Websearch.wisesearch.info is categorized as a hijacker that mainly propagates through downloads from Internet and LAN (Local Area Network) as well as portable storage device. Such kind of virus has been widely used to help its cyber makers to gain huge profit by hijacking primarily default homepage and navigate web sites to forcibly popularize vicious partner sites where would produce rogueware, commercial pop-up ads, and Trojan.
Generally speaking, victims of websearch.wisesearch.info hijacker are those who run computers with low safety coefficient to download and install program by recommended manner and to open up links contained in spam or poisoned emails. Once websearch.wisesearch.info gets into a system, it drops its malevolent file and copies it to system directory, i.e. %System%. To well prevent its virus items from being easily detected, websearch.wisesearch.info hijacker generates running process to set its files to be hidden and make their attribute as system files, leaving victims impossible to dig out virus files even after ticking ‘Show hidden files, folders, and drivers’ in ‘Folder options’. Such protective measures are far from sufficient to perfectly hide itself up, websearch.wisesearch.info hijacker will then exterminate the activities of original virus file and make its copies to release URL shortcut in C Disk.
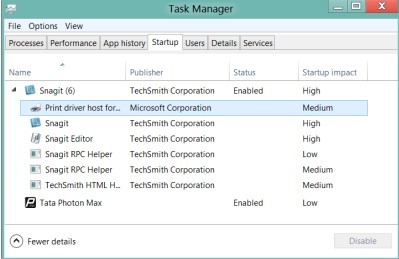
Other executable files will be copied to Startup section to ensure its auto-startup when the computer is running. Be noted that websearch.wisesearch.info hijacker is a crafty virus that it generates items similar or even identical to system ones, for example, svchost.exe, which in normal case is the general name for host process running from DLL (Dynamic Link Library), cannot be exterminated. A normal svchost.exe is usually placed under ‘%system root%\system32’ with notes, visible window for the according program; otherwise, it is fraudulent, being utilized to monitor applications, keylogging, connect automatically to the Internet, and help manipulate other programs. The last but not least, websearch.wisesearch.info hijacker will modify database by copying handles of the items inserted into the startup section to winlogon.exe in a bid to hindering deletion unless winlogon.exe is exterminated.

Add-on as websearch.wisesearch.info is, it is capable of incurring troubles since add-on is not the source of the below evil conducts:
◆ Hijack default homepage and web search.
◆ Trigger in-page pop ups during browsing session.
◆ Slow down overall PC performance.
◆ Slice down page-loading speed.
◆ Install additional cookies and plug-ins like toolbar without consent.
In fact, a folder under C: Windows with a long series of numbers and letters is the source of the above listed troubles. By releasing files of various types into systematic registry entries to help consolidate forcible modifications in an attempt to block rectifications that can help victims remove websearch.wisesearch.info easily, the hijacker manages to make the target machine become susceptible to other deadly virus, including ransomware. Therefore, one should hurry up to remove websearch.wisesearch.info hijacker for the sake of computer health. Given the fact that the folder resembles other normal temp files, websearch.wisesearch.info is not able to detect by installed security utilities, no matter how reputable they are, it is highly recommended to remove websearch.wisesearch.info hijacker manually.

