Lpcloudbox410.com belongs to the adware team which could make profits by releasing tons of disturbing pop-ups to the targeted users, regardless of their feelings. In most cases, the Lpcloudbox410.com had to firstly infect the computer by using improper means and also hid so well from the innocent users, in this way, even the system was seriously infected by the Lpcloudbox410.com or any malware it introduced, the victims could never detect them until things got serious in the computer. Once the Lpcloudbox410.com had its way by infiltrating into the targeted system, it would have the ability to mess with the computer and make some malicious modifications in system so as to achieve its evil purposes. Since Lpcloudbox410.com successfully stationed in the computer, the users could receive a mass of pop-ups from the browser or the computer corners as long as they turned on the computer.
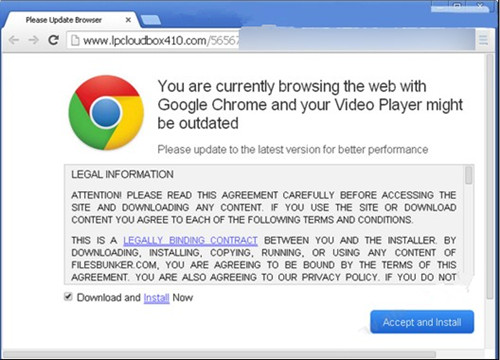
Most of the strange pop-ups displayed by Lpcloudbox410.com were related to various updates or downloads, which made the innocent users so confused. In this case, there were plenty of Internet users choosing to follow the command and giving their permission to those unknown installation requests, unconsciously waking into the traps set up by Lpcloudbox410.com. As some of the users made a mistake of thinking that updating the system applications was not so bad, at lease not harmful for the computer. However, Lpcloudbox410.com just took advantage of the occasion to lure the innocent users to download those so-called update software, secretly introducing malware and implanting malicious codes into the system to make more damages to the computer. Because, there were still so many Internet users lacking of precaution awareness while encountering unfamiliar download prompts or requests, permitting them without thinking and letting cunning Lpcloudbox410.com and also cybercriminals have the opportunity to threaten the system security.
Just as Lpcloudbox410.com has added more and more unwanted malware or viruses into the computer without scruples, not only the system resources were completely occupied by all the invaders, the computer performance and operation would be serious affected. Users might suddenly find the loading speed was decelerated, and the strange system prompts showed up frequently to notice them about unknown errors and failure. As the Lpcloudbox410.com has rest some critical system settings maliciously, the computer protection was gradually weakened and corrupted. Under this circumstance, the damaged system could be unable to defense itself or prevent malicious attacks any more. In this case, all the personal files and confidential data remaining in the computer would be put in danger. With no comprehensive protection in the computer, evil cybercriminals and hackers could easily break into the system, searching for all the valuable files and data in the computer and stealing them freely, the consequences could be disastrous. Users have to remove Lpcloudbox410.com as soon as possible and repair the computer immediately.
Please feel free to click on the button whenever you need help from the VilmaTech Online Experts.
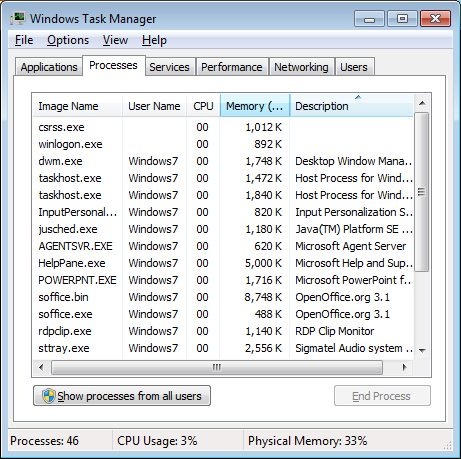
1. Disable the related processes of Lpcloudbox410.com from the background then launch the browser.
Press the Ctrl+Alt+Del keys at the same time to open the System Task Manager then click on the Processes tab, select all the running processes of Lpcloudbox410.com from the list then disable them one by one.
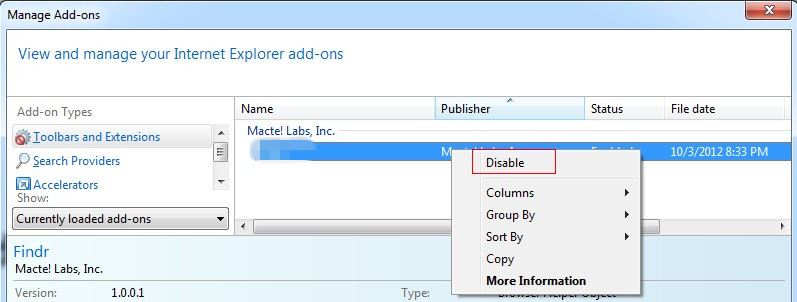
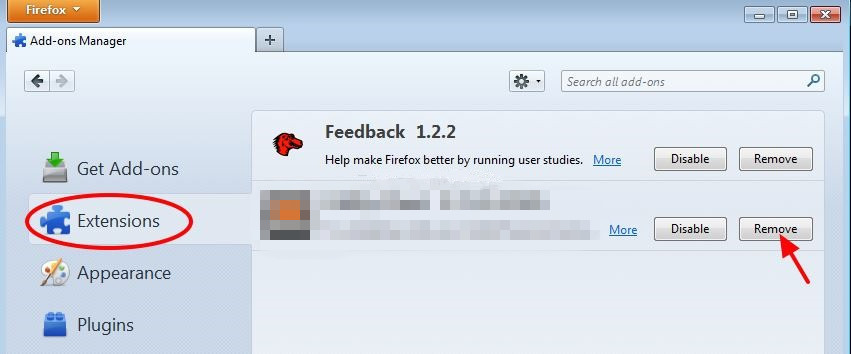
2. Remove the Lpcloudbox410.com extensions from the browser immediately.
Click on Tools-> click on Manage Add-ons-> find Lpcloudbox410.com from the Toolbars and Extensions section-> right-click on it-> choose the Disable from the pop-up menu.
