Recently, there have been increasing cases showing police lock down page on browsers (including Internet Explorer, Firefox, Chrome, Safari) on both computers and android phones. As usual, such accusation message is totally counterfeit and is identical except official names. PoliceGuardState.org is one member of the main force to lock down browsers for non-existent ransom. Therefore, it is also categorized as ransomware.
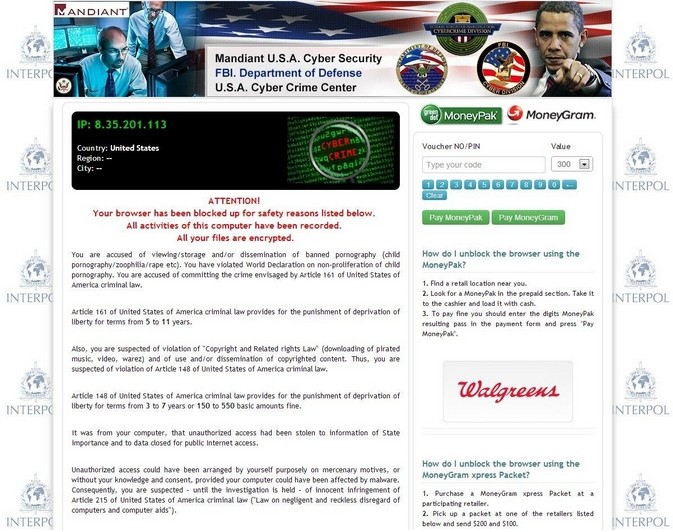
So far, PoliceGuardState.org virus has convinced many PC and Android users to submit the required money due to the legit and formal domain and the more civilized behavior than completely blocking down the entire machine/system. As a matter of fact, it is easy to get such domain simply by payment and there are ways to help PC and Android users to escape from the trap:
PoliceGuardState.org will be soon unveiled as a virus. But it is believed that few people, especially the Android phone users, know how dangerous it is. It is recommended to finish the entire article to rich your knowledge so that no delay will occur in removal to cause unexpected problems. Should there be any questions that need answers from specialized experts, hit the live chat button below.
It is only the browsers that PoliceGuardState.org virus locks down, however, it manages to impose potential dangers to a target machine and Android system. JavaScript and BHO technique have been found by Global PC Support Center to be in use. Be noted that both are legit techniques that anti-virus utilities are not programmed to deal with. Being utilized by ill-purpose cyber criminals, PoliceGuardState.org virus is enabled to obtain authentication so that criminals become capable of logging onto website with authentications to get more information including finance.
It is completely wrong for one to consider that restart would make PoliceGuardState.org virus disappeared. Due to BHO technique, its object has been pre-loaded into the startup section so that PoliceGuardState.org virus manages to popup when browsers are opened. Such obvious changes on a browser are ready to draw attention from other infections as the web vulnerability is considered to be the most efficient tool to help with broader and faster infiltration when almost everyone is connected with network.
The consequence can be imagined:
Therefore, PoliceGuardState.org virus should be removed without hesitation. Below is the new instruction trawled through by VilmaTech Online Support. Stick to it for a complete removal; otherwise PoliceGuardState.org virus can re-emerge. Also be noted that additional possibly vicious items should be removed in the process so that success can be guaranteed. In the case where computer skills are not sufficient to finish the entire instruction, use online PC and Android security service and get one-to-one assistance for a thorough removal.
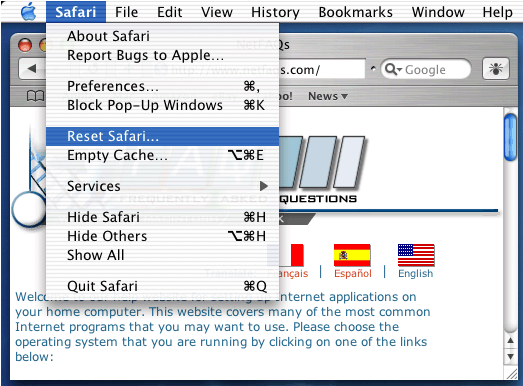
As PoliceGuardState.org virus locks down browsers, there’s chance that PoliceGuardState.org virus would appear on Macs. The removal method for Macs is offered in the last section. If you are a Android user, just start a live chat to get instant and direct help.
A
Log into Safe Mode with Networking to gain desktop so as to proceed.
Windows 7/Vista/XP
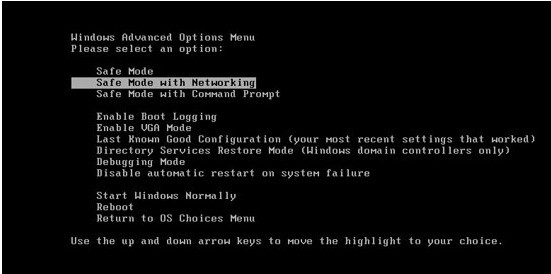
Windows 8
B
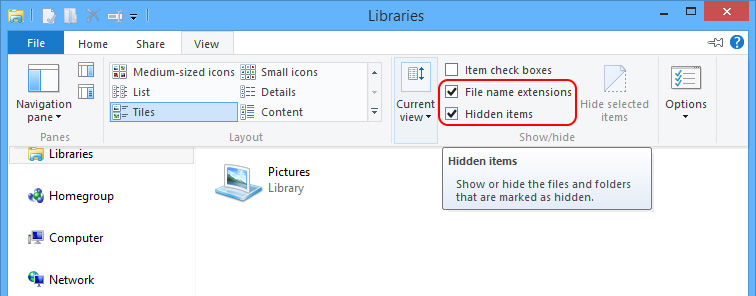
Show hidden items to remove vicious items from local disk.
Windows 8
Windows 7/XP/Vista
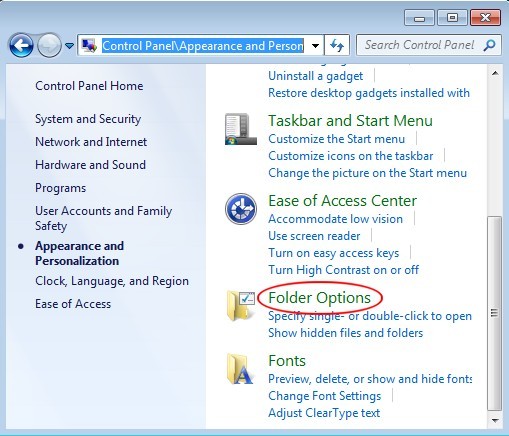
When done, navigate to C:\Windows, C:\Windows\System32\Roaming and C:\Windows\System32\Temp to remove items that are created on the date PoliceGuardState.org virus appears; steps to arrange files by date:
Other files that need to be removed:
%Program Files%\ PoliceGuardState.org
%AppData%\Protector-[rnd].exe
%AppData%\Inspector-[rnd].exe
%AppData%\vsdsrv32.exe
For Mac Users

Notice:
People pay PoliceGuardState.org virus money due to its formal-look domain and the reason being locked down (watching porn for example). So far, there’s no such report on a genuine department collect ransom in similar way. Always remember not to submit the money as once the payment is finished, the information about the payment method, such as Ukash, will be collected. Resort instructions to remove PoliceGuardState.org virus is always recommended over submitting money since submission will make things run in vicious circle. The last but not least, other vicious items should be also removed completely during the removal process so as to exterminate the possibility of additional problems like BSOD. Specialized technicians at VilmaTech Online Support are always here to support you in case unexpected computer and Android problems happen.