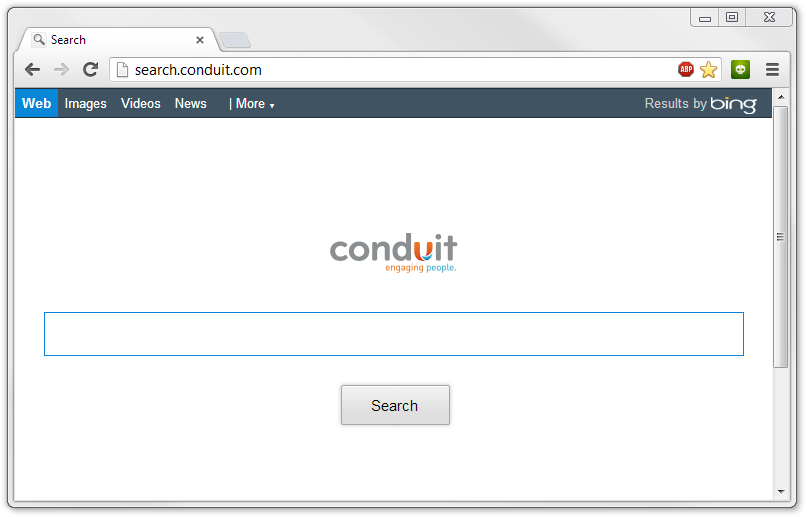
Search.conduit.com, also known as Search Conduit virus and Conduit engaging people virus, has been recognized as a notorious browser hijack virus that mainly attacks Windows operating system. As a hack tool created by cyber criminals, Search.conduit.com can be used by hackers to boost website traffic on your various browsers (eg. Internet Explorer, Mozilla Firefox and Google Chrome) and benefit from the pay-per-click technique. Being covered with a bogus search engine, Search.conduit.com virus pretends to be a legitimate and practical website, offering the similar search service like Yahoo, Google or Bing. Instead, Search.conduit.com is nothing but a harmful redirect virus that we need to eradicate. Overwhelming majority of PC users cannot pick up the precise time when the Search Conduit virus is installed on target machine.
 Tricky as Search Conduit virus is, it is distributed by some free applications’ downloads, malicious websites that may contain pornographic content, or the lawful websites that have been attacked by Search Conduit redirect. In the meantime, Search.conduit.com virus could be lurked into your computer through opening unknown sponsored link Email, alerting PC users to keep cautious while utilizing any unreliable resource online. We should keep in mind that it is indispensable to remove Search.conduit.com virus once being informed of its existence. As soon as Search.conduit.com redirect virus occupies your browser, it has the ability to modify DNS settings and alter default homepage forcibly. Thus, whenever you open your browser and start a new link or tab, Search.conduit.com would appear automatically without any permission. Meanwhile, Search Conduit virus tends to install its related toolbars, add-ons or extensions on locked browsers for the sake of tracing and record the search history and cookies. That is to say, your confidential online data is under high risk that can be pilfered by cyber crooks easily. What’s more, Search.conduit.com is always bundled with numerous additional malicious websites like infamous Babylon Toolbar virus as well as potential Trojans, worms, keyloggers and rogue. Weird symptoms may be activated on your PC; these may include slow performance of system, unusable Firewall, the high usage of CPU, randomly PC freeze and so on. We can easily tell that for the purpose of avoiding any wanted damage and data loss, it is time to take over the effective approach to remove Search.conduit.com permanently for good.
