Some undesirable scenarios happen after the installation of Websearch.wonderfulsearches.info, according to the data collected by VilmaTech Online Support:
Question thus arises – why getting websearch.wonderfulsearches.info will end up with these troubles? It is now that we are talking about the property and purpose of websearch.wonderfulsearches.info. Should you have any questions about websearch.wonderfulsearches.info, just start a live chat here for answers.
Websearch.wonderfulsearches.info is categorized as browser hijacker, also classified as PUP (Potentially Unwanted Program). In other word, it is not technically a virus instead an application that could introduce undesirable endings. Usually speaking, some modifications are injected to the JS computing technique that is inevitable to build a web page and that is the very technique assisting in the login of various accounts shortly without being asked to retype password, so that websearch.wonderfulsearches.info becomes capable of:
Every sticky item like websearch.wonderfulsearches.info targets at using its products or promoting other items. By doing so, it manages to generate income for the support of its normal operation. Websearch.wonderfulsearches.info is actually utilized to intercept and direct traffic.
By gathering more traffic, websearch.wonderfulsearches.info will attract many more online operators/advertisers to pay it for online marketing. By directing traffic to the designated web sites, it gets paid. This is why more unexpected programs will occur after the appearance of websearch.wonderfulsearches.info. Nowadays, browser hijacker like websearch.wonderfulsearches.info has been changed into online marketing tool.
It could be better to remove websearch.wonderfulsearches.info timely. First of all, the random installations of programs would take up the limited internal resource, which could hinder the effectiveness and agility of pivotal parts of a system that ward off potential threats.
Random modifications of system configuration for “permanent” stay would leave behind loophole. Should it happens, the JS computing technique will be utilized maliciously:
To safeguard personal information, it is recommended to remove websearch.wonderfulsearches.info when more and more unknown items get installed. Below is the removal thread to follow up. Should you get confused in the middle of the procedure, it is advisable to get specialized technical help from VilmaTech Online Support so that no mistake would be made to create new problems.
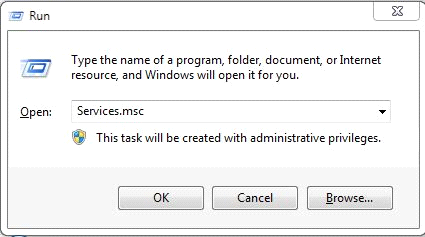
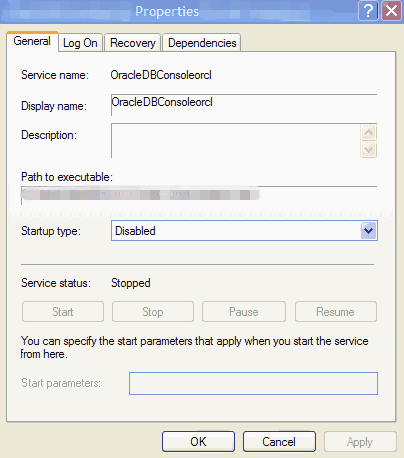
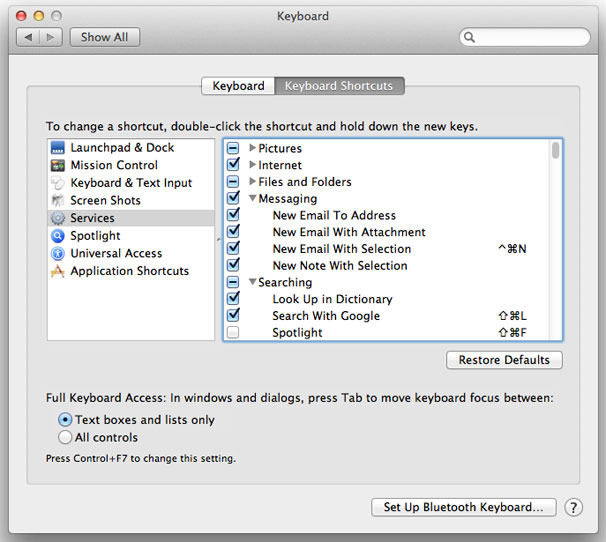
1. check the “Path to Executable” of the enabled services and to remove the ones with executable pointing to the browser hijacker.