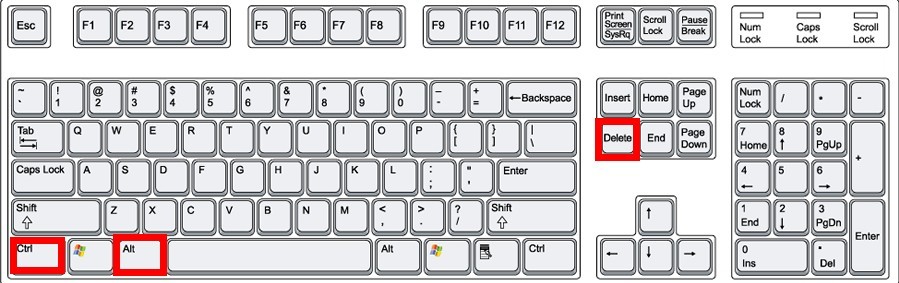
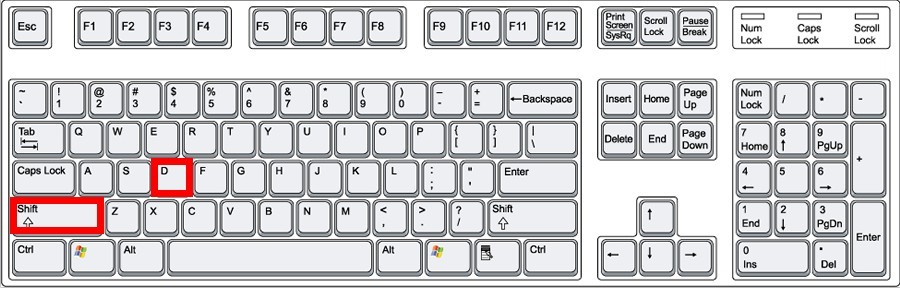
Step one – Exterminate running process related to websearch.wisesearch.info so as to make the subsequent rectifications smoothly.
◆ Windows 8
◆ Windows 7/Vista/XP
Should one encounter error when attempting to end process, one should follow up the instructions here:
◆ Windows 8
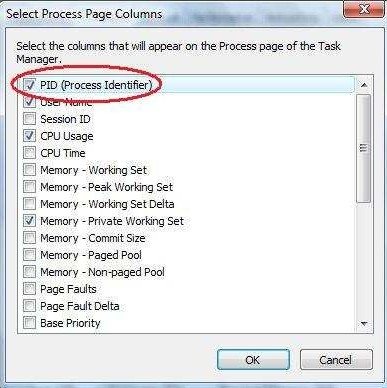
◆ Windows 7/XP/Vista
→ follow the same process as depicted above.
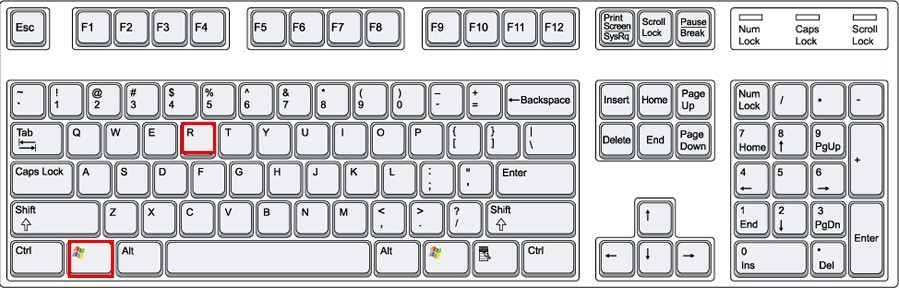
Step two – Remove startup item of websearch.wisesearch.info hijacker.
◆ Windows 8
◆ Windows 7/Vista/XP
Step three – Modify configurations back to normal on infected browser manually to remove websearch.wisesearch.info hijacker directly.
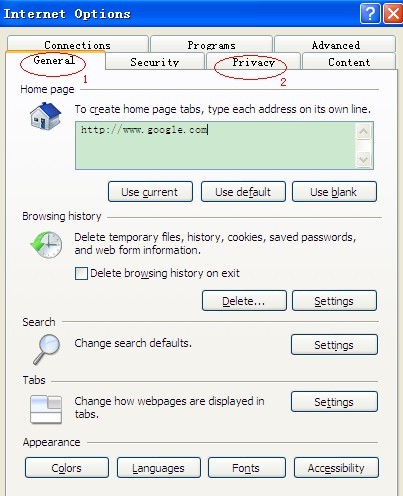
◆ Internet Explorer:
Empty out browse history.
