Judging from adfocus.us’ name and its content, it can be considered as adware; while the way it acts defines it as a browser hijacker – a suit of programs classified as Potentially Unwanted Program (PUP) rather than virus due to the lack of vicious attribute code and the application of approved computing technologies.
Browser hijacker rose in response to the need by most e-commerce businesses and black hat SEOs to generate huge leads and traffic without competition complying to the fair mechanism. And it is true to adfocus.us. Offering a list of links while hijacking users’ browsers, adfocus.us manages to direct traffic to the publishers and advertisers who have delivered payments. Not serving as virus, adfocus.us shall not be kept on browsers, according to VilmaTech Computer Security Team, not because of the detriment on surfing experience, but also because of the potential dangers it is capable of triggering.
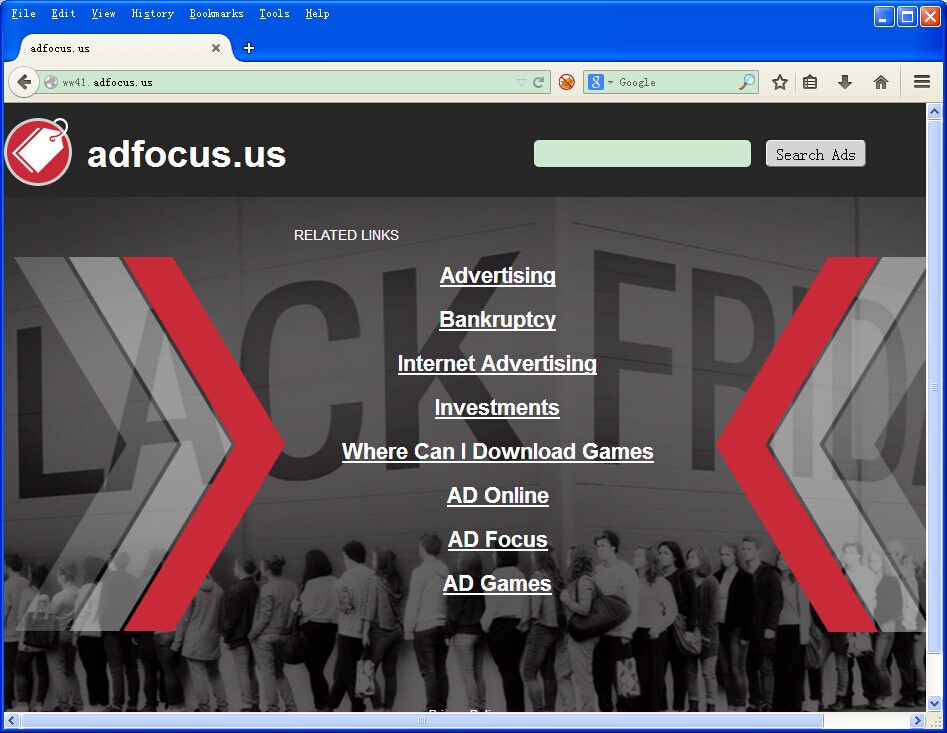
Applying approved computing technologies, adfocus.us is nevertheless potentially dangerous. Showing up in the form of a web page, adfocus.us can be concluded to adopt JS and BHO (Browser Helper Object) techniques that were created for easy and quick web browsing. Given the fact that the hijacker is money driven, it is unascertainable that adfocus.us would resell the confidential information contained in cookies including browsing history and even log-in credentials to the party in need for either high ROI or scam.
What’s worse, loophole/vulnerability is very likely to be detected within its Java Script since adfocus.us has no intention, according to the arbitrary and annoying behavior, to develop long-lasting relationship with any party, no exquisite work will be involved. And the programs with loophole/vulnerability are the targets by infections. In the event that adfocus.us is eroded by virus, the victims of it will be affected immediately and the personal information fetched by the hijacker will be grabbed which can lead to identity theft and even money loss.
Briefly, the sooner adfocus.us is removed, the better. Given the fact that adfocus.us is not technically virus, which anti-virus program will not be able to solve, manual way is highly recommended. Stick to the steps below for thorough removal. Should there be any problem occurring in the middle of the process, you are welcome to contact VilmaTech Online Support by pressing on the live chat button below for specialized technical help.
Step1. uninstall/disable/remove extensions created on/after adfocus.us appeared.
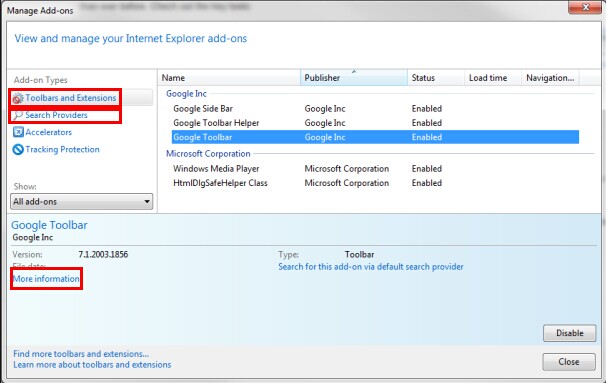
Internet Explorer
Unfold Tools menu to select “Manage add-ons”; please then look into “More Info” for the creation date to remove/uninstall/disable the one(s) created on/after adfocus.us appeared.
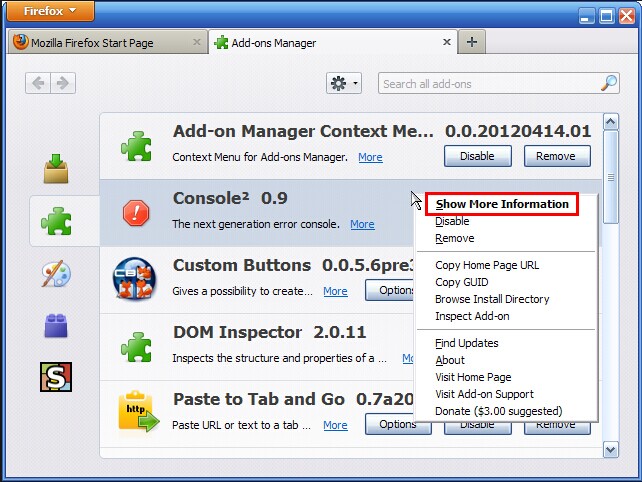
Mozilla Firefox
Select “Options” from Tools menu; enter into ‘Add-ons’ and locate ‘Plug-ins’ panel; remove/uninstall/disable the extension(s) according to creation date shown in “More Info” section.
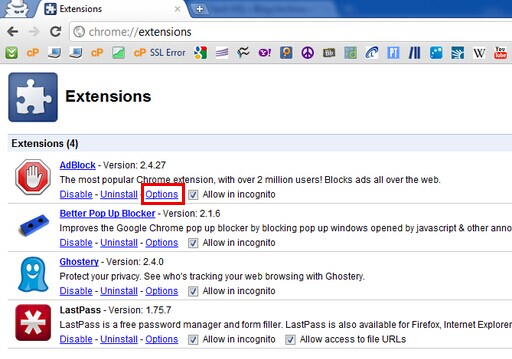
Google Chrome
Hit the spanner icon to select “Tools”; in ‘Extensions’ window, check for the creation date before removing/uninstalling/disabling the relevant extension(s).
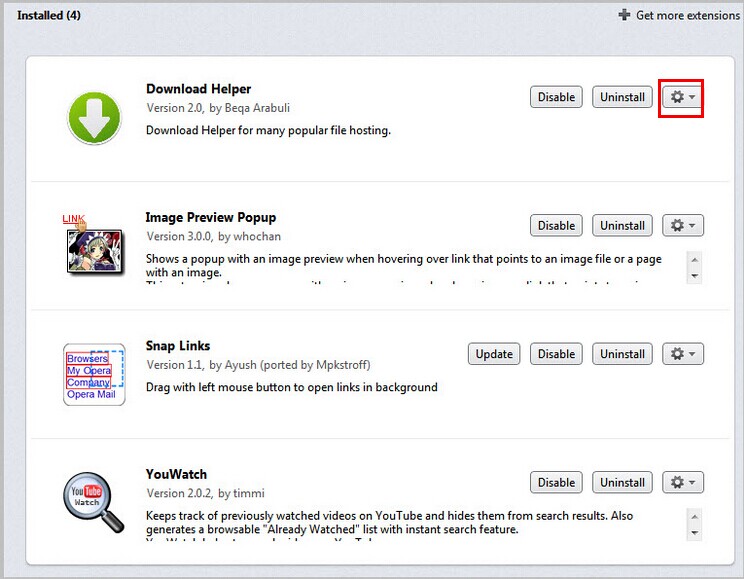
Opera
Choose “Extensions” in Opera’s menu and enter into “Manage Extensions”; remove/uninstall/disable the extension(s) according to creation date.
