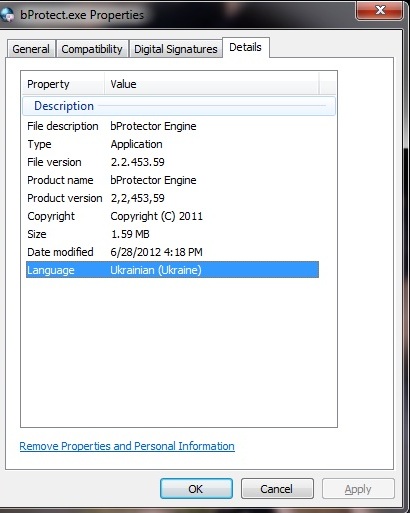
Many people consider that bProtect.exe is virus and or at least harmful as it has been always constantly flagged by installed security utilities and does trigger pop-ups supported by Adware-Bprotect (read more). As the image shown in the above, bProtect.exe is not a Windows kernel file, instead it is a process developed by bProtector to support the running of relevant third-party program.
Usually there are two major places that a normal bProtect.exe would settle. One is the subdirectory of “C:\Documents and Settings” (C:\Documents and Settings\All Users\Application Data\bProtector\ to be more specifically) and that of “C:\Program Files”. bProtect.exe situated in the former directory is invisible with the capability of manipulating other processes while the one located in the latter directory possesses no visual window with the ability to monitor applications as well as record keystrokes. In sum, bProtect.exe is technically threatening. To get more details about the hidden dangers, reasons and solution, it is advisable to keep reading. On any occurrence of emergency that needs quick fix, please do feel free to contact VilmaTech Online Support and ask its senior technicians for on-demand help.
As stated above, bProtect.exe is technically threatening. So there have been cases that bProtect.exe is issued by advanced infections to prevent from automatic removal as bProtect.exe has not been considered to be vicious. The reason why the running process being picked up by installed anti-virus program is simply because of some suspicious modifications in registry entries. Without attribute code, anti-virus programs are not able to remove anything.
To tell if bProtect.exe is issued by infections, a close look at its location will do. Bprotect.exe being used by virus would be injected under c:\windows or c:\windows\system32. Also the below problems would further help with verification:
It is a tough task to deal with bProtect.exe being utilized by virus as it is signed fraudulently with a GoDaddy certificate and thus makes victims think that it is a legitimate file by sitting in nested files. Consequently, bProtect.exe manages to replicate itself within seconds if deletion has been ever undertaken. Besides, bProtect.exe issued by virus is usually attached with verisimilar Microsoft’s signature as shown below. This could definitely out trick security program.
Remark: Microsoft HotFixes
Product Version: 5.04.0103
Brand Name: Microsoft HotFixes
Company: Microsoft Corporation
Legitimate Trademark: Microsoft HotFixes
Internal Release: Installer94
Source File Name: Installer94.exe
In such case, manual removal method is recommended to be executed right away before any further damages are made to threaten both computer health and information security as a counterfeit bProtect.exe is written with VB language to bundle itself to normal files. When the bundling work is done, the process will release virus (remote Trojan normally) and shut down firewall without authorization. Here are the consequences without timely removal of vicious bProtect.exe:
Brief summary: bprotect.exe is responsible to run associated third-party program. If you consider it potentially dangerous, it is good to uninstall the relevant program. However, bprotect.exe can be issued or utilized by infections due to its capability of manipulating actions, monitoring applications and recording inputs. Below is the instruction to help remove bProtect.exe and solve bProtect.exe error issue. Be noted that USB memory stick or other off-board device is not recommended to connect to the vulnerable computer for the prevention of broader affection. Stick to the steps and help yourself. Should failure occurs due to unknown reason, you are welcome to seek specialized technical help by contacting recommended PC Security Center.
Step One: reset browsers to restore setting without anything related to bprotect.exe.
