A large number of Internet users were compromised and used to pin links to a spam malware called SearchAssist.me. Since most of the compromised Internet browsers including Internet Explorer, Google Chrome, and Mozilla Firefox ware linked to the established SearchAssist.me spam site, they hardly bypass a series of perilous pop-up ads and any other things associated with the SearchAssist.me malware. The SearchAssist.me web spam malware is carefully crafted by cybercriminal gangs in order for running malicious payloads, boosting perilous traffic, taking over the victimized machine and then stealing banking credentials, support peer-to-peer communications, and spread over the social media such as Facebook. The SearchAssist.me also refers to the so-called browser hijacker, which can tamper with default the Internet settings and overlap them with hazardous pop-ups. The defaults including search engine, startup, new tab, homepage and more must be altered with SearchAssist.me and its components.
Just alike the Slowpcrepair.net, a similar malware originally appeared in 2014. The attackers just exploit such trick to lure online users into being trapped and then effort to collect confidential information for illegal benefits-making. The SearchAssist.me malware can be bundled with freeware, shareware, or other third-party Windows programs so that they can fast infiltrate on the targeted users’ computer without any consent just when users download those potentially unwanted programs. SearchAssist.me malware then can constantly exploit system vulnerabilities to give a rise to total system failure on the infectious PC. Besides that, the SearchAssist.me malware still can use a maliciously crafted document to attack online users’ computers. Usually, those crafted documents execute malicious macros, an infection method that far from advanced but works to the cybercriminals’ advantage, as doing so can attackers compromise the targeted machine with ease. SearchAssist.me is an onslaught attack becoming more prevalent over the cyber world. In case of further damage, the SearchAssist.me malware should be removed completely.
Tips: The safest and quickest way to remove the SearchAssist.me malware from the victimized machine is through the manual way. If need professional help, you can Live Chat with VilmaTech 24/7 Online Experts now.
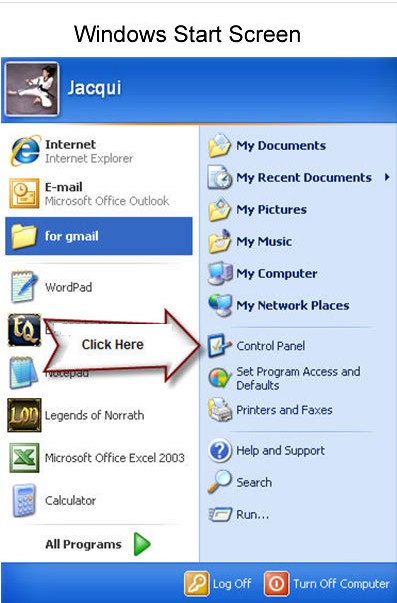
1. Click Start menu, locate at Control Panel option, and open it.
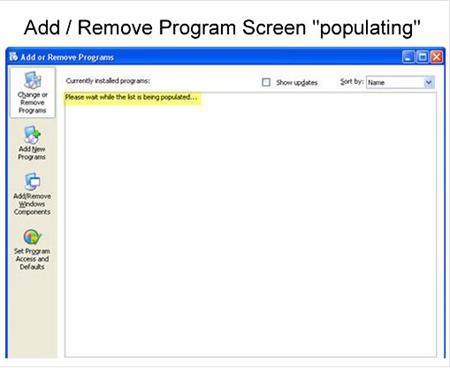
2. Next is the Control Panel Interface. Locate at the Add or Remove Programs option and open it.

3. Wait for a while, all installed programs are loading.
4. Scroll down and click on the unknown program related with SearchAssist.me malware. You then select Remove Option.

5. Make sure you want to get the target program uninstalled from the victimized machine completely. You then click Next button-> Uninstall button->Click Finish.
1. Open the Control Panel now. For Windows 8 users, reach the desktop now. And then just move the mouse cursor around on the Start screen to reveal a new Apps button.

2. Click the Apps button and the he Apps view will show up. Find out the search box.

3. Type the control panel in the search box. Click on Control Panel to open it.

4. On Control Panel window, open Uninstall a program. And locate at the unwanted program associated with the SearchAssist.me malware. The left steps are just like the steps mentioned above.
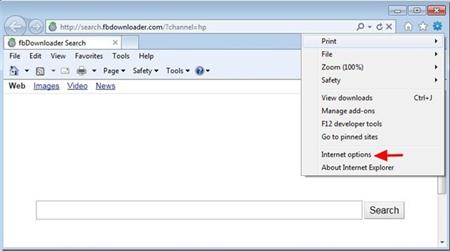
1. Open the Internet Explorer.
2. Click Tools and open “Internet Options.”
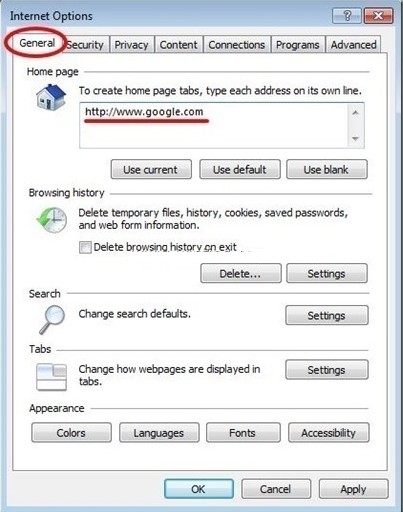
3. Now you may locate at the General tab from pop-up window. Remove the SearchAssist.me from “Home page” box and type your preferred Home Page. And then press “Settings” in Search section.
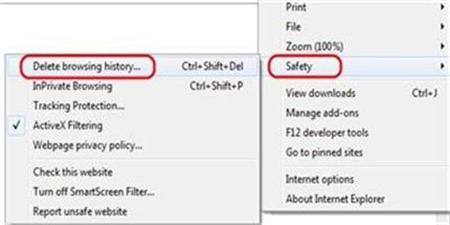
4. Come back Tools, you need select on Safety and then click delete browsing history.
5. To delete all cookies, uncheck the Preserve Favorite Website Data box, check the box next to Cookies, and hit Delete.
6. Restart the Internet Explorer. And then reboot the infectious computer.
SearchAssist.me hijack virus may cause one major data breach containing encrypted password, login-credentials and other financial data. The SearchAssist.me browser hijacker focuses on performing some unauthorized activities and accessing to financial information. The scale of the SearchAssist.me malware damage is difficult to understate. In the SearchAssist.me attack, the system can be completely compromised and even failure, all programs installed on the infectious machine can be disabled, and even all sensitive data stored on memory, browser, and devices must be at high-risk of exposure. There’s really only one thing that victimized users have to do to in case of further damage: remove the SearchAssist.me malware completely. Once the SearchAssist.me left on the victimized machine long enough without a fix, attackers can acquire much more time to do anything benefits them. Do you still need more information about the SearchAssist.me malware removal? You can live chat with VilmaTech 24/7 Online Experts