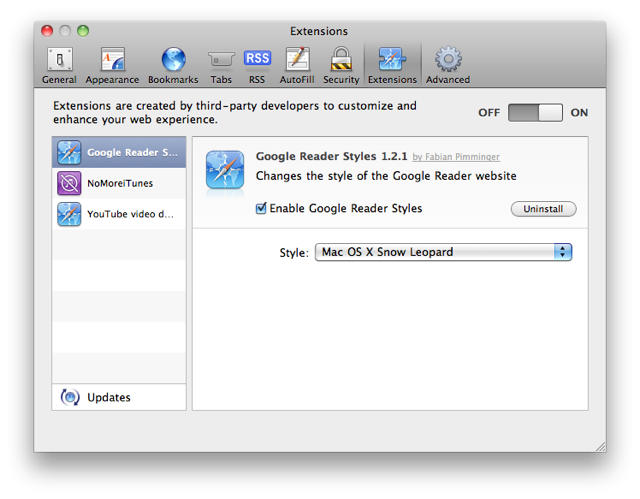
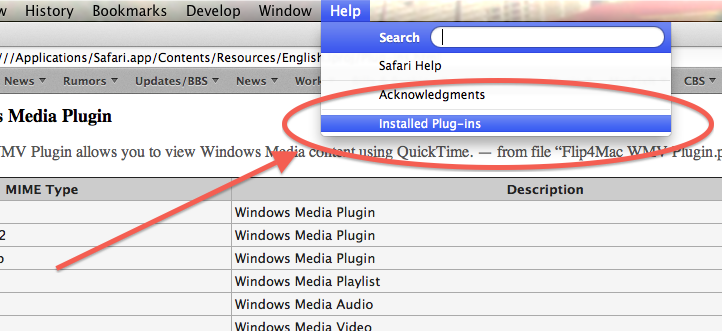
Safari
Step2. disable/remove the service relevant to adfocus.us hijacker.
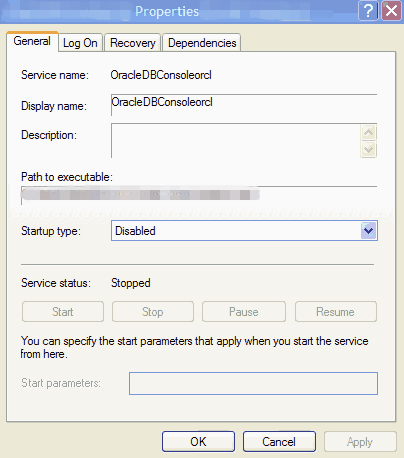
For Windows7/vista/XP
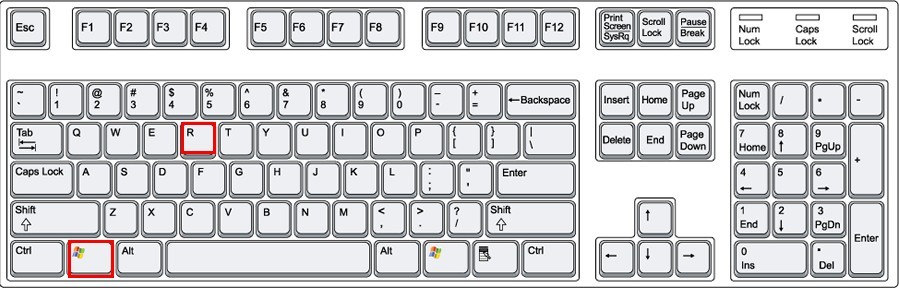
Use Win+R key combination to enable Run box; enter “services.msc” in and hit Enter key will you be led to System Service window; check the enabled services you didn’t see before to remove/disable the ones with “Path to Executables” directing to adfocus.us’ path.
