When holidays coming up one after another and discount goes crazy, so does browser hijackers. Among which, Safesear.ch is one that becomes active until recently. Offering a list of the most commonly visit channels, Safesear.ch does attract many PC users to use it as browser homepage without bothering asking where it comes from and how it installs. Safesear.ch endangers identity, property and information security without causing scenes due to the application of some computing techniques. Therefore, VilmaTech Online Support would love to bring it to light and offer corresponding solution.
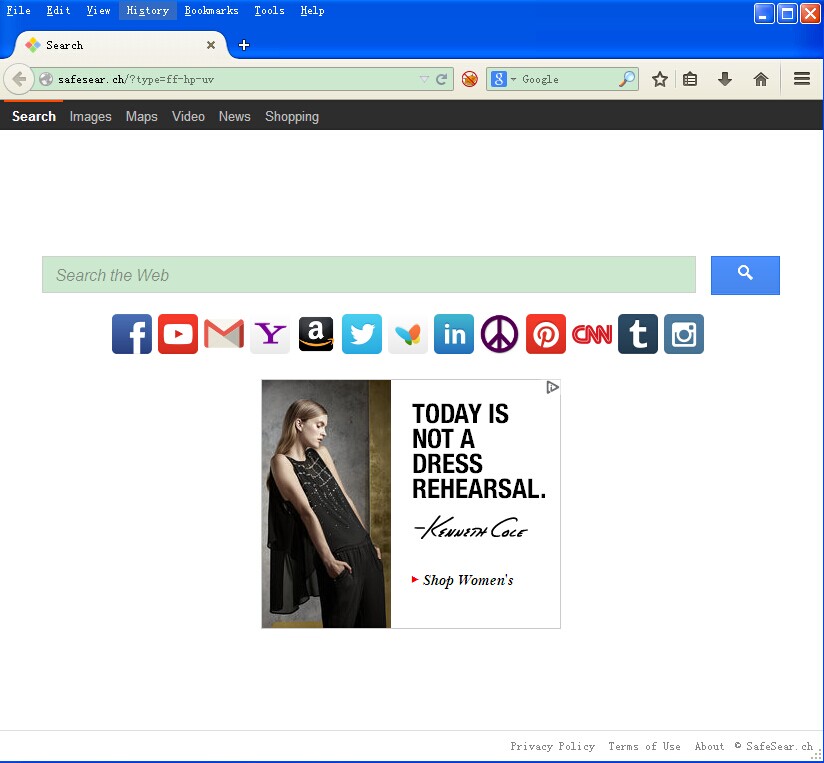
Presenting in a website form, Safesear.ch absolutely adopts JS technique, BHO (Browser Helper Object) technique. Those techniques are approved to allow quick connection and navigation on the Internet. Still, Safesear.ch applies WinsockLSP to intercept and modify inbound and outbound Internet traffic. All these techniques were supposed to be created for benefit. Sadly, they can be utilized in the other way around.
Since WinsockLSP, the DLL file, can be loaded into the SQL Server processes, it can help the browser hijacker change browser settings “permanently” and make BHO technique to serve its vicious and secrete deeds:
The ultimate purpose for its hijacking is money. How Safesear.ch makes money by simply hijacking homepage and search engine?
Safesear.ch does appalling things stealthily, using computing technique to dodge the detection and deletion by installed anti-virus programs. Such browser hijacker should be removed in no time for the sake of identity, property and information security. Stick to the steps below offered by VilmaTech Online Support. Should you run into unexpected situations during the removing process, do not hesitate to ask for instant help by starting a live chat window with the button below.
