CTB-Locker (Critoni) or Curve-Tor-Bitcoin Locker are the terms used by cyber criminals to describe one type of malware that attempts to extort a sum of money or Bitcoin from victim by infecting and taking control of the affected machine, including Android system. Thanks to its attributes, the CTB-Locker (Critoni) infection has been added to Microsoft security signatures called Critoni.A. Similar as TROJ_POSHCODER.A threat, upon its installation, the CTB-Locker (Critoni) virus will encrypt various types of files, documents, videos and images with an encrypted key and then asks victim to pay ransom for the keys to decrypt your data and unlock targeted PC as well as Android Phones. In reality, CTB-Locker (Critoni) can be recognized as a program, carrying executable code embedded in the malware’s body that has the capabilities to damage a user’s computer. Unlike common ransom virus, CTB-Locker (Critoni) virus is the first cyptomalware that uses the Tor network to annonymize its communication with the command and control server. Before reaching the Command and Control Server, the infection can make it undetectable as the ransomware commands go through the several layers of Tor anonymiser setup.
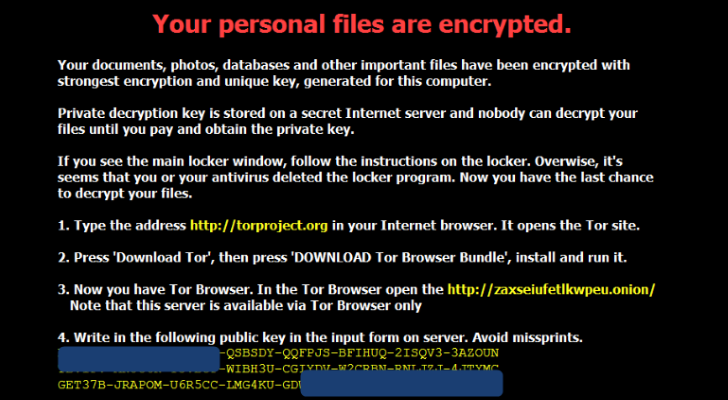
Critoni ransomware is known as Curve-Tor-Bitcoin Locker because it may allow cyber crooks to mint bitcons through innocent victims of Critoni.A. In some scenarios, CTB-Locker (Critoni) ransomware may directly require victims to pay ransom in bitcoins in order for the restriction to be removed and encryption to be decrypted. If so, the infection will usually give a tutorial on how to obtain bitcoins through the market criminals have. Accomplished with a Tor.exe file in its body, CTB-Locker (Critoni) infection may automatically self-deletes itself once the period of time set for making the ransom payment expires. As a result, malware distributors would get another chance to retrieve the data from victims. Usually, there will be a TXT file located in the Documents folder as instruction. No matter how authentic CTB-Locker (Critoni) information seems to be, one fact every victim should know is that CTB-Locker (Critoni) or Curve-Tor-Bitcoin Locker is only one type of hazardous malware that is capable of making hazards on affected machine, and users should eliminate the virus timely so that to decrypt their encrypted data and unlock affected machine as good result.
Note: To get rid of CTB-Locker (Critoni) Ransomware, you may adopt the helpful manual removal. Any problems during the operation, you are welcome to ask help from VilmaTech Certified 24/7 online expert here , who will be glad to help you out of trouble.
