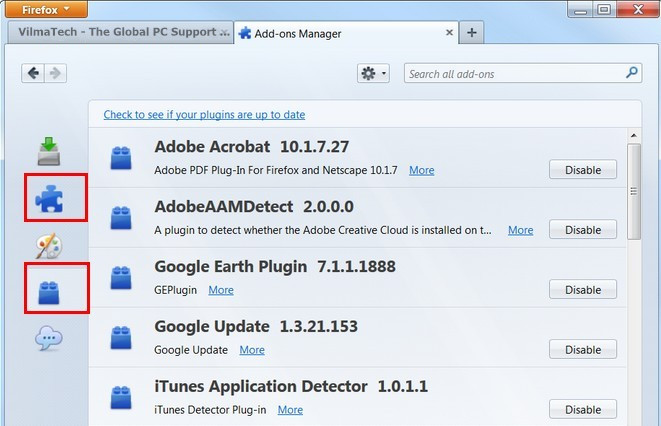
Mozilla Firefox
Access Tools menu and bring up Options window; search for items related to feed.helperbar.com and remove them from ‘Add-ons’ and ‘plugins’ respectively.
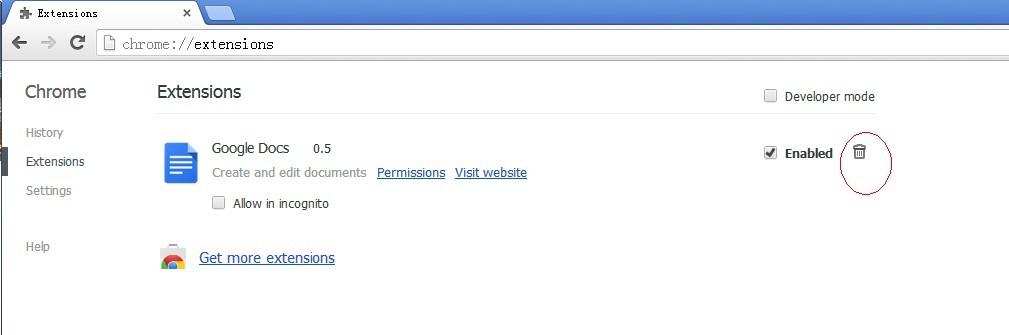
Google Chrome
Click on the spanner icon in the upper right and unfold “Tools” menu to go to ‘Extensions’; search for items related to feed.helperbar.com and remove them from there.
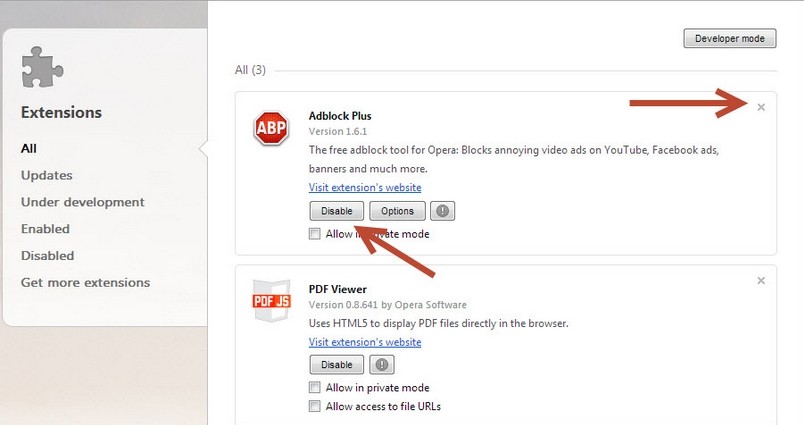
Opera
Spread Opera menu and bring up Extensions window to click open “Manage Extensions”; search for items related to feed.helperbar.com and remove them from there.
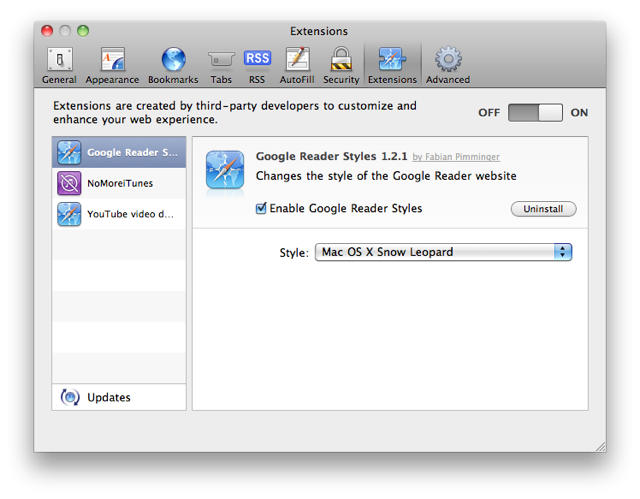
Safari
Unfold Safari Menu and bring up Preferences window to tap on extensions tab; search for items related to feed.helperbar.com and remove them from there.
This list shows the issues that can be triggered by feed.helperbar.com redirection. It should be advised that the earlier the removal is taken, the less the consequences will be detected.
There’s no intention to scare victims. This is how virus act to obtain easy money and this is why various virus emerge in endlessly. There is a lot of insecurity in cyberspace. Any carelessness could have call feed.helperbar.com back or more infections. Before taking any further actions, we would like to suggest you think beforehand about the several questions listed below:
Complete removal is always stressed by senior technicians as remnants of vicious items could give rise to error message due to incompatibility and conflict. Besides, left pieces can help feed.helperbar.com survive again after all the cumbersome removal procedures. Though feed.helperbar.com mainly makes troubles on browsers, rectifications and removal are required to be done deep in system configurations such as Registry Editor for a complete removal.
Registry Editor (Database) involves all the significant information of the entire machine. Any mistake made there could cause tangled mechanical problem. Therefore, VilmaTech Online Support would consider it wise to back up registries before making rectifications in Database. Here’s the video to show how.