Select ‘Search’ section to ‘Manage Add-on’ window and heck ‘Toolbars and Extensions’ and then ‘Search Providers.
Locate ‘Tabs’ section to ‘Tabbed Browsing Settings’ and uncheck ‘Always switch to new tabs when they are created’ before pressing ‘OK’.
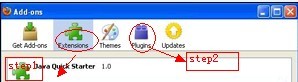
◆ Mozilla Firefox
◆ Google Chrome
Step four – Remove all suspicious files under C: Windows and System32 to thoroughly remove websearch.wisesearch.info hijacker.
◆ Delete all executable files identical to systematic ones, such as svchost.exe and winlogon.exe in sub-directories under C: Windows.
◆ Remove temp folders under System32.
Step five – Empty out Dustbin to make sure that websearch.wisesearch.info will not come back again.
There have been not a few cases that people get virus coming back again because of the leftovers in Dustbin. One should remember to right click on Dustbin on the desktop to select ‘Empty Dustbin’.
Step six – Restart the infected computer and back to desktop normally to check if you successfully remove websearch.wisesearch.info hijacker.

If error message prompts up after reboot to tell that files cannot be found, it is telling you that there still are registry keys being modified by websearch.wisesearch.info. One may follow the steps below to rectify the database.
◆ Windows 8 users to follow up
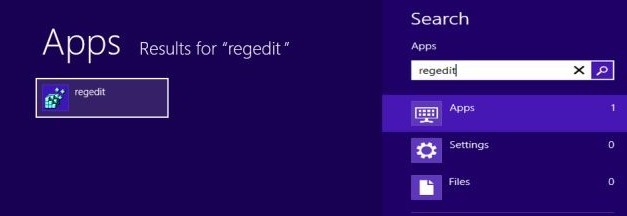
→
For IE users:
HKEY_CURRENT_USER\ Microsoft\Internet Explorer\
to find and select items related to websearch.wisesearch.info and then right click on selected item to delete it.
For Google Chrome users:
HKEY_LOCAL_MACHINE\SOFTWARE\Google
to find and select items related to websearch.wisesearch.info and then right click on selected item to delete it.
HKEY_CURRENT_USER\Software\Google\Update
to find and select items related to websearch.wisesearch.info and then right click on selected item to delete it.
HKEY_CURRENT_USER\Software\Google\
to find and select items related to websearch.wisesearch.info and then right click on selected item to delete it.
For Mozilla Firefox users:
HKEY_CURRENT_USER\ Microsoft\Mozilla\ Firefox
to find and select items related to websearch.wisesearch.info and then right click on selected item to delete it.
HKEY_CURRENT_USER\ Microsoft\MozillaPlugins
to find and select items related to websearch.wisesearch.info and then right click on selected item to delete it.
HKEY_LOCAL_MACHINE\SOFTWARE\MozillaPlugins
to find and select items related to websearch.wisesearch.info and then right click on selected item to delete it.
◆ Windows 7/XP/Vista users to follow up
→ follow the same process as shown above for Windows 8 users.
Notes:
Hijackers like websearch.wisesearch.info is capable of affecting flash drive by mounting autorun file so as to affect more computers once it is used to other computers without bothering PC users to run the vicious file. Bear in mind to always keep installed security utilities running on the computer infected with websearch.wisesearch.info hijacker no matter what prompt-up message telling that some conflict happened and that installed security utilities should be switched off. Once you do so, installed security utilities will be disabled completely and safe mode will no longer be able to help remove websearch.wisesearch.info by stopping its malicious part from reproducing smoothly shortly after some parts are exterminated successfully. Instead, it would give BSOD (Blue Screen of Death). Stick to the steps above that have been tested to be applicable to many situations. However, exceptions can happen should there be abnormal items left in a system without being recognized. If you are overwhelmed by websearch.wisesearch.info hijacker and other associated problems, you are welcome to ask for solutions tailored to your concrete situation by starting a live chat here.