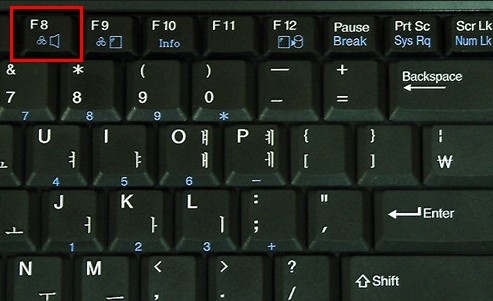
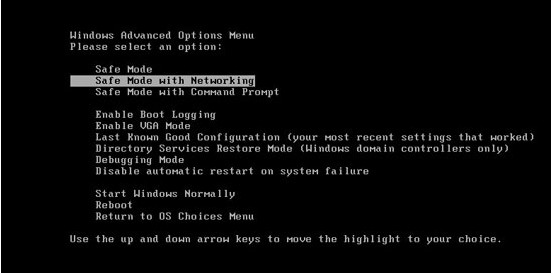
Thanks to its Tor network technology, CTB-Locker (Critoni) ransom virus can always bypass the detection by antivirus software applications as well as other security tools. In some serious conditions, victims may not able to do anything in normal mode. In consequence, you may consider the almighty manual approach to completely get rid of all components of CTB-Locker (Critoni) infection for good. If you are not familiar with the process, you’d better backup windows registry in case of potential mistake, or directly live chat with VilmaTech Certified Computer Experts here for real-time support. Here is the step by step manual removal help:
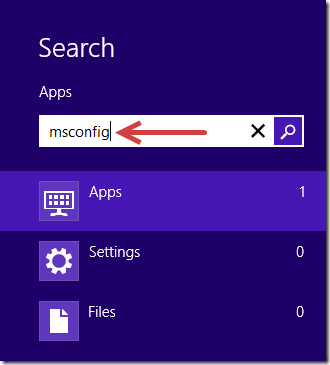
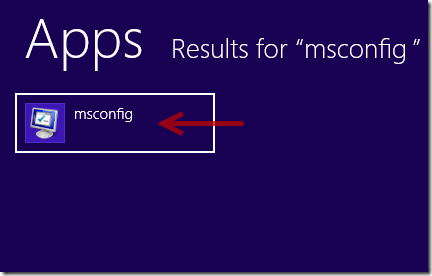
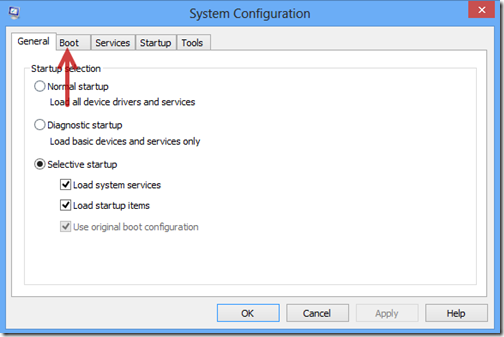
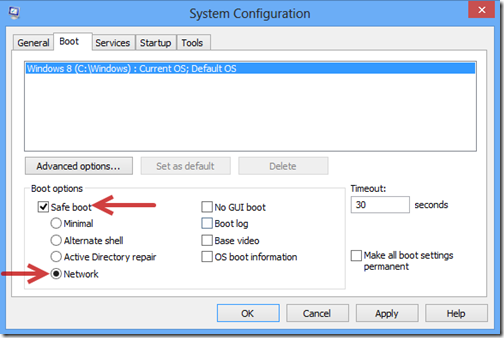
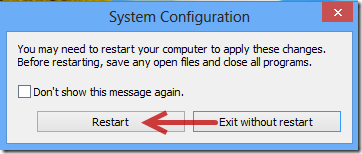
1. Boot your computer into Safe Mode with Networking.
2. Clean up all the components of CTB-Locker (Critoni) Ransomware in your computer.

%Temp%\[RANDOM CHARACTERS].exe
C:\Documents and Settings\<Current User>
C:\Users\<Current User>\AppData\
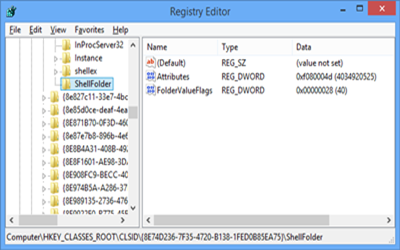
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System “DisableTaskMgr” = 0
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run\random
CTB-Locker (Critoni) or Curve-Tor-Bitcoin Locker is a destructive ransom virus designed by cyber criminals to damage affected computer/Android Phones and gain from victim. Most commonly, the infection can always permeate onto a user’s computer via different dishonest ways via compromised websites, spam email message or some “free” applications carrying out the activation code of the virus which are specifically shared on networks. Once being installed, the CTB-Locker (Critoni) or Curve-Tor-Bitcoin Locker infection will make use of its programmed code to make chaos on affected computer and connect remote command and control server with the aid of Tor network technology. Usually, the infection will encrypt user’s personal files such as documents, photos, databases and other important files with strong encryption and unique key, generated for the computer. To obtain the unique key, the ransomware would demand you to pay in money or bitcoims. It is certain that CTB-Locker (Critoni) or Curve-Tor-Bitcoin Locker is only a computer virus that should be removed from computer and Android devices as long as being noticed of its presence. However, auto removal by antivirus may have a very low chance to get rid of the infection. In this case, you may consider the helpful manual removal to clean up all its components permanently.
If you have no experience on the manual approach, and do not want to make mistake, you may start a live chat with VilmaTech Certified 24/7 online agent here to get professional tech help.