Rector Ransomware is malicious virus that has attacked a lot of online users’ computers, compromising credentials and other confidential information. After being out of the spotlight for a while, the Rector ransomware has been regarded as one of the most malicious threats that focus on blocking PCs, damaging system, stealing sensitive user information, and more. So far, Rector ransomware has patched a series of Trojan viruses that allow hijackers to completely compromise the targeted PC and execute arbitrary code, just such as the hazardous virus called Trojan/Win32.Rector.A, Trojan-Ransom.Win32.Rector, Trojan:Win32/Orsam!rts, and more. And they can carry out incredible damage one the targeting compromised system, including PC, Android phone, Android Tablet, and many others. In most cases, the Rector Ransomware is able to identify a heap buffer overflow vulnerability on the targeted machines and take advantage of it to affect various versions of Windows operating systems and Android devices. Exploitation of a critical vulnerability has the capability of allowing cyber gangs to remotely execute arbitrary malicious code in order for a complete control.
Besides that, the Rector Ransomware also can finish its distribution through drive-by download. Drive-by download mainly refers to those third-party free downloads, including freeware, shareware, web plugins, toolbar, add-on, and a lot of other potentially unwanted programs. Attackers prefer concealing virus infection through bundling it within those freeware, just need user click to install, the virus also can be installed on the targeted machine simultaneously. While, there is another situation, the Rector Ransomware can be spread via spam email or anonymous email as an attached file with a double extension to be executable. Once followed, the Rector Ransomware would quickly compromise the targeting machine until take over it. After that, the Rector Ransomware starts to make a lot of troubles to stop you from normally using PC or android phone. All files can be encrypted with a .CBF extension, victimized users can’t be allowed to read their files as usual. And even all personal files and data are encrypted.
As seen on the infectious PC, similar to CryptoLocker encrypted virus, the Rector Ransomware blocked website says that all your files are encrypted, and you have to pay a ransom $1000 for obtaining a decryption key. It declares that the decryption software called RectorDecryptor will help you recover all your files and data just after you finish the demanding payment. While, the truth is that attackers never have consciences, they hardly will help you get all files and data back just due to their needs are satisfied. Unfortunately, the Rector Ransomware virus even will damage the victimized system all the more, because they prefer blackmailing more money once again and again. Therefore, never trust the Rector Ransomware and all its warnings reflected on the infectious PC. What best to do to reduce the damage to the minimum and even recover files is to remove the Rector Ransomware completely and quickly.
Note: If you need professional help to remove the Rector Ransomware, you can consult helps with VilmaTech 24/7 Online Services now.
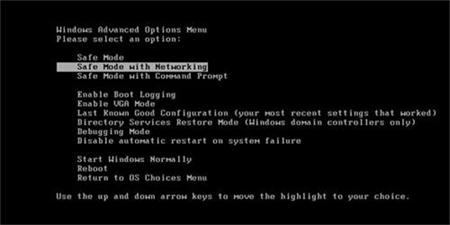
Want to counter the effect of Rector Ransomware? Boot the infectious PC to safe mode with networking. Restart the infectious system and or actually hitting F8 key for getting there. Read more on the next part.
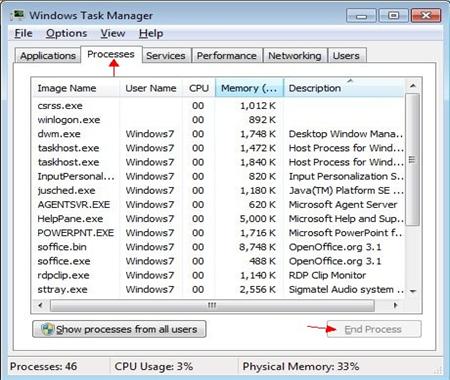
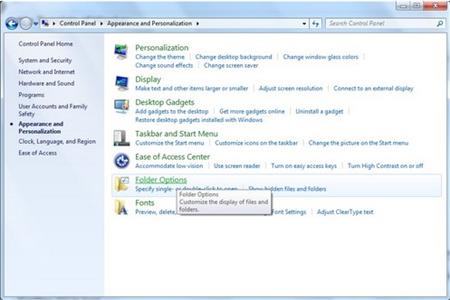
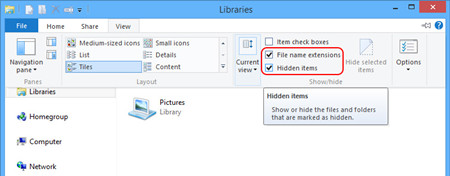
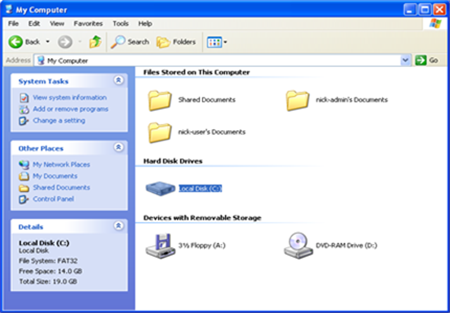
Delete RectorRansomware files from Local disk. But you need show hidden files first.

Delete the Rector Ransomware registry entries.
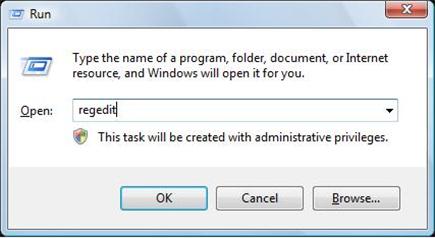
1. Press Windows+ R key to reveal out Run box. Type regedit in Run window and click Ok.
2. In the Registry Editor window, you need navigate to the below path. You then need to find out “Shell” and right click on it. Click on Modify.
3. The default value data is Explorer.exe If you see something else written in this window, remove it and type in Explorer.exe.
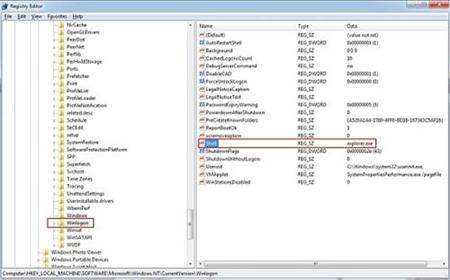
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\
4. Besides that, you still need delete Rector Ransomware registry entries, you can refer to the below registry entries.
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\[random].exe
HKEY_LOCAL_MACHINE\SOFTWARE\ Rector virus
HKEY_CURRENT_USER \Software\Microsoft\Windows\CurrentVersion\Policies\System ‘DisableRegistryTools’ = 0
HKEY_LOCAL_MACHINE \SOFTWARE\Microsoft\Windows\CurrentVersion\policies\system ‘EnableLUA’ = 0
You need reboot the infectious computer with regular mode to active the Rector Ransomware removal.
Note: Still have troubles with completely removing such aggressive virus files and registry entries? You may Live Chat with VilmaTech 24/7 Online Experts to get further help.
In case of any mistaken operation, you’d better backup files first, refer to the below video.
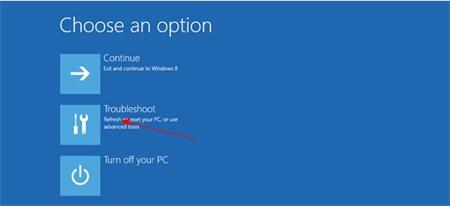
1. To restore from a restore point you will first have to navigate to the Systems Protection tab by typing “System Restore” in the Windows 8 Search bar.

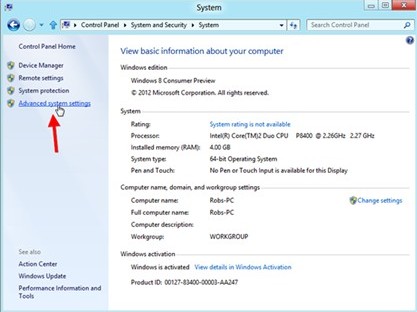
2. Open up the control panel and select “System and Security.”
3. Then select “Advanced System Settings.”
4. In the next window, click on the “System Protection Tab.”
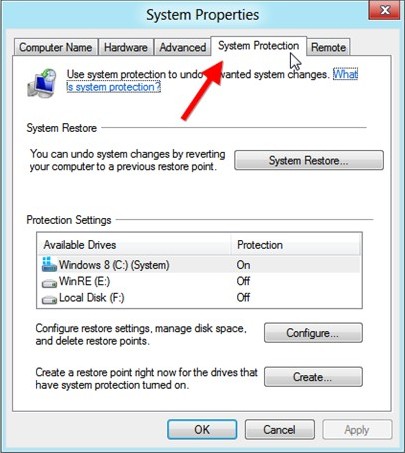
5. In the same window, click on System Restore button.

6. Next it will show you System Restore Wizard.
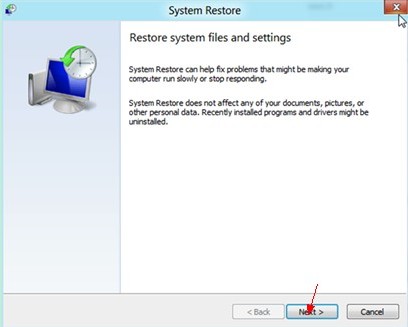
7. In the next window asks that restore point is better to take, click on it and click Next button again.
8. Later after that you’ll find the following window asking you to confirm your choice. Click on Finish button and Windows will automatically complete the restore for you.
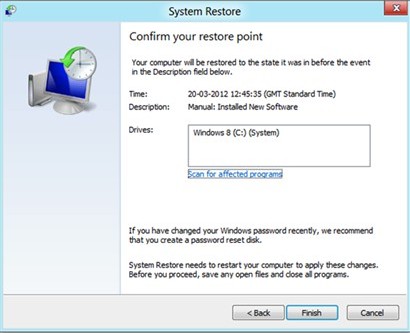
9. Reboot your computer to the regular mood to check if the virus is removed.
Rector, a newly discovered ransomware attacking online users’ computers and encrypting all files and data for blackmailing ransom. It allows attackers stealing log-in credentials and other confidential data if accomplished exploited. The Rector virus is able to encrypt files and stop victims from accessing and reading. Even PC comes guarded with normal anti-virus program, the Rector ransomware is able to bypass detection to finish the established attack. Rector Ransomware grabs people’s attention of benefit-making to maximize its distribution with ease. As a file encryption virus, Rector Ransomware doesn’t exist on the victimized machine alone and instead always tries to lure as many malicious threats as possible. In case of further damage, the Rector Ransomware should be removed completely from the infectious PC at first time. Till now, if you are still confused about the Rector encrypted virus removal, you can live chat with VilmaTech 24/7 Online Experts