![Remove Win64:Dropper-Gen[Drp]](https://blog.vilmatech.com/wp-content/uploads/2014/03/win64-dropper-gen.png)
Win64:Dropper-Gen[Drp] is a generic Trojan Horse with a major task of dropping down complementary items as well as virus from its remote server. To know more details in how Win64:Dropper-Gen[Drp] triggers the above troubles, how dangerous it is and the recommended way to remove it completely, it is advisable to keep reading. Any help request can be promptly answered if you contact VilmaTech Online Support by clicking on the below button.
With generic characteristic of a Trojan Horse, Win64:Dropper-Gen[Drp] manages to spread itself by two commonly used ways, one is drive-by download on website/program, and the other is vulnerability exploitation. The moment it settles in a target system, drivers concerning security utility and browsers will be numerated to be overwritten for its satisfaction, so that Win64:Dropper-Gen[Drp] becomes capable of injecting its vicious codes into system running process explorer.exe and controlling it to constantly connect to its remote server without being discouraged by build-in security services.
Consequently, ActiveX, Applet and JavaScript are falling into Win64:Dropper-Gen[Drp]’s use to help preload vicious code into the target system without being detected as they are supposed to be legit and helpful in improving surfing experience and to further alleviate the installation of additional threats. As a result, redirect problem, feed.helperbar.com for instance, is triggered. Be noted that Win64:Dropper-Gen[Drp] implants its startup executable file into system configuration to guarantee that the suspended dropping task would continue the next system boot. On this occasion, the target machine has become so extremely vulnerable that susceptible to any infections.
It should be widely advised that Win64:Dropper-Gen[Drp]’s affection could threaten information security as corresponding .dll and .dat files have been inserted into local disk and browser settings situated in Registry entries. With ActiveX, Applet and JavaScript technology, Win64:Dropper-Gen[Drp] is able to record log-in credentials and track down online whereabouts, assisting in spreading vicious codes easily in the name of the victim’s or obtaining easy money directly from victims’ bank cards.
Any delay would result in additional infections and problems. Therefore, an efficient and quick solution is in desperate need. Below is the instruction to help remove Win64:Dropper-Gen[Drp] thoroughly only if professional computer knowledge and skill are available. Otherwise, contact recommended PC Security Center and get exclusive help according to your concrete situation.
Win64:Dropper-Gen is not necessarily malicious. Actions considered to be unsafe such as downloading some freeware or online games might trigger the alert upon performance. Also some faulty on programs considered to be exploited by virus or hackers would give rise to Win64:Dropper-Gen[Drp] threat alert. There are some suggest submit the affected file to virustotal for confirmation; yet it is not that it is not 100% determinate. VilmaTech Online Support would suggest follow the below steps to rule out the false positive possibility.
![disable error reporting to rule out Win64:Dropper-Gen[Drp] false positive](https://blog.vilmatech.com/wp-content/uploads/2014/03/error-reporting1.gif)
When the possibility of false positive has been ruled out and Win64:Dropper-Gen[Drp] is still flagged, the following steps will be helpful.
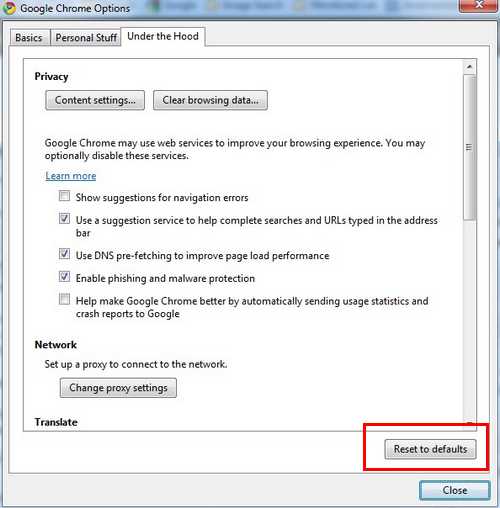
A – end vicious running processes generated by Win64:Dropper-Gen[Drp].
![select colums to end Win64:Dropper-Gen[Drp]'s running processes](https://blog.vilmatech.com/wp-content/uploads/2014/03/select-colums4.png)
![access all apps to remove Win64:Dropper-Gen[Drp]'s running processes from Win8](https://blog.vilmatech.com/wp-content/uploads/2014/03/all-apps3.png)
![use system information to remove Win64:Dropper-Gen[Drp]](https://blog.vilmatech.com/wp-content/uploads/2014/03/system-info.jpg)
B – navigate to Database to remove Win64:Dropper-Gen[Drp]’s startup item as well as other generated ones.
(tip: it is recommended to backup entries before the execution in case mistake takes place. Here’s the video to show how.)
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\Current Version
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders Startup=”C:\windows\start menu\programs\startup
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Settings “net
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\Current\Winlogon\
C – show all hidden files and folders to remove the items dropped by Win64:Dropper-Gen.
Windows 7/XP/Vista
![use folder options to show hidden items for Win64:Dropper-Gen[Drp] removal](https://blog.vilmatech.com/wp-content/uploads/2014/03/folder-options12.jpg)
Windows 8
![show hidden files to remove items generated by Win64:Dropper-Gen[Drp] on win8](https://blog.vilmatech.com/wp-content/uploads/2014/03/win8-hidden-file1.jpg)
Files and folders to delete:
%WINDIR%\SYSTEM32\[random numbers and letters].dll
C:\Windows\system32\msconfig.com
%AllUsersProfile%\[random]
%AppData%\Roaming\Microsoft\Windows\Templates\[random]
%AllUsersProfile%\Application Data\.exe
D – Reset browser to restore healthy settings from the ones modified by Win64:Dropper-Gen[Drp]
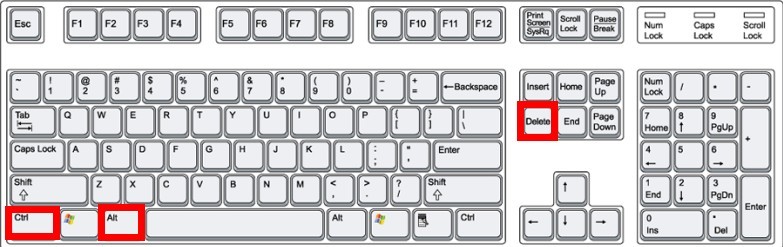
Internet Explorer
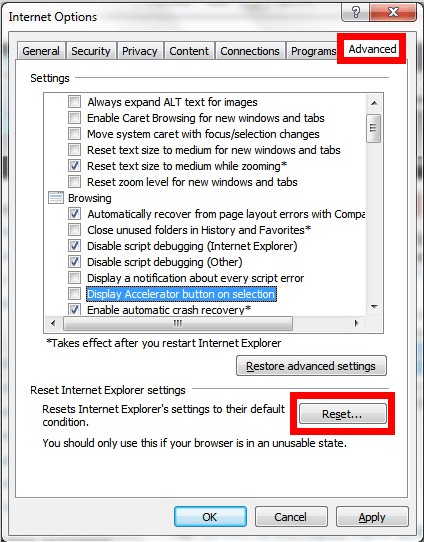
Mozilla Firefox
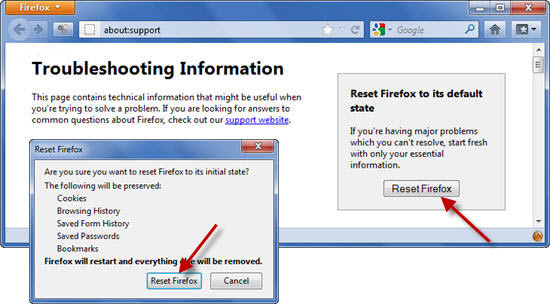
Google Chrome
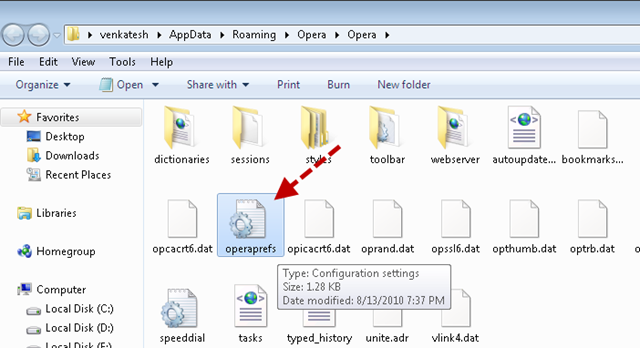
Opera
All virus is created to help acquire easy money and Win64:Dropper-Gen[Drp] is no exception. By bringing in additional threats, Win64:Dropper-Gen[Drp] manages to get profitable commission. The cyber criminal behind the Trojan Dropper manages to get extra money by reselling the information collected from a target system to other spammers longing for the knowledge of commonly-visited sites so that they are capable of spreading their products rapidly within a short period of time.
Protected by SHA256: 868efdba6e8e51bbdc99a45bbdfd2fccfa16b5e4851d86e905cf3cd0e89b602d, Win64:Dropper-Gen[Drp] is enabled not to be randomly modified by installed security utility or to delay the disruption before its complete installation. Win64:Dropper-Gen[Drp] is a cunning threat that would remove the original executable file once the settlement is done. Besides, some system running processes, explorer.exe is one of them, are affected to help maintain Win64:Dropper-Gen[Drp]’s evil deeds, which would definitely confuse the robotmorphic security programs.
VilmaTech Online Support would like to correct the false belief that anti-virus program is omnipotent to remove all computer threats. It is just a tool to automatically remove anything contains vicious attribute code for a basic protection and relief in manual removal. In the case that anti-virus programs are not able to tackle down a virus, manual removal way is highly recommended. One should be notified that the above instruction is exclusively applicable to Win64:Dropper-Gen[Drp] to the exclusion of incidental issues and infections. Should you have problems in removing extra virus, please go to virus reservoir for solutions correspondingly or as alternative live chat with senior technicians for quick and complete fix.