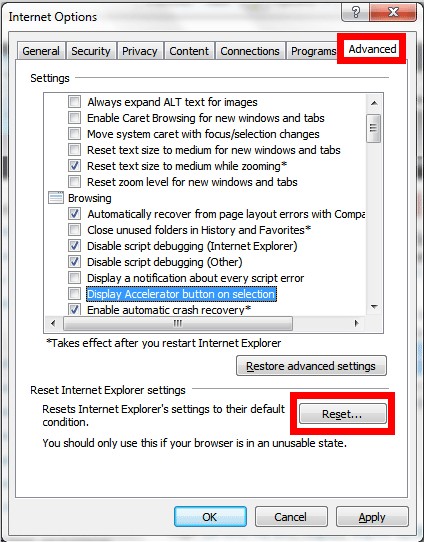
Internet Explorer
Go to its Tools menu and select Internet Options; hit on Advanced tab and press Restore Defaults button.
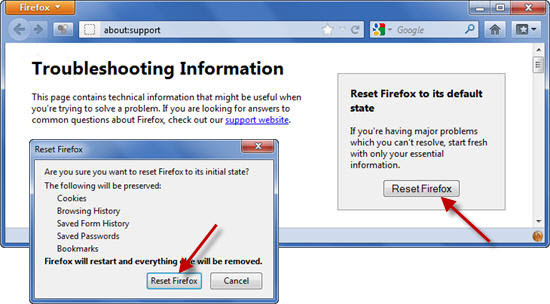
Mozilla Firefox
Click on the Firefox button and select Troubleshooting information in the option list of Help; press on ‘Reset Firefox’ button to reset Firefox.
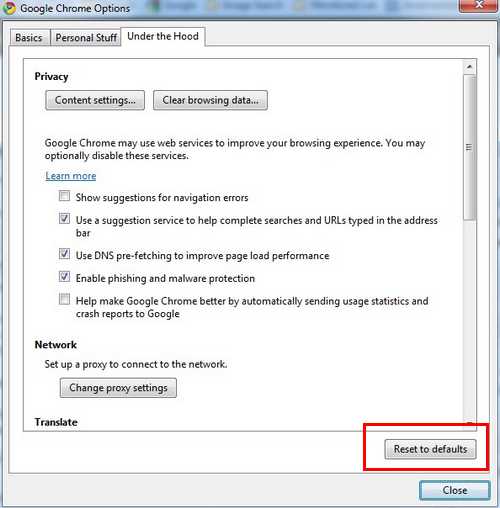
Google Chrome
Spread ‘Customize and Control Google Chrome’ menu and go for ‘Options’; hit ‘Under the Hood’ tab to press ‘Reset to Defaults’ button.
Opera
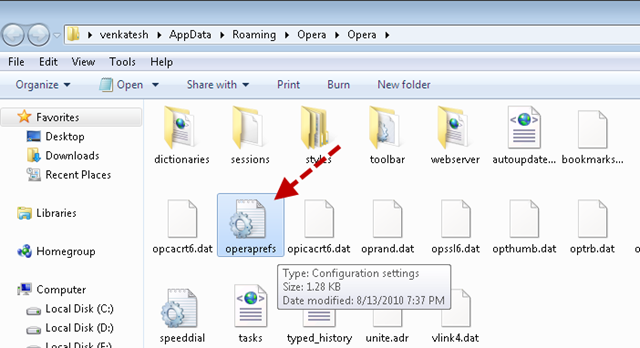
Close Opera and navigate to “C:\Users\user_name\AppData\Roaming\Opera\Opera\”; remove Operapref.ini file will reset Opera.
Step Two: clean up Temp files, among them would be the ones associated with bprotect.exe.
