Judged from the interface, it is never more obvious that websearch.searc-hall.info belongs to websearch browser hijacker family with the colorful circle and succinct interface twisted by random ads that seem to cater to your preference. It has been long since we were told that items like websearch.searc-hall.info to hijack homepage as well as search engine was virus. Yet technically speaking, they are Potentially Unwanted Programs with some potential dangers that we should throw concern over.
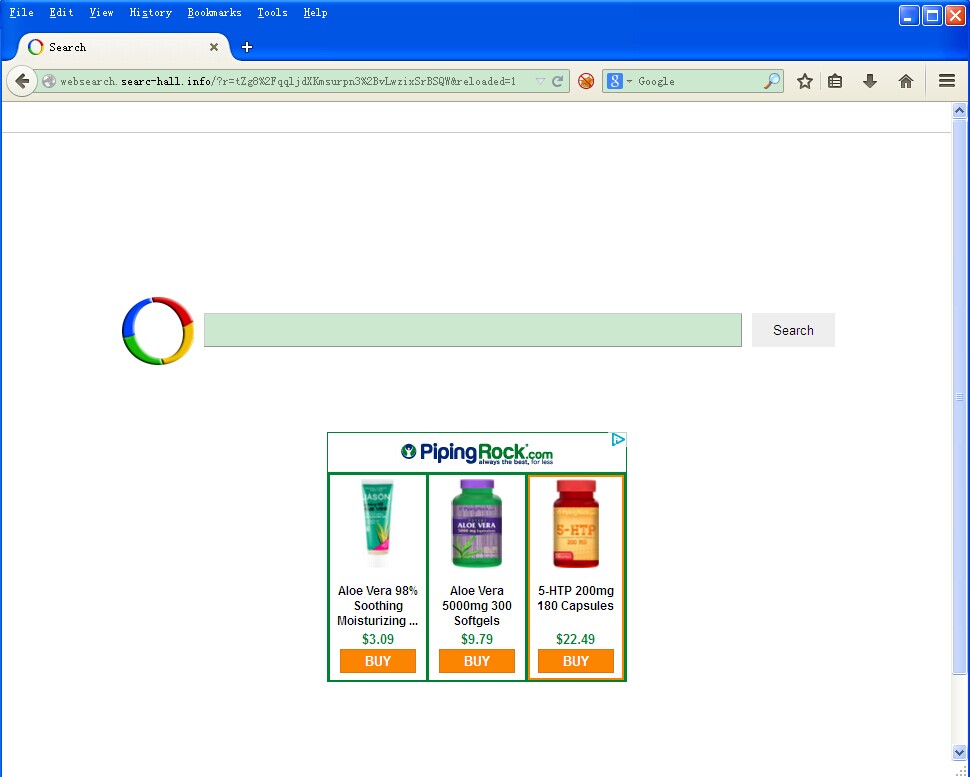
Without vicious attribute code, websearch.searc-hall.info is not virus. What makes the hijacker cling to the browsers is computing technique. DLL plug-in, BHO, JavaScript and WinsockLSP are non-virus but they can impose potential dangers when being capitalized by computer threats.
Through the URL can we tell that websearch.searc-hall.info is unsafe. All the authority sites and the self-build sites are ended with .com, .net or the suffix of the service provider instead of a string of random numbers and letters. This implies that the programming on which websearch.searc-hall.info hijacker is built is loose, bug can be evident. It should be widely informed that bug can be considered as a shortcut for virus attack, that’s why computer security center do not suggest freeware or the programs from unpopular websites. Otherwise, tragedy can happen along with the harassment by websearch.searc-hall.info hijacker:
It is clear that websearch.searc-hall.info does not belong to virus catalogue that anti-virus programs usually handle; manual method becomes the most practical solution to prevent foreseeable tragedy. Stick to the steps below and you’ll be guided to remove the hijacker. In the event that you run into unexpected issues, simply get specialized technical help from VilmaTech Online Support right away by pressing on the live chat button below.
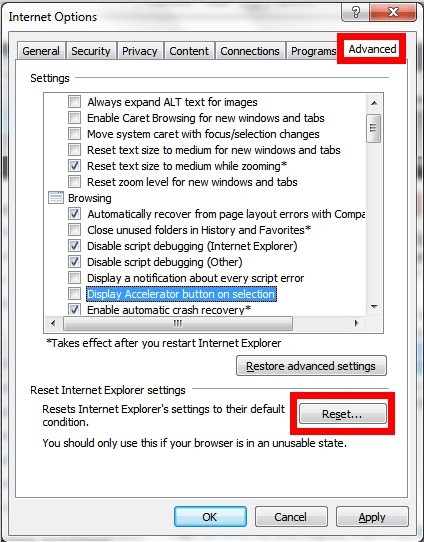
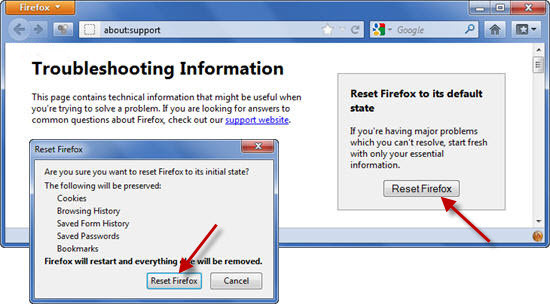
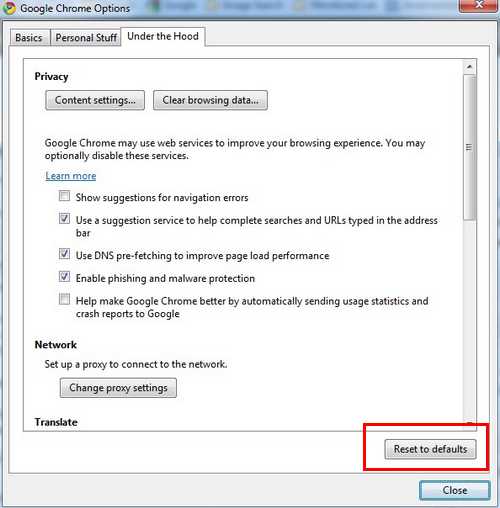
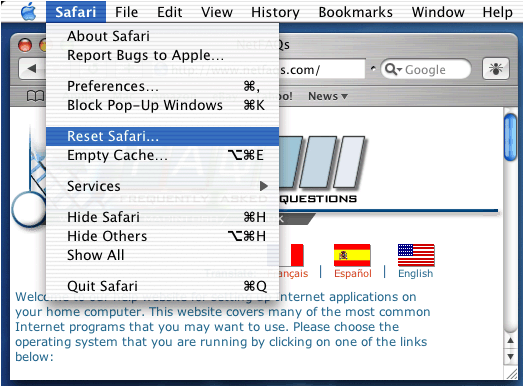
Step1. Reset browser settings to restore the modification by websearch.searc-hall.info.
Internet Explorer
Mozilla Firefox
Google Chrome
Opera
Windows 7/XP/Vista
- Access control panel to select “user accounts and family safety”.
- Click open ‘Folder Options’ and hit View tab to tick ‘Show hidden files and folders” and non-tick “Hide protected operating system files (Recommended)’.
Windows 8
- Access Windows Explorer and navigate to its View tab.
- Tick ‘File name extensions’ and ‘Hidden items’.
Safari
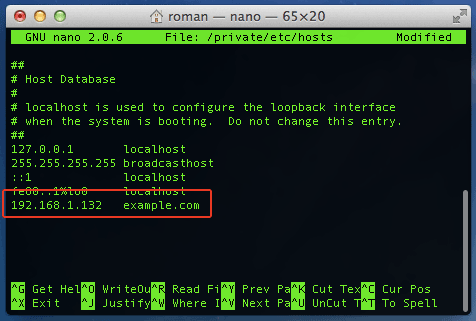
Step2. Modify Hosts file to remove websearch.searc-hall.info hijacker.
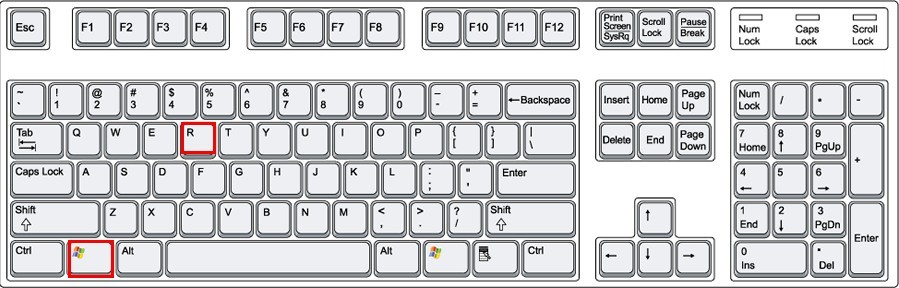
Windows users to follow up
Mac users to follow up

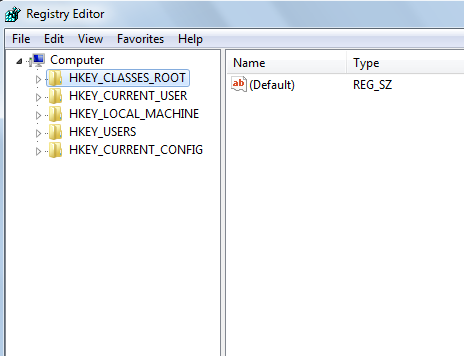
Step3. Rectify registry entries to remove Websearch.searc-hall.info (not for Mac).
Tip: before doing this, please backup your registry for precaution just in case you make some slight mistake that would end up with permanent damage. The backup instruction video is at the end of this article.
Instead of the mess incurred by the browser hijacker, what websearch.searc-hall.info wants is money. At the outset, browser hijacker was created by black hat SEOers to increase click through rate and pay per click without generating beneficial materials. Gradually, the ones resembling websearch.searc-hall.info are produced to be e-marketing tool and worse, a tool to direct virus attack.
It is uncertainty that websearch.searc-hall.info has something to do with virus. But that it drops down additional programs is for sure. VilmaTech Online Support would kindly suggest taking more steps after removing websearch.searc-hall.info completely for the sake of security. Should you have troubles for that, live chat to get exclusive help according to your concrete situation.
Database is the heart of a computer. Slight inappropriate modification there could impose damage overtime. Therefore it is highly recommended to back it up before any rectifications for precaution. Here’s the video to show how to back up registry entries on Windows 8: