In announcing the release of the Onefloorserve.com pop-up malware recently, based on our findings, the new version of this Onefloorserve.com malware affects on all kinds of Internet browsers including Internet Explorer, Google Chrome, Mozilla Firefox and more and is dropped by a potentially unwanted drive-by download. Just alike the previously released pop-up malware called Java-tips.net, once executed, Onefloorserve.com browser hijacker drops malicious payloads and executable files in the infectious system. And the Onefloorserve.com browser hijacker then always effort to compromise the Internet browsers and constantly exploit system vulnerabilities to get the victimized machine totally vulnerable for more attacks. The solitary of the Onefloorserve.com browser hijacker is to acquire money and steal confidential data from the infectious system. Onefloorserve.com browser hijacker is a just online fraud tactic exploited by attackers for illegal benefit-making.
Onefloorserve.com browser hijacker can infiltrate on the targeted Internet browser via drive-by download. This implies that the Onefloorserve.com browser hijacker drops into the targeted system with the help of third-party Windows programs such as freeware, shareware, web plugin, pop-up das, and more. Besides that, the Onefloorserve.com browser hijacker takes advantage of vulnerabilities in Java, Internet Explorer, and Flash Player. If the vulnerabilities were accomplishedly exploited during the campaign, pay-click malware was then downloaded on the victim’s computer. Onefloorserve.com bundled within that can slip into the targeted machine without any consent. By this way, the Onefloorserve.com browser hijacker has compromised a large number of users and the attackers could have potentially infected a substantial amount of users’ computers with malware through this attack. And then the Onefloorserve.com malware forces the compromised computer a artificially generate traffic to generate revenues for attackers.
For the most important part, the Onefloorserve.com malware can collect confidential information including log-in credentials, online transaction data, banking data and other financial information from the victimized machine. The attackers injected an IFrame into the Onefloorserve.com browser hijacker which redirected users to an established perilous website or pop-ups. This Onefloorserve.com browser hijacker in turn sends victimized users to highly hazardous searches in order for boosting malicious traffic. In another word, the Onefloorserve.com browser hijacker alters with all default Internet settings, searches, homepage, and more, and overlaps them with hazardous sites, as doing so can attackers quickly collect sensitive information and steal them from the web browser, local disks, and devices. Therefore, never belittle the Onefloorserve.com malware. You’d better remove such malware from infectious PC as quick as possible incase of further damage.
Note: How to definitely remove the Onefloorserve.com? If you need professional help now, you can Live Chat with VilmaTech 24/7 Online Experts.
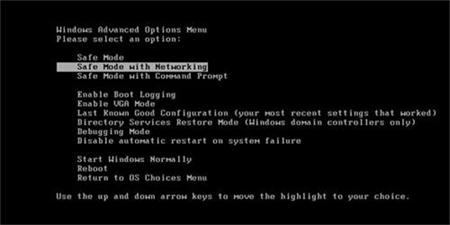
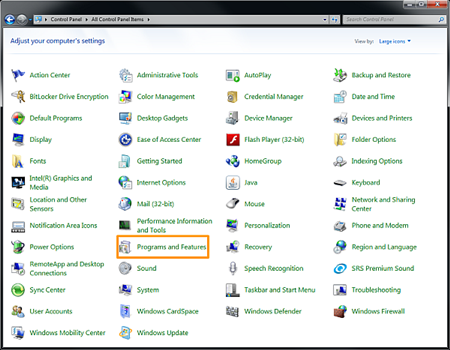
A: For Windows 7, Windows Vista
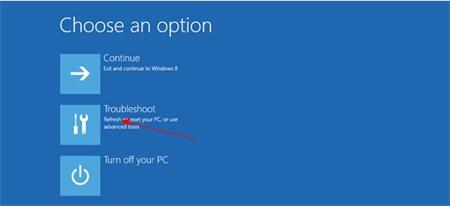
B: For Windows 8

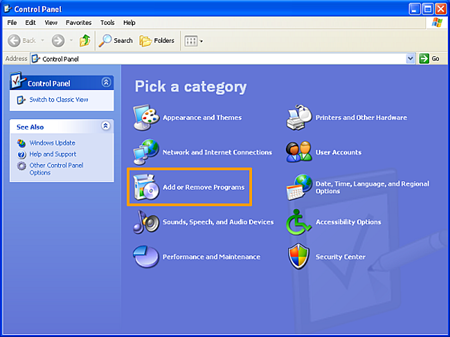
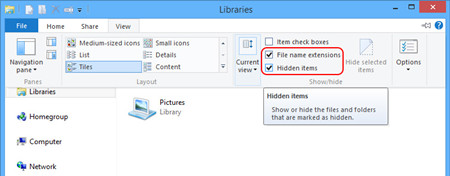
After the steps mentioned above, you still need to remove all left files about the Onefloorserve.com browser hijacker. To accomplish this step, you have to show hidden files first, follow the below tips please.
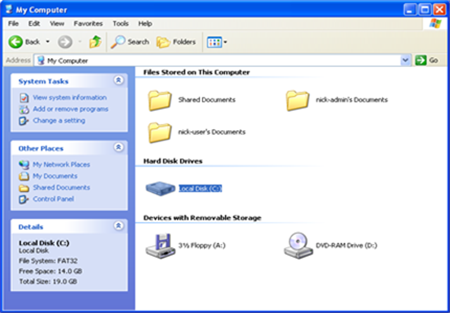
A: Windows 7, Windows Vista,

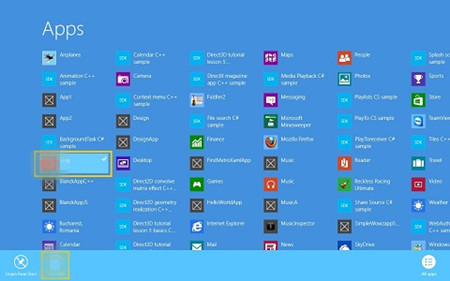
B: For Windows 8, Locate at the Metro.
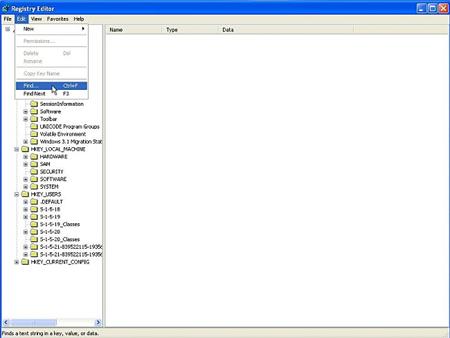
C: Delete shown files about the Onefloorserve.com pop-up malware.
Onefloorserve.com is regarded as perilous browser hijacker that focuses on redirecting defaults to malicious site and rendering various pop-ups in order for malicious benefit-making. The primary thing is the Onefloorserve.com browser hijacker can allow hijackers collect and steal confidential information from the compromised system and web browsers. From this point, the victimized users have to face incredible sensitive information leakage. The attackers can access the infectious web browser via backdoor and then track browsing histories, cookies, log-in details of social media to acquire beneficial information. By redirecting victimized users to malicious web sites or pop-ups, the Onefloorserve.com malware can inject more malware into the same victimized machine just need potentially unwanted one-click download. In a word, the best way to avert from further damage and resave the infectious PC is to remove the Onefloorserve.com completely. Till now if you still need more help to fix the virus, you can live chat with VilmaTech 24/7 Online Experts.