Tricky as Search Conduit virus is, it is distributed by some free applications’ downloads, malicious websites that may contain pornographic content, or the lawful websites that have been attacked by Search Conduit redirect. In the meantime, Search.conduit.com virus could be lurked into your computer through opening unknown sponsored link Email, alerting PC users to keep cautious while utilizing any unreliable resource online. We should keep in mind that it is indispensable to remove Search.conduit.com virus once being informed of its existence. As soon as Search.conduit.com redirect virus occupies your browser, it has the ability to modify DNS settings and alter default homepage forcibly. Thus, whenever you open your browser and start a new link or tab, Search.conduit.com would appear automatically without any permission. Meanwhile, Search Conduit virus tends to install its related toolbars, add-ons or extensions on locked browsers for the sake of tracing and record the search history and cookies. That is to say, your confidential online data is under high risk that can be pilfered by cyber crooks easily. What’s more, Search.conduit.com is always bundled with numerous additional malicious websites like infamous Babylon Toolbar virus as well as potential Trojans, worms, keyloggers and rogue. Weird symptoms may be activated on your PC; these may include slow performance of system, unusable Firewall, the high usage of CPU, randomly PC freeze and so on. We can easily tell that for the purpose of avoiding any wanted damage and data loss, it is time to take over the effective approach to remove Search.conduit.com permanently for good.

Well, Search.conduit.com is similar to many viruses released that can escape antivirus or can even prevent from scanning. Why? It’s obvious that people usually got this virus on their computers when surfing online, but when they wanted to remove it, only to find that the antivirus programs couldn’t pick it up at all. This is mainly because Search.conduit.com hides deep in the registry entries and mutates at quick speed that is capable of blocking antivirus software. Besides, it can also infect many system files and make them become its associated files. Although Search.conduit.com removal didn’t help, people can still clean this threat completely by following the manual removal guide below.
1. Delete Search Conduit add-ons and repair search engine
Internet Explorer:
1) Go to Tools -> ‘Manage Add-ons’;
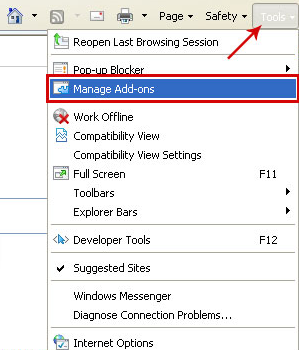
2) Choose ‘Search Providers’ -> choose ‘Bing’ search engine or ‘Google’ search engine and make it default;
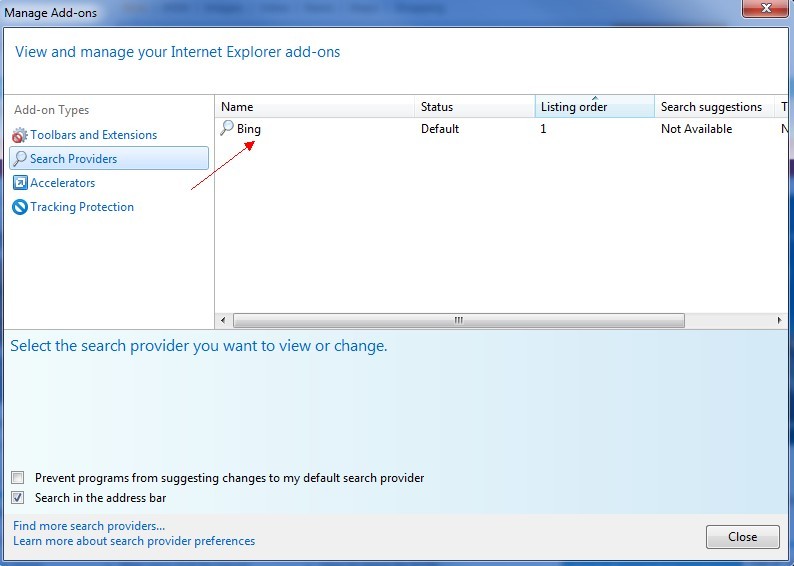
3) Select ‘Search Results’ and click ‘Remove’ to remove it;
4) Go to ‘Tools’ -> ‘Internet Options’; select ‘General tab’ and click website, e.g. Google.com. Click OK to save changes.