Windows7/vista/XP
Windows 8
Mac OS X
2. restore your default homepage from websearch.wonderfulsearches.info.
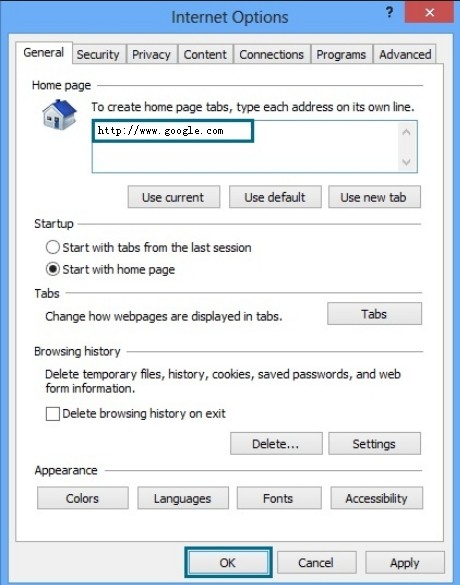
Internet Explorer
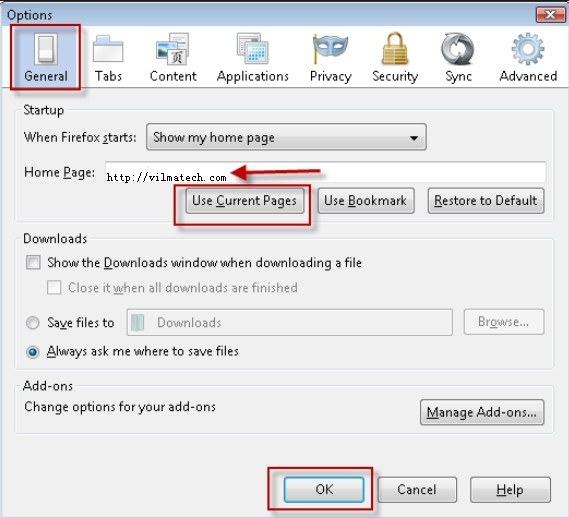
Mozilla Firefox
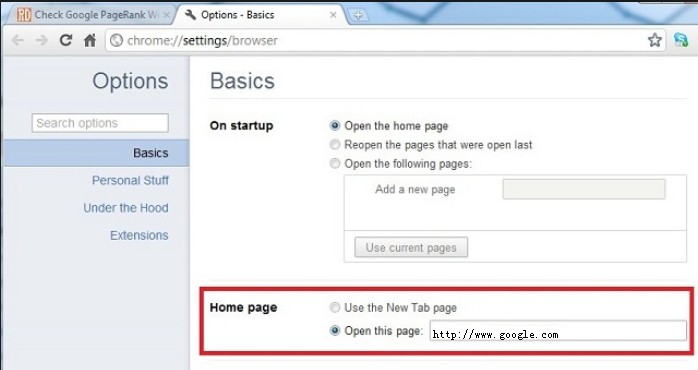
Google Chrome
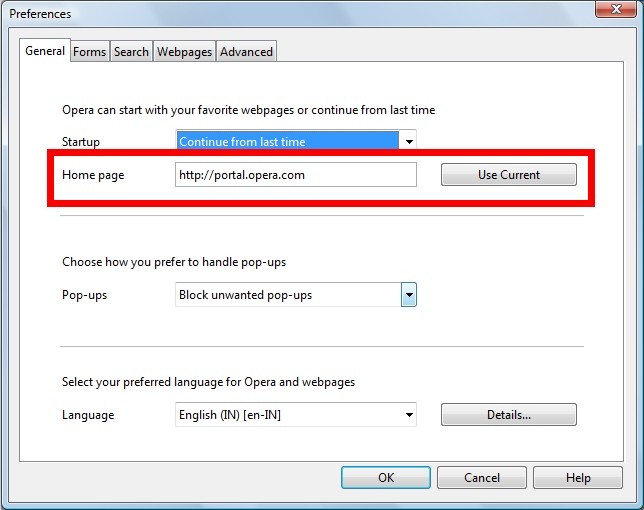
Opera
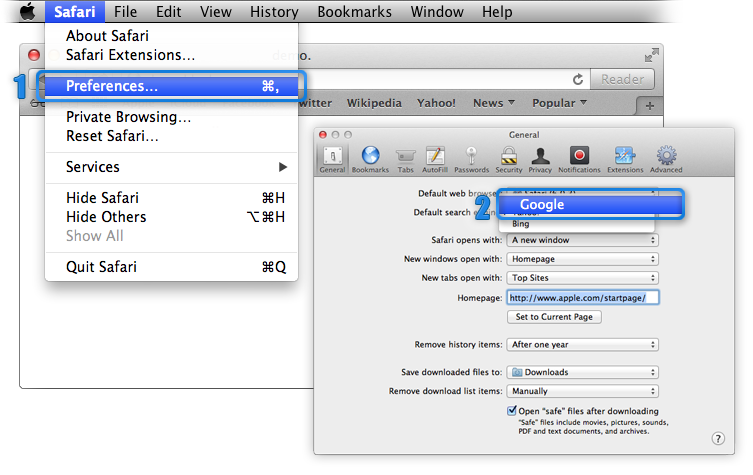
Safari
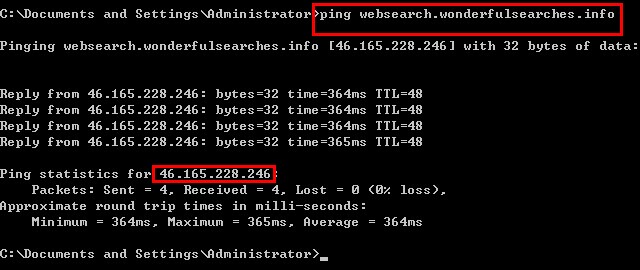
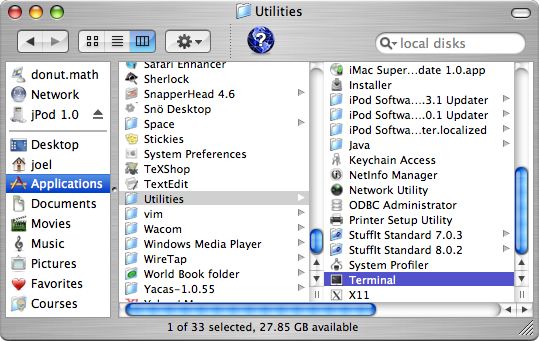
3. modify Hosts file to stop websearch.wonderfulsearches.info from hijacking.
Windows
Mac OS X
Many PC users reported that websearch.wonderfulsearches.info appeared all of a sudden, as a matter of fact it is the users’ negligence that allow websearch.wonderfulsearches.info in. Websearch.wonderfulsearches.info is a piece of freeware, it would bundle with third-party programs to spread as broad as possible without too much cost. On the occurrence of carelessness during the setup process of programs, websearch.wonderfulsearches.info could land on a target machine without being noticed.
Experts from VilmaTech Online Support would suggest give priority to ads-free programs. In the event that you have to download such program, please un-check the items recommended by the program. Any problems occurred during the removing session, just start a live chat for instant help.
As what has been made clear that additional items can worm into the same computer that websearch.wonderfulsearches.info harassed due to the cooperative ties, it is recommended to remove the dropped down items together with websearch.wonderfulsearches.info. Otherwise, there’s a big probability that websearch.wonderfulsearches.info stages back even after the accomplishment of the above given thread. Corresponding solution can be found in virus reservoir; still victims should get rid of the scattered files related to websearch.wonderfulsearches.info and the dropped down items for a better performance and safer system. It is time consuming to dig them out one by one. Here’s the video to show how: