Are you looking for a verified Proton VPN Coupon Code? If so, you’ve come to the right place. Here we will show you on how to get 55% off Proton VPN coupon code on 2-Year plan at Proton VPN. Fake discount codes for VPNs are everywhere online, so many users don’t know where to get the real Proton VPN coupon code. They spend most of time trying to save money, but finally none of them work properly. Here, we offer the latest VPN coupon codes for our readers. Any readers on our site can have a chance to grab the 55% off Proton VPN coupon code of the year. This is the best value you should never miss out. Learn more below on how to take this special offer.
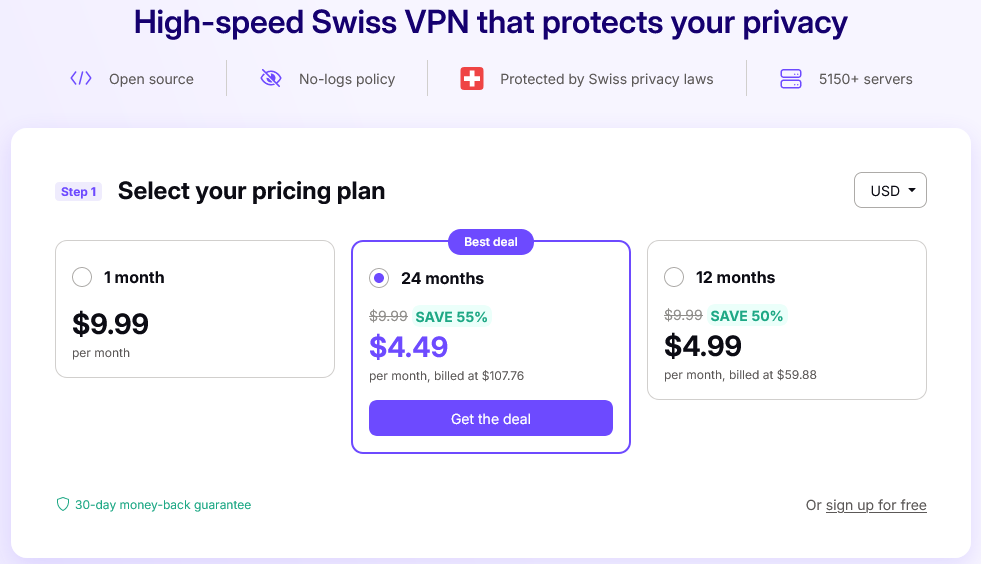
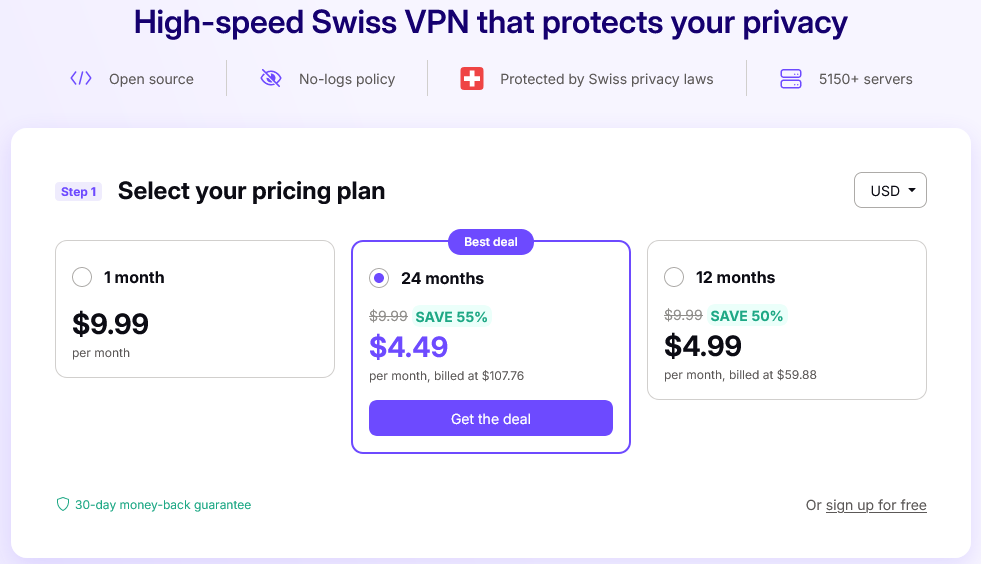
Proton VPN, based in Switzerland, is a competent and remarkable VPN service that offers both VPN & proxy service to protect your online privacy and lets you stay anonymous whenever you are online. Currently, Proton VPN is running a big promotion for every new user. You can grab 55% discount coupon code, promo code to save big on your purchase if you go with Proton VPN for 2 years, and save 50% on the 1-year plan. Usually, it costs US $9.99 a month to get you into the Monthly plan. Every plan includes VPN access to 5,127 servers in 91 locations. But now, with 55% discount it only costs you $4.49/month, and save 55%! Do remember the Proton VPN special offer for $4.49/month only deal is available only for a limited time! Don’t miss out on the biggest discount on Proton VPN. Enjoy amazing deal from Proton VPN here!
Proton VPN is a privacy-focus VPN service supplier based in Switzerland. It is operated by experienced and skill staffs and engineers from Asia, Africa and Europe, which offers 24/7 attentive support service for customer across the globe. Proton VPN provides 300+ servers in over 57 countries, which almost spread throughout the world except in locations where privacy is not fully ensures at the moment. Proton VPN offers incredibly discreet, fast and secure as well completely private VPN speed connection. All servers hide IP address (Internet identity) and location from unwanted sights without leaving traces either on the Internet or here at our shop. Proton VPN is empowered with strong encryption standard which is made up of 256-bit AES/CBC, SHA-512 and 4096-bit RSA as cipher/hash/control. It offers 100% non-logging servers. All services are set to never log a single bit of information and most of them are running into RAM. OpenVPN network is designed as default protocol maintained with great standards. Proton VPN regularly develops new encryption & features to their VPN, like Ad-blocker and Stealth protocol. A great variety of proxy technologies are supplied to adjust to all situations and operating systems. Proton VPN engineers their own client app called Proton VPN which is easy-to-use and also compatible with major platforms like Windows, Mac, iOS, android, Linux and more.

Proton VPN package comes at 3 different prices: USD $9.99 for 1 month, USD $4.99/month if billed for 2 years, USD $4.99/month if billed for 1 year. The yearly prices offer generally quite an interesting discount. The difference of prices mainly corresponds to billed terms you’re willing to use. It is also important to note that all these Proton Plus packages include all the features, except the free package if you’re willing to try it. All packages include unlimited bandwidth, OpenVPN, Extras (DNS, TOR, SOCKS, etc.).
The Proton VPN plus packages are specifically built for demanding users and professionals. It provides access to one of the largest VPN network with 5,127 servers in 91 locations. It will give you a fast and stable access to major Internet services and content delivery networks. It also comes with access to Proton VPN Multi-Hop technology and the huge Proton VPN Network (U.S. West, East, South, UK, Germany, Japan & Singapore, and others).
1. Go to Proton VPN homepage, click on Pricing tab
2. Select your favorite plan, take 2-year plan for example, which is selected by default.
3. Enter your login details.
4. Finally, select your preferred PAYMENT METHOD, and Complete Order.
Proton VPN is happy to offer a full refund for any order as long as your payment method allows it. If you’re not happy with it, they will issue an immediate refund, no question asked.
Proton VPN provides a strongly-encrypted VPN network & online infrastructure that are all set to never log anything. It is ‘no logs’ VPN service. So, in any cases Proton VPN VPN will never monitor or log your session data, web history, data transfer, or connection history. However, it collects your email address to send you subscription information and payment confirmations, and Google Analytics data to improve their website.
Proton VPN provides strong encryption standard to guarantee complete security and privacy for customers. All Proton VPN VPN servers are powered with powerful protocols configuration as follows:
– OpenVPN-TCP: The cipher used by OpenVPN-TCP is CBC mode of ARS with encryption strength of 256bit, hash algorithm is 512bit SHA (SHA512). And the control channel is same TLSv1/SSLv3 DHE-RSA-AES256-SHA, 4096 bit RSA. Proton VPN’s 4096 bit RSA key is changing every hour, preventing most advanced hackers and covert teams part of governmental agencies from breaking through.
– OpenVPN-UDP: OpenVPN-UDP is equipped with the same encryption and security level as OpenVPN-TCP, but it works via UDP protocol which allows better speeds and bypasses more restrictions.
– OpenVPN with ECC: It uses Diffie-Hellman initialized with 4096-bit key along with ECDH curve secp384r1 to encrypt. Its full control channel is made of TLSv1.2, cipher TLSv1/SSLv3 ECDHE-ECDSA-AES256-GCM-SHA384. Moreover, this protocol combines encryption cipher AES-256-CBC and the auth SHA512 to make the whole combination one of the strongest known to cryptographic research field. This ECC environment works well on port 465 (both UDP and TCP).
– OpenVPN with ECC+XOR: Almost the same encryption level with ECC, it also uses Diffie-Hellman initialized with 4096-bit key along with ECDH curve secp384r1. Its full control channel is made of TLSv1.2, cipher TLSv1/SSLv3 ECDHE-ECDSA-AES256-GCM-SHA384 while associated with cipher encryption AES-256-CBC and the auth SHA512. Furthermore, this environment is supplemented with OpenVPN’s XOR scrambling option, which makes the whole combination probably the strongest known to cryptographic research field. “ECC + XOR” environment are provided on port 995 (both UDP and TCP).
– OpenVPN with TOR’s obfsproxy: It makes use of our default encryption for OpenVPN along with obfsproxy on port 888 (both UDP and TCP). Proton VPN offers obfs3, obfs2 and obfs3, obfs2 as obfsproxy standards.
– PPTP: PPTP uses MPPE 128bit cipher with compression and MS-CHAPv2 authentication.
– L2TP: L2TP is using IPSec for encryption with 256 bit key for encryption, 3DES/AES.
Proton VPN proudly serves you with the highest standards in VPN cryptography. The standard WireGuard, OpenVPN is running 256-bit AES/CBC, SHA-512 and 4096-bit RSA as cipher/hash/control. It also provides ECC and Serpent as extra encryption methods, as well as XOR and TOR’s obfsproxy for scrambling your traffic. Proton VPN supplies a great variety of proxy technologies to adjust to all situations and operating systems.
1. Advanced Encryption Standard – Elliptic Curve Cryptography (ECC)
Proton VPN offers a higher standard of encryption on its network. The higher encryption ECC has been as part of Proton VPN VPN’s network encryption standards. ECC encryption standard is coupled with a 4096-bit Diffie-Hellman key, and the curve is ECDH secp384r1. The full control channel is made of TLSv1.2, cypher TLSv1/SSLv3 ECDHE-ECDSA-AES256-GCM-SHA384 while the associated cypher is AES-256-CBC and the auth SHA512, making the whole combination one of the strongest known to the cryptographic research field. This ECC environment is provided on port 465 (both UDP and TCP). It is easy to use ECC when you use Proton VPN’s custom OpenVPN client called Safeiumper. Proton VPN also provides OpenVPN with 256-bit AES/CBC, SHA-512 and 4096-bit RSA as cipher/hash/control.
2. Integration of TOR’s Obfsproxy within Its OpenVPN Network and Its VPN Client Configuration
TOR’s obfsproxy is also called Stealth VPN. Proton VPN integrates TOR’s obfsproxy with its OpenVPN network and its VPN client configuration – Safejumper. Obfsproxy is an obfuscation program that will scramble, or if you prefer, disguise your traffic to make it undetectable to firewalls and governmental monitors. It is what makes TOR users undetectable unless you monitor the exit nodes. Tor is an effective censorship circumvention tool, allowing its users to reach otherwise blocked destinations or content. Tor can also be used as a building block for software developers to create new communication tools with built-in privacy features.
Obfsproxy has a strong capability to bypass the detection and filtering of anti-VPN tools, internet censorship and government monitors. Therefore, Proton VPN becomes strong and powerful to survive in some regions or nations where practice strict internet censorship like China, India, UAE. Take China for example, it carries out the strictest and strongest internet censorship in the world and implements thousands of anti-VPN tools together with strict laws and regulations. Many low-quality VPNs cannot survive in China. However, with Obfsproxy feature, Proton VPN become strong and unbreakable. You can use Proton VPN in China and other internet-censored countries.
TOR’s obfsproxy not only can strongly bypass the detection of the strictest internet censorship but also keeps users enjoy complete privacy and security on the internet. users can use TOR’s obfsproxy to stop websites from tracking them and their family members, or to connect to news sites, instant messaging services, or the like when these are blocked by their local Internet providers. Tor’s onion services let users publish web sites and other services without needing to reveal the location of the site.
3. Remarkable ECC+XOR Combo
Proton VPN provides XOR in exclusivity with ECC. The latter allows you to make sure your traffic will be next to impossible to decipher, while XOR allows you to make sure the third party cannot detect you are using OpenVPN. XOR obfuscation option is perfectly added into OpenVPN network. ECC+XOR patch adds obfuscation capability to OpenVPN, allowing it to bypass network traffic sensors which aim to detect usage of the protocol and log, throttle or block it. But this patch is not designed to enhance or replace the existing encryption functions within OpenVPN and thus it should not be used for this purpose. So, Remarkable ECC+XOR Combo lets you alter the “look and feel” of the traffic that goes between your devices and our VPN network, making it more difficult for any external watchers such as network administrators or governmental agencies to detect you are behind a VPN.
4. Outstanding SoftEther VPN
SoftEther VPN (“SoftEther” means “Software Ethernet”) is one of the world’s most powerful and easy-to-use multi-protocol VPN software. It runs on Windows, Linux, Mac, FreeBSD and Solaris. SoftEther VPN is an optimum alternative to OpenVPN servers. SoftEther VPN has a clone-function of OpenVPN Server. You can integrate from OpenVPN to SoftEther VPN smoothly. SoftEther VPN is faster than OpenVPN.
SoftEther VPN is not only an alternative VPN server to existing VPN products (OpenVPN, IPsec and MS-SSTP). SoftEther VPN has also original strong SSL-VPN protocol to penetrate any kinds of firewalls. Ultra-optimized SSL-VPN Protocol of SoftEther VPN has very fast throughput, low latency and firewall resistance.
SoftEther VPN has strong resistance against firewalls than ever. Built-in NAT-traversal penetrates your network admin’s troublesome firewall for overprotection. You can setup your own VPN server behind the firewall or NAT in your company, and you can reach to that VPN server in the corporate private network from your home or mobile place, without any modification of firewall settings. Any deep-packet inspection firewalls cannot detect SoftEther VPN’s transport packets as a VPN tunnel, because SoftEther VPN uses Ethernet over HTTPS for camouflage.
5. Trusted Multi-Hop Technology
The Multi-Hop technology will let you connect to any VPN server as entry point, and then it will randomly route you through various VPN nodes across our network up to your selected exit point which will become your public IP.
6. Flexible SOCKS5
Socket Secure (SOCKS) is an Internet protocol that exchanges network packets between a client and server through a proxy server. SOCKS5 additionally provides authentication so only authorized users may access a server. Practically, a SOCKS server proxies TCP connections to an arbitrary IP address, and provides a means for UDP packets to be forwarded.
SOCKS5 is a unique proxy because it’s made for handling data from anywhere — any protocol, any program, and any type of traffic. So, you can be sure that our SOCKS5 feature will maintain your privacy in nearly any program you configure it with, whether it be for torrents, VoIP, or even your web browser!
Using SOCKS5 is a great option if the main goal is downloading torrents and P2P. It is also a secure option if you are not browsing the net– as SOCKS5 codes your traffic via proxy server. Alternatively, use a mix of VPN and SOCKS5, as VPN service is highly recommended for multiple online data operations, online privacy and enhanced security. SOCKS5 easily helps you bypass internet blockades and firewalls as your IP address is hidden from the firewall or the internet censor. The IP address of the proxy server is visible, which is usually in a location where the blocked service is available.
Therefore, Proton VPN with SOCK feature has a more powerful functions to bypass internet censorship and access all geo-websites like Netflix and Hulu. It allows you to torrenting and P2P file sharing without any worry.
| VPN Services | Servers | Country | Connections At Once | Price (USD) | Official Website |
|---|---|---|---|---|---|
| NordVPN |
6,390 in 111 locations | Panama | 10 | $3.09/month 74% off & 3 months free | Get this deal |
| IPVanish |
2,400 in 90 locations | USA | Unlimited | $2.19/month 84% off & 3 months free | Get this deal |
| ProtonVPN |
5,127 in 91 locations | Switzerland | 10 | $4.49/month 55% off | Get this deal |
| Surfshark |
3,200 in 100 locations | Netherlands | Unlimited | $2.19/month 86% off & 3 months free | Get this deal |
| PIA |
29,650 in 91 locations | USA | Unlimited | $1.98/month 83% off & 4 months free | Get this deal |
| CyberGhost |
11,690 in 126 locations | Romania | 7 | $2.19/month 86% off & 3 months free | Get this deal |
| Ivacy |
5,700 servers in 100 locations | Singapore | 10 | $1.17/month | Get this deal |
hide.me |
2,600 in 90 locations | Malaysia | 10 | $2.69/month 2 months free | Get this deal |
| VPN.AC |
130 in 31 locations | Romania | 12 | $4.8/month 46% off | Get this deal |
| PureVPN |
6,000 in 80 locations | British Virgin Islands | 10 | $2.14/month 82% off | Get this deal |
AirVPN
|
24 locations | Italy | 10 | $2.42/month 68% off | Get this deal |
StrongVPN |
950 in 30 locations | USA | 10 | $3.97/month 66% off | Get this deal |
Proton VPN gives you access to a VPN network that is operated with state-of-the-art standards in encryption, quality & transparency. Its network spans all around the world and is hosted on nodes where all services are running from live memory (RAM). Shutting down the node erases all software setup and all Proton VPN services are set to non-logging. Proton VPN provides several hundreds of VPN nodes running through various ports and with various protocols such as TOR or ECC/XOR to make sure you are able to unblock everything you wish to access online.
Warm TIPS: Proton VPN is now offering the biggest discount 55% off Proton VPN coupon code for all customers all around the world. The 55% off 2-year plan is a limited-time offer. With the valid code, you can enjoy the lowest cost but enjoy the high-quality Proton VPN service and experience complete security and privacy on the internet all the year round! Don’t miss out on the biggest discount at the moment!