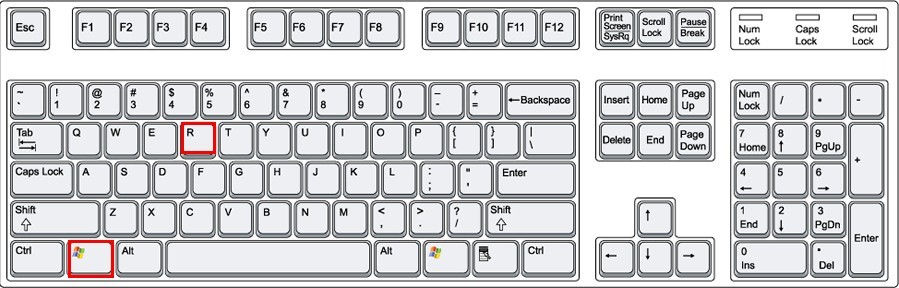
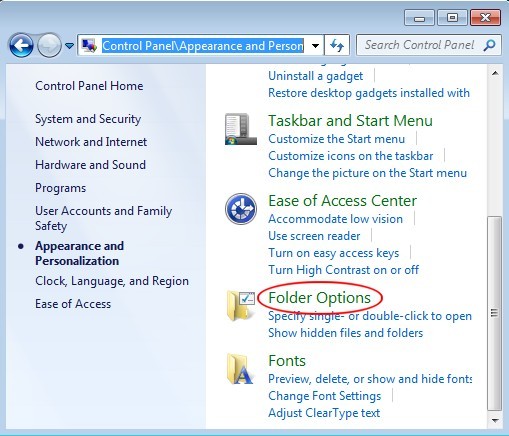
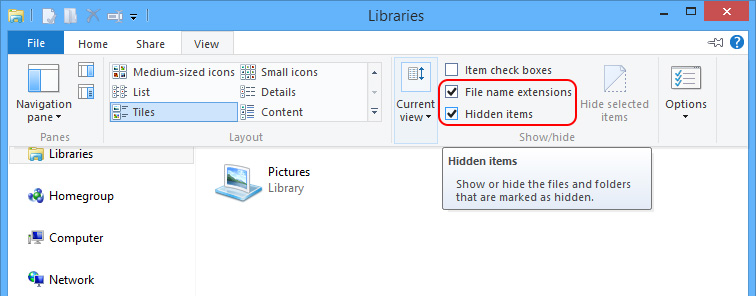
Step Three: show hidden files and folders to remove
Windows 7/XP/Vista
Windows 8
C:\Windows\system32\rundll32.com
C:\Windows\system32\msconfig.com
C:\Windows\system32\regedit.com
Step Four: repair local disk affected by bprotect.exe with command.
ECHO Y|CHKDSK /X /F C:
Name: Deceiver’s bundle
Threat Assessment: High
Type: file bundling tool
Length: 2060299
System Affected: Win9x WinMe WinNT Win2000 WinXP Win2003
Hashes:
| MD5 | cb64441c0842f627e577b9df4caf0dbf |
| SHA256 | d115d1a186cf5f9ca7b74aad3701d599ac5d402c061b76fe04ccc53556e69864 |
Bprotect.exe releases virulent files and execute them in %WindowsDirectory%A__rd.exe. The files or pictures that bprotect.exe is about to bundle will be placed under c:msasn1 directory. The process would keep changing icon file names to dodge automatic removal. Then bProtect.exe starts to scan for documents in the target disk in an attempt to add some of its parts ahead of the .exe suffix or to icon files. As a result, new files are generated. The moment affected files are executed, the original vicious files will be removed, making it possible to successfully escape easy removal. What’s worse, the bprotect.exe issued by virus would trigger some bogus warning to make victims into believing that turning off firewall is a comparatively better option. Warnings can be:
Considering the fact that a target machine can be compromised by bprotect.exe, additional infections hold fat chance to infiltrate the system, which can complicate the situation and hinder removal. If it is the case that you are in, please do feel free to seek one-to-one help from VilmaTech Online Support according to your concrete situation.