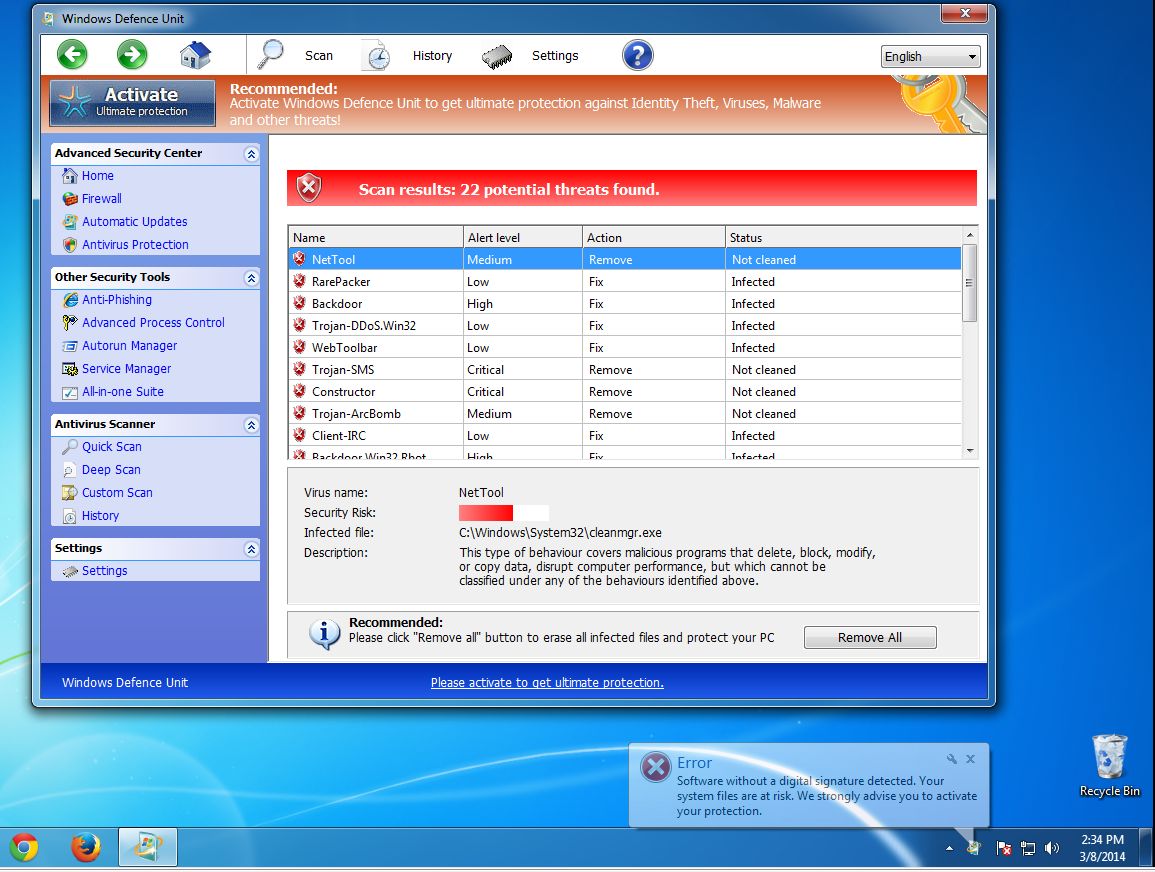
Windows Defence Unit is new type of fake antivirus program or rogue virus, which is adept at utilizing counterfeit automated scanners to meddle with user’s regular routine. Upon its installation, this specific type of rogue virus generally appears to victims in the form of a fake Windows warning on affected operating system, claiming that a mass of PC viruses are detected. To troubleshoot the problem, Windows Defence Unit will deceive users to purchase its simulated removal of malware as well as ultimate security protection. It is certain that Windows Defence Unit is only a freshly form of Internet fraud tool utilized by cyber criminals, which is quite similar as the infamous Futurro Antivirus Rogue-AV threat. For the purpose of covering up its malignity, Windows Defence Unit virus commonly imitates the basic structure and GUI (Graphical User Interface) from legitimate security tool.
By default, this type of rogue virus has the capability to be loaded automatically on every Windows boot by technically modifying the work of default Windows boot sector, which is responsible for the operating system’s bootloader. When initialized, Windows Defence Unit virus may forcibly block the legitimate antivirus application or other security tool from running in order to avoid auto security protection. While running in affected operating system, Windows Defence Unit may slow down the performance of system through occupying high computing resources. This may keep CPU running at 100% abnormally. Apart from those basic symptoms, Windows Defence Unit rogue virus may also generate website traffic by bringing up numerous pop-up ads out of expectation. In addition, the infection may even open a backdoor for remote hackers using found security vulnerabilities. Thereupon a backdoor can be used to drop and install additional PC malware onto compromised machine for further harm. As a result, users are obliged to remove Windows Defence Unit virus timely as long as being informed of its existence in order to be end up all its symptoms.
