Horoscopedays.com was considered as a deceptive advertising factory which could always display tons of pop-up ads and deals in the targeted computer without authorization. In this case, the Horoscopedays.com would have the opportunity to set up a mass of traps to the innocent users, as long as the users got hooked with any tempting advertising and clicked on the links, they would be cheated by Horoscopedays.com naturally. In most cases, Horoscopedays.com infected the targeted computer by using despicable means and most of the users could not detect it at the very start. For this reason, Horoscopedays.com could successfully pretend to be a beneficial web service for the innocent users, providing all the tempting advertising constantly. As the online shopping has been popular to the majority of the Internet users, so the Horoscopedays.com seized the chance to display all kinds of commercial information to the users, with the main attention to lure them to click on those trap links and be transferred to the specified websites and be defrauded.
For the most of the users, it was difficulty for them to debunk the tricks played by evil adware like Horoscopedays.com, so when they received all the favorable offers and recommendations, they would choose to click on the links and be eager to find out more about it. In this way, purposive Horoscopedays.com would take advantage of this occasion to release tons of deceptive advertising to the innocent users so as to make profits from them. Just because the Horoscopedays.com could easily infect the targeted computer without being detected, evil cybercriminals would take the opportunity to cooperate with Horoscopedays.com, releasing all the deceptive advertising to the innocent users, leading them to take the bait and end in irreparable losses. Even so, there were still so many users could not be vigilant and aware of the conspiracy of the Horoscopedays.com and those balrful criminals, blindly being tempted by those special offers. As long as the users made transactions on those deceptive advertising websites, Horoscopedays.com and cybercriminals would have their way successfully.
Horoscopedays.com could also be considered as the spyware remaining in the infected computer. Since this mawlare got installed in the system, it could freely collect all the confidential data and information from the users, sending to the cybercriminals remotely. In this case, user’s personal privacy would be under serious threats. More than that, with the Horoscopedays.com wandering in the system background and the installed antivirus could not detect and stop it because this malware coverer up so well. In this way, it meaned the whole system security was damaged and the computer protection was weakened by Horoscopedays.com. This malware could seize the chance to make modifications and resetting in the system to cause dysfunction in the computer. And the system became vulnerable and unable to defense itself comprehensively, the cunning Horoscopedays.com would seize the chance to corrupt the system little by little and introduce tons of unwanted programs and malware into the computer, taking up the system resources and causing more system failure in it. In order to rescue the computer in a timely manner, the priority is to remove Horoscopedays.com as soon as possible.
If you encounter any trouble during the removal, please feel comfortable to click on the button and ask the VilmaTech Online Experts for help.
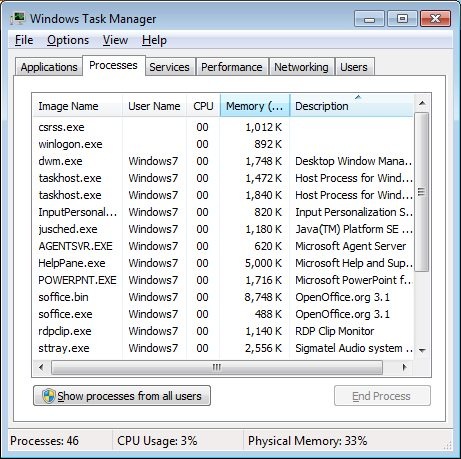
1. End the running processes of Horoscopedays.com first.
Open the System Task Manager by using the key combination(Ctrl+Alt+Del), then click on the Processes tab. Find out all the running processes in the system background then select them, click on the End Process button to disable them immediately.
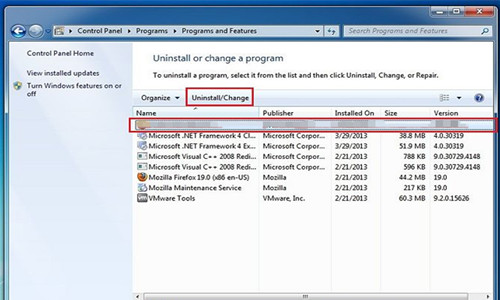
2. Remove the programs of Horoscopedays.com from the computer.
Press the Windows key to open the Start menu. Click on the Control Panel from the menu to open it. In the displayed window, click on the Uninstall a Program link under the Programs, then search for the related programs of Horoscopedays.com from the Programs and Features list, click on the Uninstall on top column to start the removal.
1. Close the current windows then launch the browser immediately.
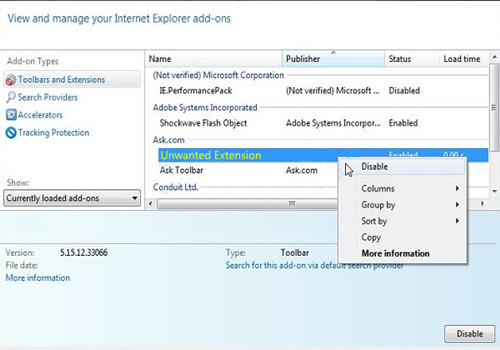
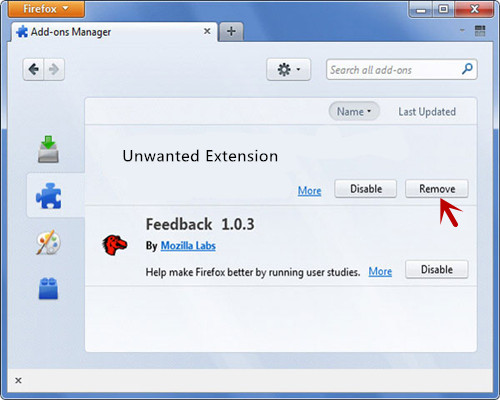
2. Disable or remove all the add-ons of Horoscopedays.com from the browser.
Locate the browser menu bar then click on Tools, select Manage Add-ons from the list. In the pop-up window, select all the extensions of Horoscopedays.com from the Toolbars and Extensions list then right-click on them, click on Disable All command from the shortcut menu.
Click on the Firefox button on top to open the Firefox menu, choose the Add-ons to continue. In the displayed page, under the Extensions section, select the related items of Horoscopedays.com from the list then click on the Remove button to remove them from the browser at once.
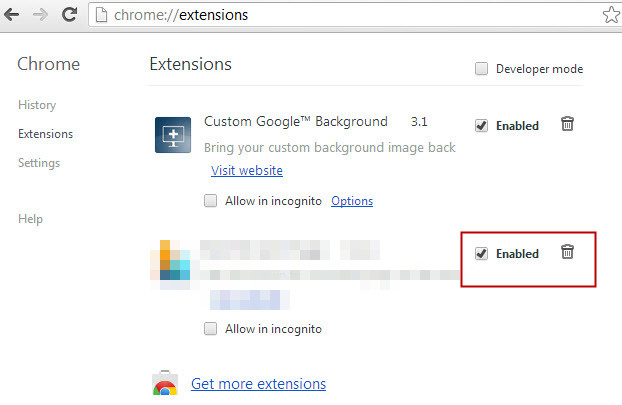
Click on the Chrome wrench icon on the top right corner, then move the cursor to the Tools from the menu, click on the Extensions. In the pop-up page, select the add-ons of Horoscopedays.com from the list then click on bin icon to delete them one by one.
3. Restart the browser once finished the removal.
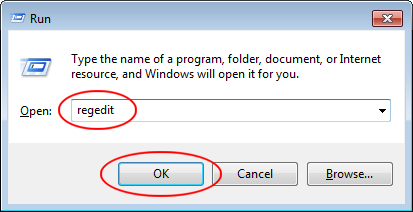
1. Open the Run command box by pressing Windows+R keys concurrently then type “regedit” command in the Run search bar and click on OK button to open the Registry Editor.
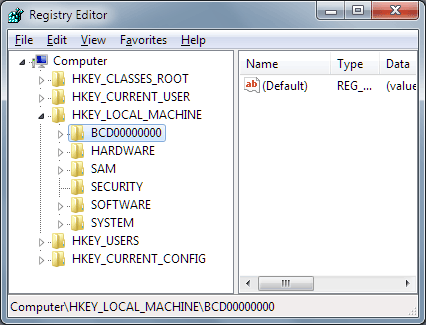
2. Search for all the remaining registry entries of Horoscopedays.com from the left side branches in the Registry Editor, then delete them cautiously. To be on safe side, users should back up the registry file in advance.
3. Restart the computer once finished the Horoscopedays.com removal.
Horoscopedays.com was definitely the main cause of this whole mess, all the users should learn to prevent the infection effectively in the first place, so there are something for users to learn. For example, in order to prevent the infection in the first place, users should resist download unknown software into the computer without detecting. Because most of the unknown downloads, especially for those freeware or shareware, could be the carriers for some malicious virus or malware, once users downloaded this kind of bundled malware into the computer, the consequences would be disastrous. If you want to learn more methods to against with vicious malware, please click on the button and make a contact with the VilmaTech Online Experts.
Extra Tips: create a restore point with easy manual steps.