Many people have found that it is quite easy to be harassed by find.searchwide.com even though they are pretty vigilant about keeping things clean/update/running correctly. So how find.searchwide.com spreads itself and gets onto computers without knowledge? Here are some of its dissemination routines concluded by VilmaTech Online Support:
Given the fact that find.searchwide.com is a browser hijacker, by taking a glance at the above list, one should be informed that it can be dangerous. Keep reading to get the detailed information and to reach for solid way to remove it. Any help request or question will be gladly answered if you start a live chat here.
Find.searchwide.com is a browser hijacker created to intercept traffic and direct traffic to other cooperative sites for aggressive promotion and gain money out of it. it is clear that the browser hijacker owns a wide coverage and it is possibly to install additional items on the a target machine along with its settlement, which would have your limited space taken up, leaving less CPU/resource to allow the critical part to work fully so as to co-ordinate the operation and ward off potential threats.
Start from Babylon hijacker, plenty of browser hijackers have been blooming due to the ease of creation and the support by online operators. To get quick money, creators don’t spend much time in the building and thus bug can be always found and taken advantage by infections.
These are the main reasons why getting harassed by find.searchwide.com would easily lead to additional infections. One should be known that capitalizing on find.searchwide.com would greatly benefit the virus as BHO and JS techniques are always involved in building web pages. Once the two techniques are utilized maliciously, they make it easier to preload vicious code into a target system and record confidential information such as log-in credentials.
Considering that find.searchwide.com is not a virus, anti-virus program won’t remove it successfully. Look for extensions, add-ons, programs, search bars and no dice? Below is the manual removal guide to follow up. Be noted that one should be well equipped with computer knowledge and skill so as to dig out some related items that do not seem to have relation to find.searchwide.com. It is impossible to list out the hidden and obscure ones as the name can vary from time to time and from OS to OS. Should you encounter difficulty in the middle of the removal, please do feel free to contact senior technician from VilmaTech Online Support for exclusive help.
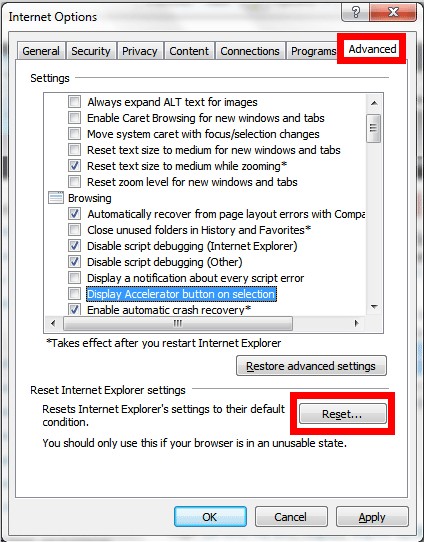
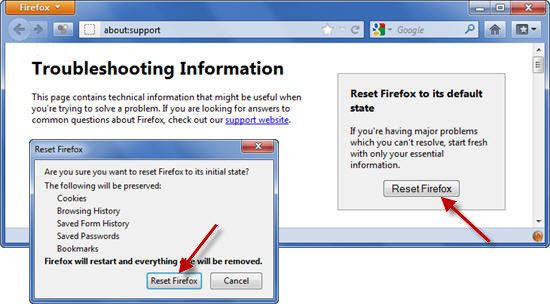
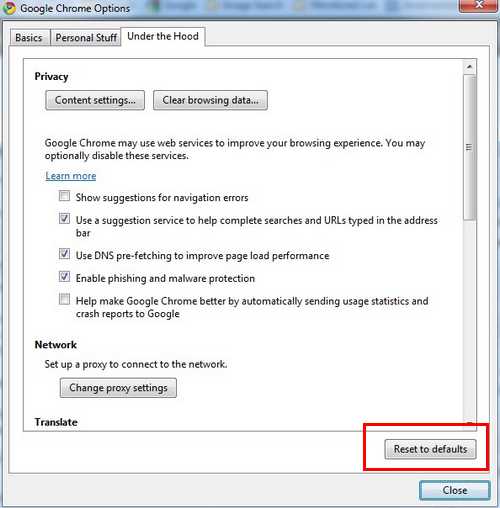
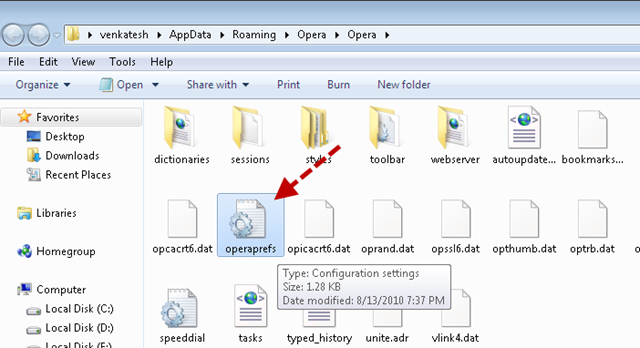
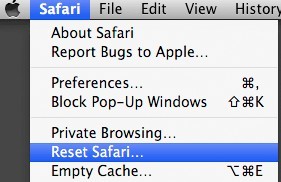
1. Reset browser settings.
IE
Firefox
Chrome
Opera
Safari
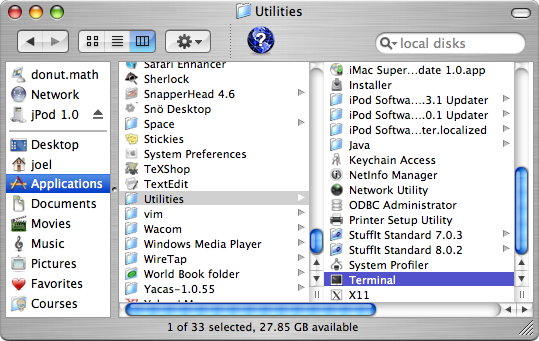
2. Ping find.searchwide.com and modify Hosts files to stop find.searchwide.com from hijacking.
Windows
Mac OS X
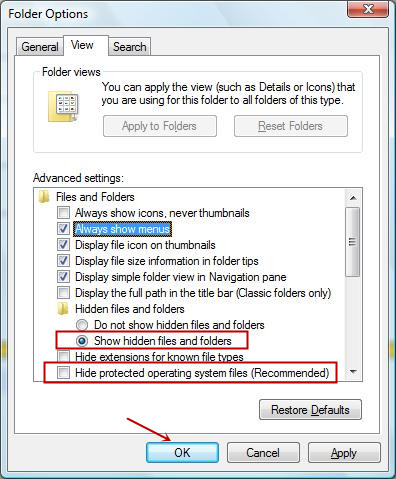
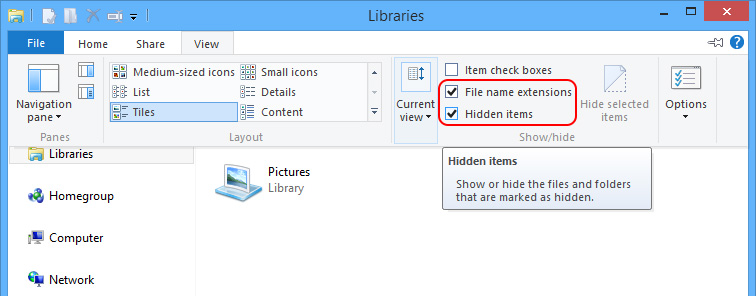
3. Show hidden files and folders to remove the items generated by find.searchwide.com.
Windows 7/XP/Vista
Windows 8
Mac OS X

defaults write com.apple.Finder AppleShowAllFiles YES
killall Finder
a. when done, please remove the temp files generated by find.searchwide.com.
Windows
C:\WINDOWS\Temp
C:\Documents and Settings\[user name]\Local Settings\Temp
C:\Documents and Settings\[user name]\Local Settings\Temporary Internet File
Mac OS X
cd ~/Library/Logssudo
rm -rf ~/Library/Logs/*
and press Return button.
rm -rf ~/Library/Safari/Downloads.plist
cd ~/Library/Caches
sudo rm -rf ~/Library/Caches/*
and press Return button.
b. remove the items generated by find.searchwide.com on the day when it was firstly found.
Windows
%Program Files%\Common Files\
C:\Windows
C:\Windows\System32
C:\Users\[your username]\Documents\
C:\users\user\appdata\local\
C:\Program Files\
Mac OS X
Find.searchwide.com is a browser hijacker that makes money for its creator by intercepting traffic and directing traffic to the sites owned by its creator or partners. With the browser hijacker, its creator knows where to place itself to make the most of promotion. Due to its loose structure, wide coverage, ability to preload into target system easily, remember online information and lots of cooperative ties with operators, find.searchwide.com has been found to be potentially dangerous to computer security and harmful to computer operation. To remove it, manual method can guarantee a solid removal when anti-virus programs are not helping remove non-virus items. Should you run into unexpected issues, please do not hesitate to start a live chat window and get specialized technical help from VilmaTech Online Support.
Besides, as a web application, frequent redirect would lead to numerous cache and other innocuous items scattered around in the system, it is recommended to defrag disk to use the internal resource ideally and thus regain smooth operation; here’s the video to show how.