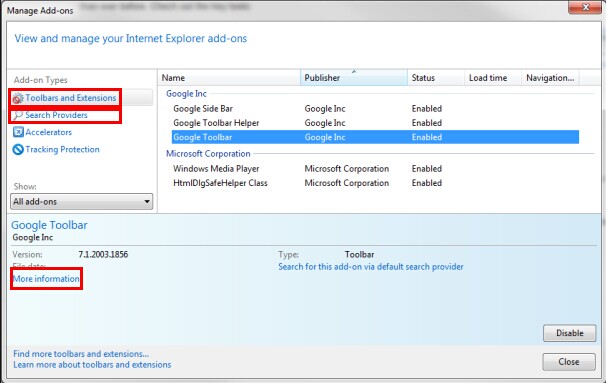
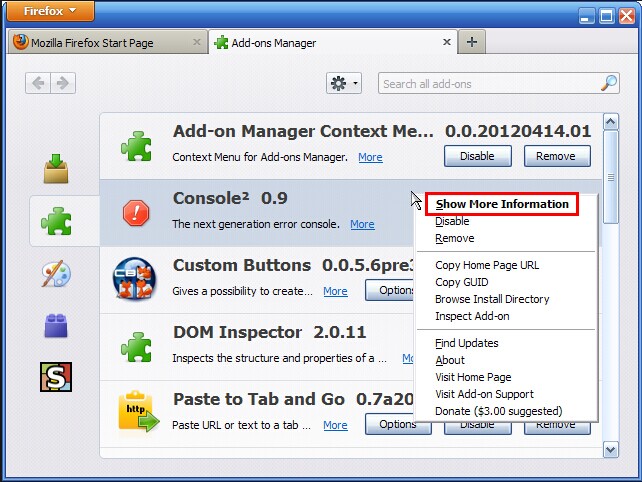
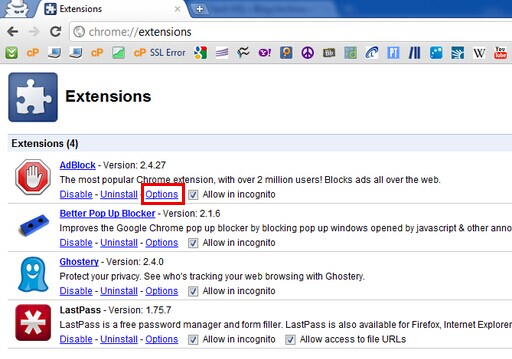
Step1. Remove Safesear.ch’s extensions/plug-ins/add-ons.
Internet Explorer
Mozilla Firefox
Google Chrome
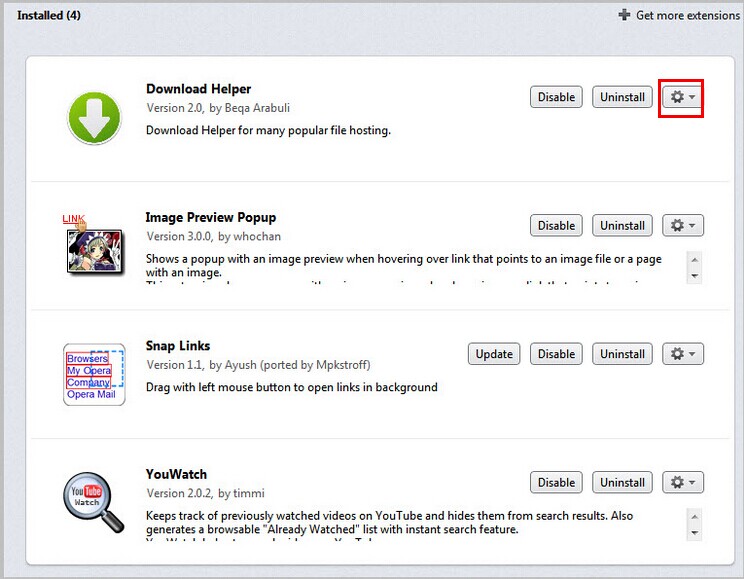
Opera
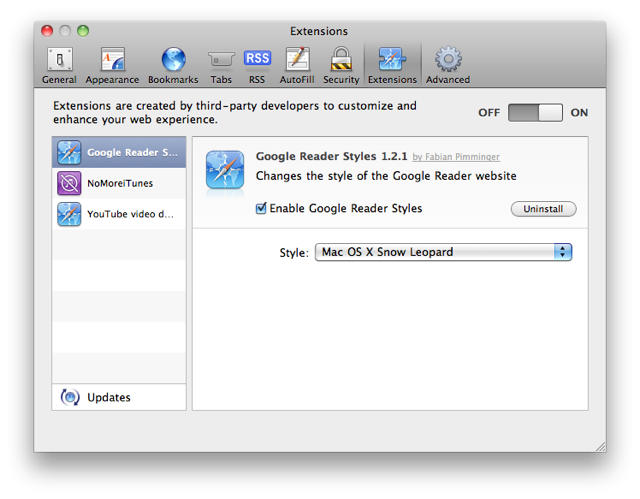
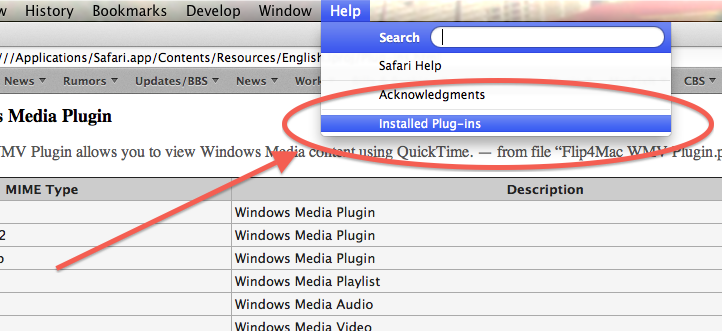
Safari
Step2. Replace Safesear.ch with desirable URL.
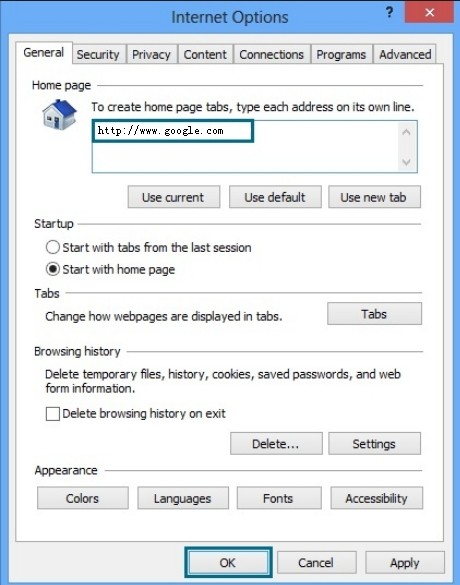
Internet Explorer
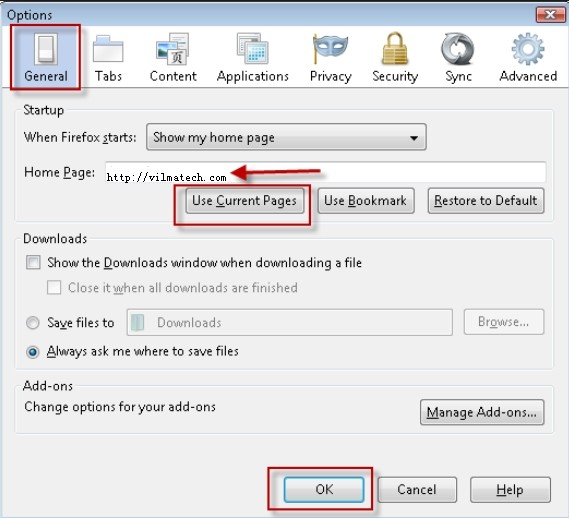
Mozilla Firefox
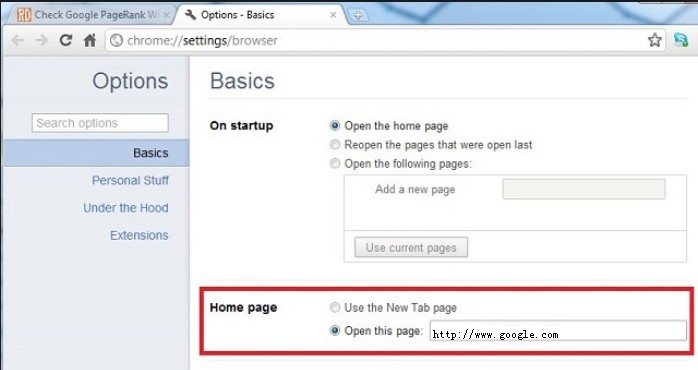
Google Chrome
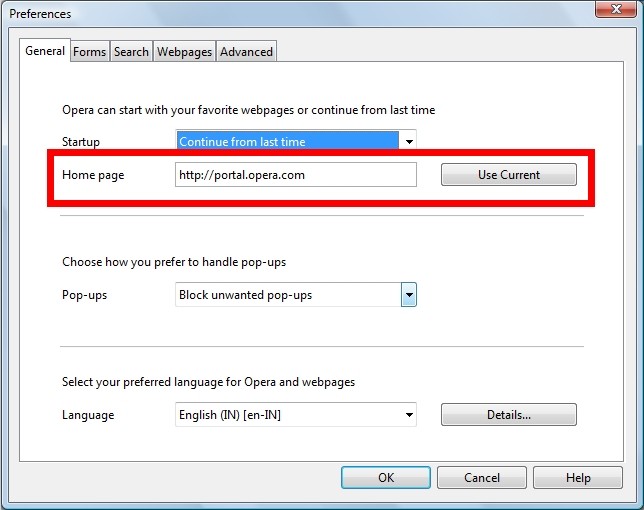
Opera
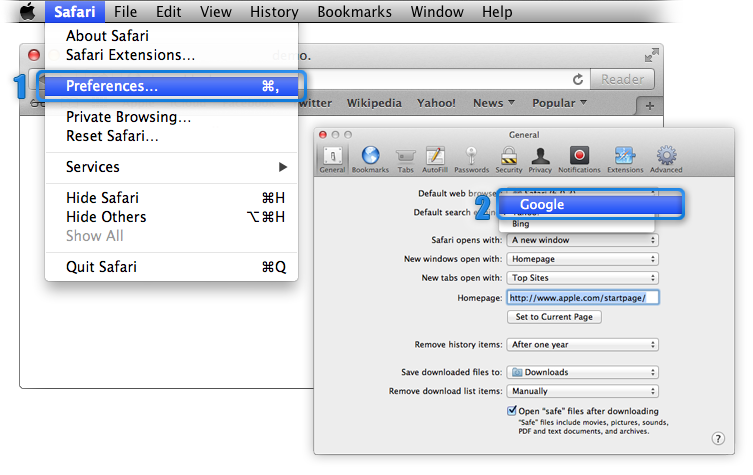
Safari
Step3. Modify Hosts file.
Windows Users to Follow up
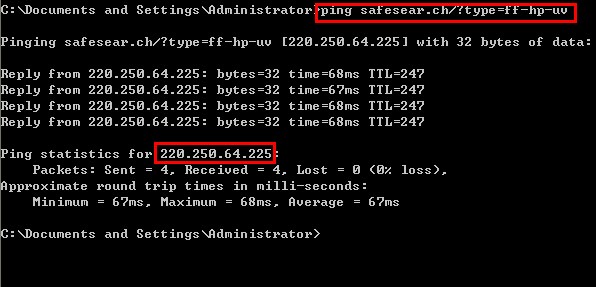
Mac Users to Follow up

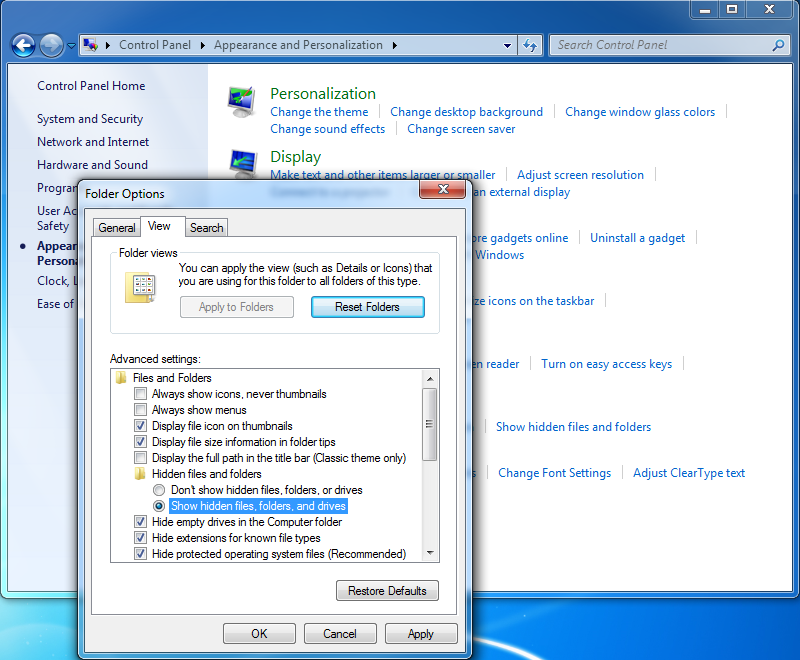
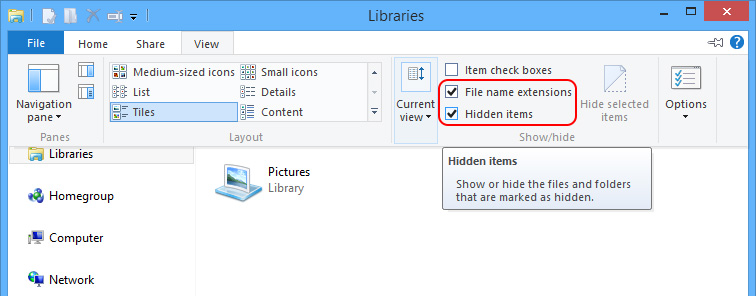
Step4. How hidden items to remove the ones created on and after the day Safesear.ch installed itself.
Windows 7/XP/Vista
Windows 8
Mac OS X
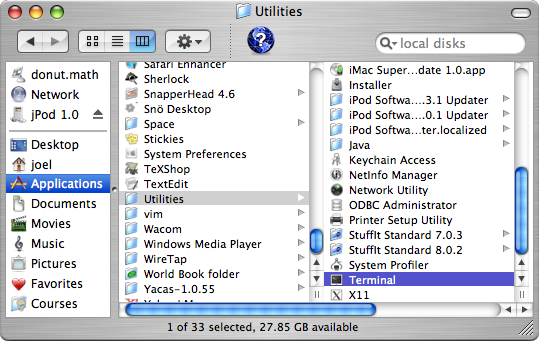
defaults write com.apple.Finder AppleShowAllFiles YES
killall Finder
When all the files and folders are revealed, please remove the files as instructed:
a. access the following directories to remove all the temp files:
C:\WINDOWS\Temp
C:\Users\[user name]\AppData\Local\Temp\
C:\Documents and Settings\[user name]\Local Settings\Temp
C:\Documents and Settings\[user name]\Local Settings\Temporary Internet Fileb. access the following directories and remove the ones created on or after Safesear.ch hijacks:
C:\Windows
C:\Program Files\
C:\windows\system32\
C:\users\user\appdata\local\
C:\users\[username]\appdata\locallow\
C:\Users\[your username]\Documents\
%SystemDriver%\
Since black hat SEO strategy brings quick financial return on websites in a short period of time, many greedy people needs hijacker like Safesear.ch. Though being punished by renowned search engine like Google, those websites can still rank high in safesear.ch and gain traffic even drastically. This is it. The moment you accidentally bump into a website applying black hat SEO, you fall into victim of safesear.ch. The best way to prevent for future affection by browser hijacker like safesear.ch is not to click anything that suddenly pops up from nowhere regardless of how attractive or official the content is like Masterupdate.net; and not to click on anything on the websites with its URL ended with a string of random letters or numbers like safesear.ch.
As we’ve been informed before that the attack by safesear.ch can lead to additional virus/program installations. Therefore, one should take more steps to deal with the residual damages after following the above given steps that are exclusively applied to safesear.ch hijacker.
Last but not least, change passwords after the complete and thorough removal of safesear.ch. It is advisable not to make the browsers “remember” your log-in credentials in the future just in case. Should you run into troubles when dealing with the residual damages, contact VilmaTech Online Support for specialized technical help by starting a live chat window here.
Many of VilmaTech’s customers report that computers run sluggishly even after the removal of browser hijacker. The unsolicited installation of safesear.ch leads to the unreasonable use of disk space. Not to mention how bad can the consequence thereof be by the items safesear.ch introduces. Therefore, it is recommended to do a defrag after the removal for better performance. Here’s the video to show how.