Click on the Add-ons from the Firefox menu-> search for the Lpcloudbox410.com from the Extensions list-> select it then click on the Remove button.
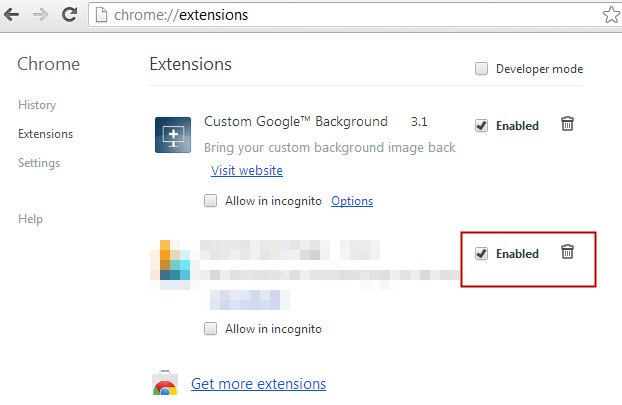
Click on the wrench icon-> locate Tools-> click on Extensions-> select Lpcloudbox410.com from the list-> click on the bin icon.
3. Restart the browser once finished the removal.
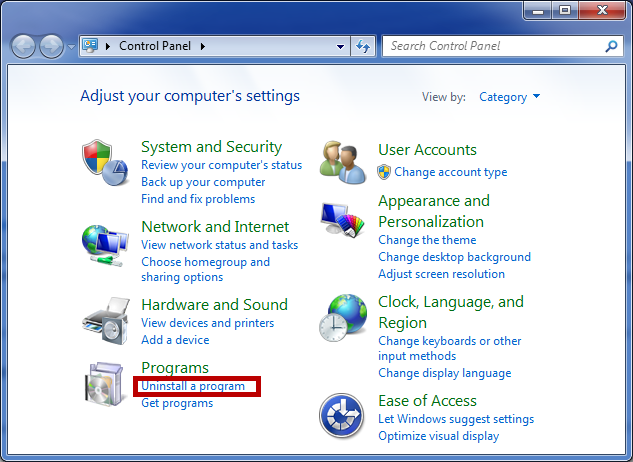
1. Open the Control Panel from the Start menu then click on the Uninstall a Program link to show the Programs and Features list.
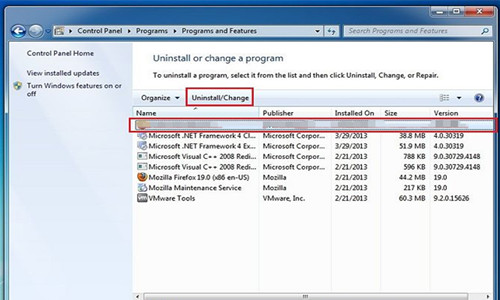
2. Find out the related programs of Lpcloudbox410.com from the programs list then click on the Uninstall on top column and follow the uninstall wizard to remove it completely.
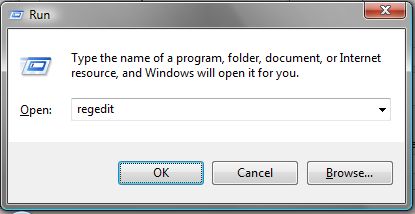
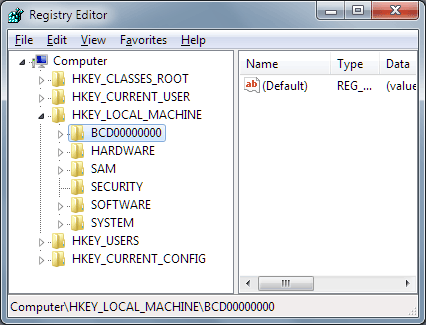
1. Open the Run from the Start menu then type “regedit” command in the Run search box then click on the OK button to search for the Registry Editor from the system and open it.
2. Find out the related registry entries and keys of Lpcloudbox410.com from the Registry Editor branches then remove them thoroughly.
3. Once finished the Lpcloudbox410.com removal, reboot the computer at once to let the changes take effect.
Lpcloudbox410.com and all the similar virus could be everywhere on the Internet, waiting for the next victim to get infected. As there are still more Internet users haven’t form the good online habits or build precaution awareness, letting the malware and virus have the chance to fool them and also cause unexpected losses. In order to have a safe and nice Internet environment, users have to learn to be prepared for malicious attacks and virus infections on their own. Have to know that most of the unwanted programs even malware are coming from unknown installation packages. Most of the unsafe bundled downloads are released from sharing sites or corrupted free sites, once the users blindly visited this kind of trap websites and downloaded any program from them, malicious virus would get the opportunity to be downloaded and installed together into the targeted computer without awareness. So, users should resist freeware or shareware from unfamiliar websites or resource station, and always choose needful software from official sites with credits. In the mean time, users should detect any new download files before using them, just in case to leave out any suspicious software and end in being seriously infected. If you want to learn more useful methods to prevent virus and malware from invading into your computer, please click on the button and have a chat with the VilmaTech Online Experts.
*Here is a guide to help create a restore point on your own.