Google Chrome:
1) Click on ‘Customize and control’ Google Chrome icon, select ‘Settings’;
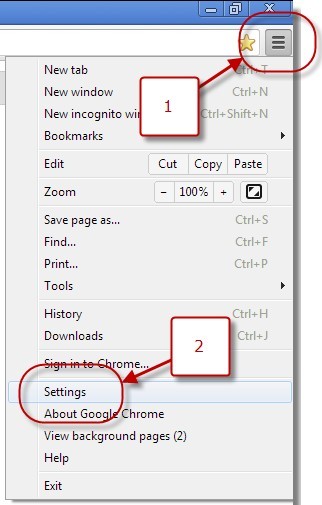
2) Choose ‘Basic Options’;
3) Change Google Chrome’s homepage to google.com or any other and click the ‘Manage Search Engines…’ button;
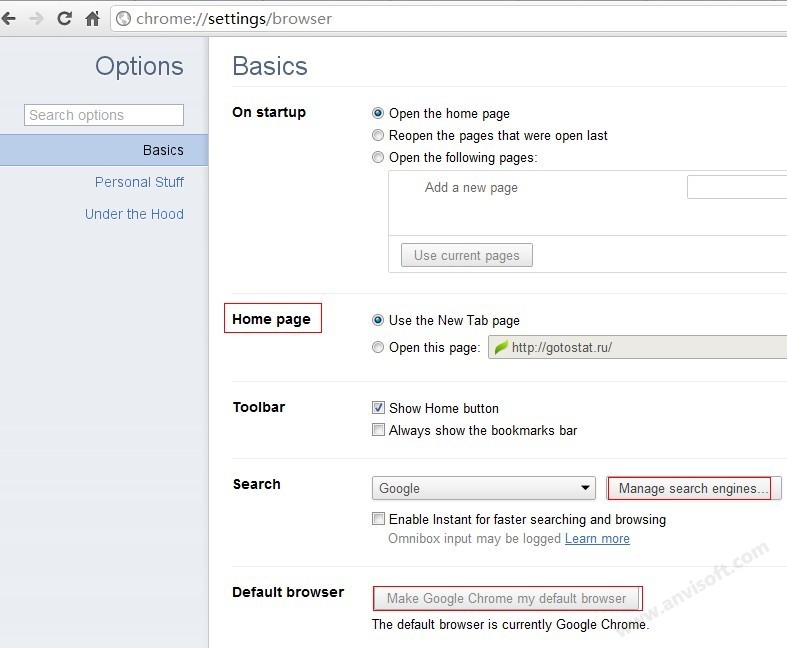
4) Select ‘Google’ from the list and make it your default search engine;
5) Select ‘Search Result’ from the list to remove it by clicking the ‘X’ mark.
Mozilla Firefox:
1) Click on the magnifier’s icon and select ‘Manage Search Engine…’;
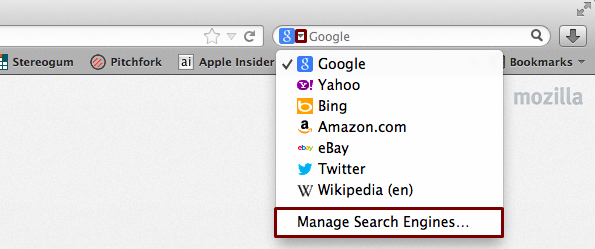
2) Choose ‘Search Results’ from the list and click ‘Remove’ and OK to save changes;
3) Go to ‘Tools’ -> “Options”. Reset the startup homepage or change it to google.com under ‘General tab;
2. Remove all its registry files.
1. To stop all Search.conduit.com, press CTRL+ALT+DELETE to open the Windows Task Manager.
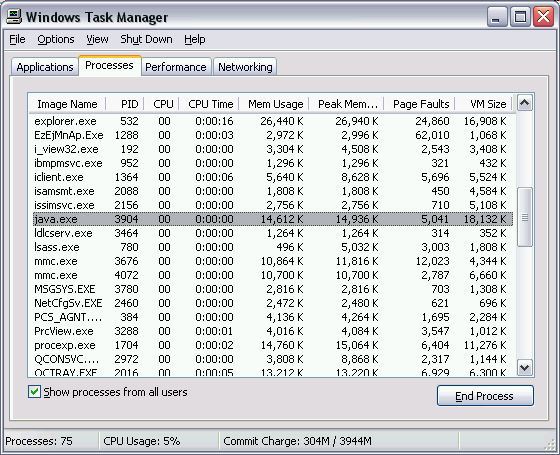
2. Click on the “Processes” tab, search for Search.conduit.com, then right-click it and select “End Process” key.
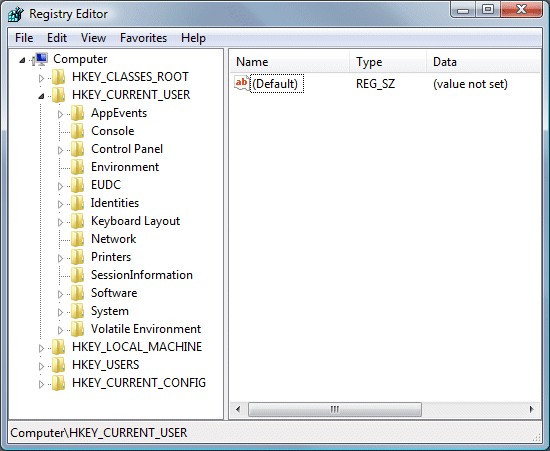
3. Click “Start” button and selecting “Run.” Type “regedit” into the box and click “OK.”
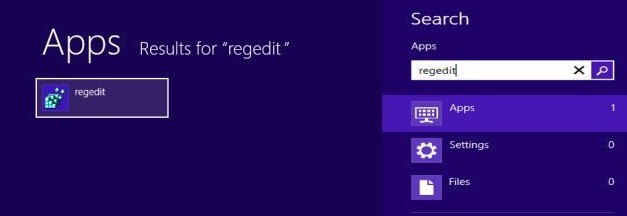
4. Once the Registry Editor is open, search for the registry key “HKEY_LOCAL_MACHINE\Software\ Search.conduit.com.” Right-click this registry key and select “Delete.”
5. Navigate to directory %PROGRAM_FILES%\ Search.conduit.com \ and delete the infected files manually.
%Windir%\temp\random.exe
%Windir%\Temp\random
HKLM|HKCU]\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\Userinit
HKLM|HKCU]\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\random
• Use a firewall to block all incoming connections from the Internet to services that should not be publicly available. By default, you should deny all incoming connections and only allow services you explicitly want to offer to the outside world.
• Enforce a password policy. Complex passwords make it difficult to crack password files on compromised computers. This helps to prevent or limit damage when a computer is compromised.
• Ensure that programs and users of the computer use the lowest level of privileges necessary to complete a task. When prompted for a root or UAC password, ensure that the program asking for administration-level access is a legitimate application.
• Disable AutoPlay to prevent the automatic launching of executable files on network and removable drives, and disconnect the drives when not required. If write access is not required, enable read-only mode if the option is available.
• Turn off file sharing if not needed. If file sharing is required, use ACLs and password protection to limit access. Disable anonymous access to shared folders. Grant access only to user accounts with strong passwords to folders that must be shared.
• Turn off and remove unnecessary services. By default, many operating systems install auxiliary services that are not critical. These services are avenues of attack. If they are removed, threats have less avenues of attack.

There is not any perfect antivirus that can catch all computer infections in the world. Though manual removal is the effective way to remove Search.conduit.com, some files might be hidden or changed, so you should realize that manual removal of Search.conduit.com is a cumbersome procedure and does not ensure complete deletion of the malware. Besides, manual interference of this kind may cause damage to the system. So we strongly recommend you get help from vilma agents who will save your time and guarantee the needed result.