Note: To get rid of Windows Defence Unit virus, you can adopt the following manual removal. If you are not familiar with the operation and afraid of making mistake, you may start a live chat with the VilmaTech Certified 24/7 Online Experts to help you resolve your issue for good.
1. Windows Defence Unit virus may sneaks into a targeted computer without user’s authorization or knowledge. To be specific, it may be distributed by malicious website or other compromised web pages. Users may get infected with this malady when they navigate to a malign link or attachment in an infected email. Windows Defence Unit virus may be packaged with specific application which seems to be legitimate for users.
2. Windows Defence Unit virus may have an auto scan on affected computer upon its installation, allegedly checking the affected computer system for potential security threats.
3. Windows Defence Unit virus may slow down the performance of computer via taking up large amounts of system resources, and keep CPU run at 100%.
4. Windows Defence Unit virus may make use of found security vulnerabilities to open a backdoor for attackers. This may lead to additional infection on compromised machine, such as Trojan, worm, keyloggers or other unclear subjects.
Users may wonder the most effective way to terminate Windows Defence Unit virus from computer. Well, having the similar properties as other Rogue AV threat, Windows Defence Unit virus has the capability to block installed antivirus software program or other security tools from running so that to avoid auto removal. Even though users have updated their antivirus software to the latest version, it may still have a very low chance to clean up Windows Defence Unit from computer. If this is the case, you may consider the helpful manual removal to erase all its related processes, dll. files and registry files entirely. Anyhow, manual removal is a high-level tech operation that requires computer expertise. If you cannot handle it alone, you may ask help from the recommended VilmaTech 24/7 Online Experts for further solution.
Part one: Log in Safe Mode with Networking.
Method for Windows 7, XP and Vista:
1. Reboot infected PC.
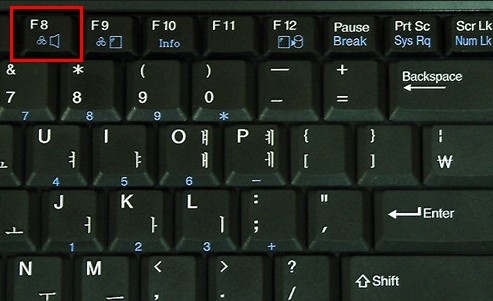
2. Before Windows logo appears, keep pressing F8 key.
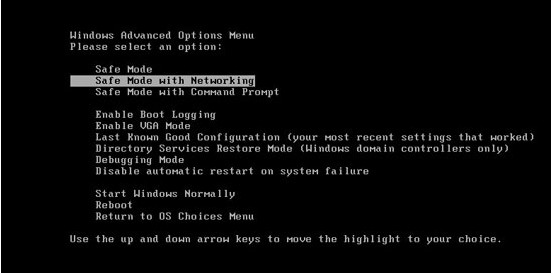
3. In Advanced Boot Options, select Safe Mode with networking and Enter.
Method for Widnows 8 users:
1. Reboot infected computer.
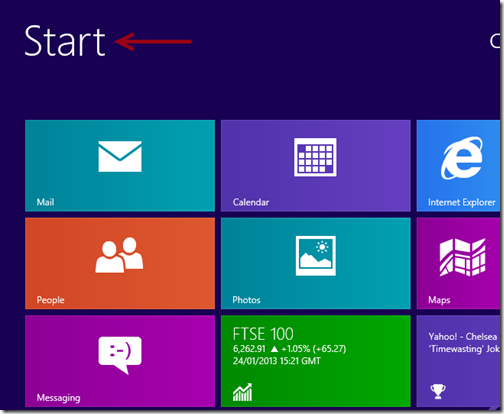
2. Click Start menu in Metro User Interface.
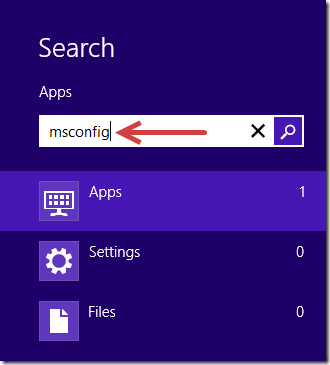
3. In the Search box, type msconfig in the box and Enter.
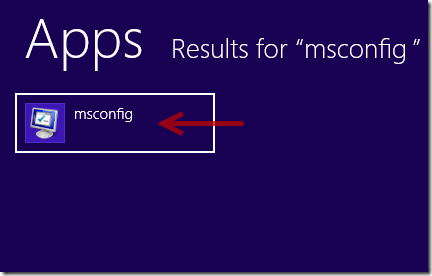
4. Click the msconfig icon from the search results.
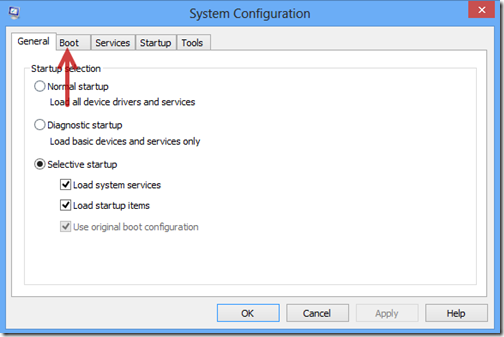
5. In the pop up System Configuration menu window, choose/select Boot tab.
6. Check the box for Safe Boot and choose Network option so that to have Internet service in Safe Mode.
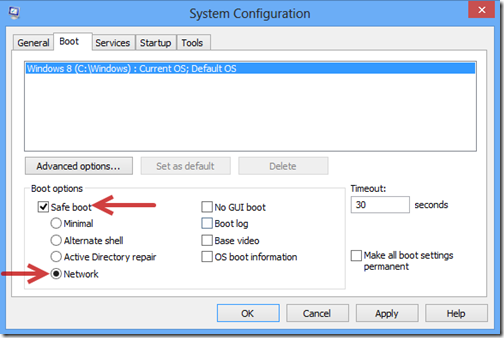
7. Then select Restart to continue.
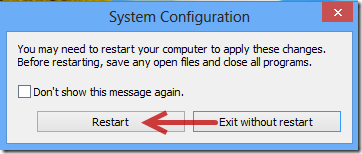
8. Wait for minutes. Windows will automatically boot into Sade Mode with Networking later.
Part two: Remove leftover and registry files of Windows Defence Unit.
1. Kill the process of Windows Defence Unit.

2. Remove the following files of Windows Defence Unit.
%system%\[random characters].dll
%Documents and Settings%\[User name]\Desktop\[random name].exe
C:\Users\Stuart\AppData\Local\Temp\[random names].exe
3. Get rid of the following registry entries of Windows Defence Unit.
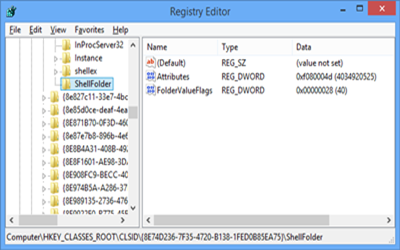
HKEY_CLASSES_ROOT\CLSID\[random numbers]
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\”Shell” = “[SET OF RANDOM CHARACTERS].exe”
HKEY_LOCAL_MACHINE \ Software \ Microsoft \ Shared Tools \ MSConfig \startupfolder\[random names]
HKEY_LOCAL_MACHINE \ Software \ Microsoft \ Shared Tools \ MSConfig \ startupreg\[random names]
1. Do not use any unreliable online resource. As we have mentioned before, Windows Defence Unit virus may be delivered by some infected Internet resources, such as compromised websites, SPAM email and infected applications. Thereupon, users need to keep cautious while using those distrusted resources to refrain from unexpected damage or loss.
2. Build up a firewall protection. By default, Windows operating system provides a built-in firewall protection which can be used to block all incoming connections from Internet to services. Users can only allow services they explicitly want to offer to the outside world to reduce the chance of getting infected with potential threats.
3. Have a quick/full scan in antivirus software. It is evident that a standard antivirus application is capable of safeguarding user’s machine from a variety of PC threats. To prevent from unwanted viruses, users may regularly have a quick/full scan in their antivirus software applications. However, antivirus may not be able to deal with all kind of threats which are endowed with advanced hack techniques by attackers. In this case, users may think over other helpful method such as manual approach to get rid of them completely.
Windows Defence Unit is categorized as a fake antivirus application produced by cyber criminals to make damage on affected computer and gain from victims. Most commonly it clones the basic user interface from standard antivirus or security tool to increase its illusion. Once being installed, Windows Defence Unit virus often perform an auto scan for affected computer, claiming that the machine is at high risk due to the detected PC threats. To clean up alleged threats, Windows Defence Unit virus generally misleads users into activating and purchasing its “full” version. In reality, Windows Defence Unit has nothing to do with those so-called functions or services. It is only a fraud tool utilized by attackers for money extortion. Apart from the basic symptoms, Windows Defence Unit may led to the sluggish performance of Windows by occupying high computing resource, and even open a backdoor for hackers using found system loopholes. Without any doubts, users need to remove Windows Defence Unit virus from computer once being informed of its presence. However, it may block antivirus application from running to avoid auto removal. If this is the case, users may think over the helpful manual removal to terminate Windows Defence Unit from computer.
If you cannot remove Windows Defence Unit virus by yourself, you may start a live chat with the recommended VilmaTech 24/7 Online Tech Experts to help you out of trouble.