For Windows 8
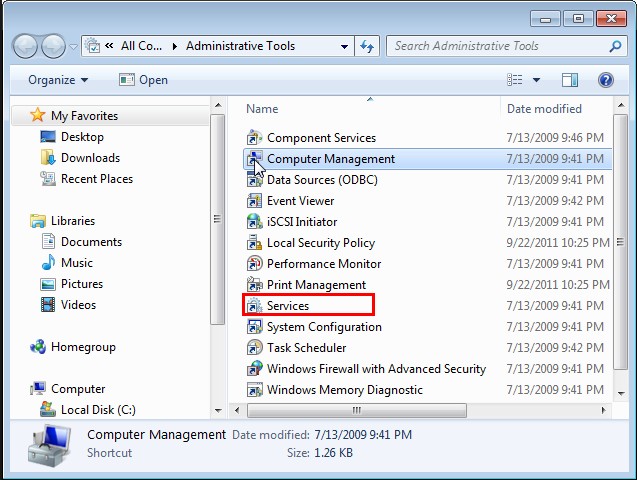
Access Windows Explorer from Start screen and choose Administrative tools to continue; enter into service window through Services icon and remove/disable the service(s) with “Path to Executables” directing to adfocus.us’ path.
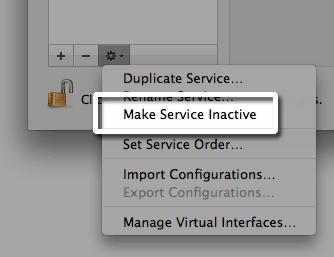
For Mac OS X
Access Finder menu to choose “Services” for “Services Preferences”; navigate to “Services” on the left pane and check the service(s) on the right; non-tick the box next to the relevant service(s).
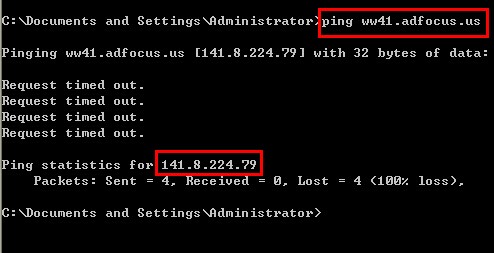
Step3. Rectify Hosts file to stop adfocus.us from hijacking.
For Windows
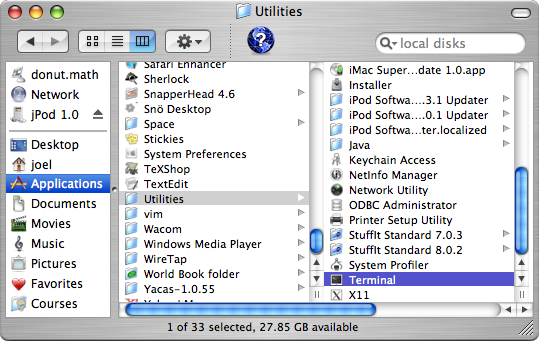
For Mac OS X
It can not be clearer that it is an emergency to get rid of adfocus.us browser hijacker. But the additional items brought in by the hijacker may thwart the removal as the above offered steps are exclusively tailored for adfocus.us. For more solutions to the unexpected situations, you are welcome to get one at VilmaTech Blog, or simply get online PC security service by bringing up the live chat window with the button below.
Apart from the executable files supporting adfocus.us’ unacceptable behaviors, there are data files and the like dropped for operational coordination. Generally speaking, such files are scattered around to bring about unreasonably utilized computer space. To regain the satisfactory PC performance, it is advisable to defrag disks after the complete removal of adfocus.us. Here’s the video to show how:
Serving as a money-driven program, adfocus.us would seize any chance to get more. The scenario caused by the hijacker include, inter alia, bringing in additional applications. Here’s the list of unpleasant scenes observed by VilmaTech Computer Security Team: