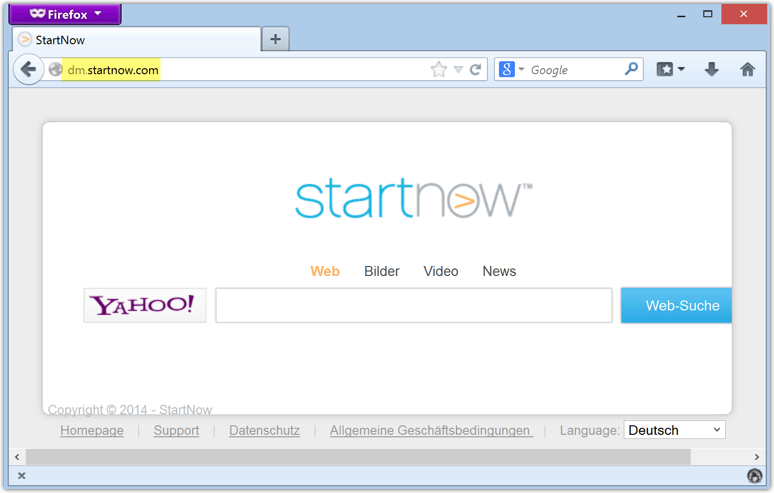
Dm.StartNow.com is another variant of startnow browser hijacker. It is a lame BHO, which can be told from the below listed detections:
As a matter of fact, dm.startnow.com is a browser hijacker to replace default homepage, search engine and new tab permanently. This is serving for only one purpose which is money. But the purpose is hidden by the browser hijacker well. It doesn’t show up ads on its interface like what MyAllSearch.com (read more) does, while it does search like what Google does except some unusual scenarios that would help us figure out the difference dm.startnow.com has from an average search engine:
Note: annoying as it is found by most PC users, dm.startnow.com is not a virus. Then what is it, is it dangerous and why it keeps annoying people without being removed by anti-virus programs? To get the answers, VilmaTech Online Support would suggest a continuous reading to enrich the knowledge and to finally get the effective solution to the browser hijacker. Questions will be gladly answered as soon as a live chat window is opened up.
It should be widely informed that what anti-virus program bases on to catch a virus is virulent attribute code. Without the code, security utilities are not that smart enough to perform the task.
As what has been made clear on the preceding paragraphs that dm.startnow.com is a BHO, it is one of the numerous browser hijackers to work for huge traffic and direct traffic to other operators that dm.startnow.com has cooperative ties with. In short, dm.startnow.com is a promotional tool. With BHO, JavaScript technologies, the browser hijacker manages to load its data files into system configuration and have browser settings changed. It is allowed as the technologies were created to do so for a better surfing experience. In this way, dm.startnow.com is not fighting against anti-virus program, it is just not a virus.
People would instinctively believe that items that are not picked up by security programs are safe since they are too dependent on the automatic programs. Remember BitCrypt ransomware? It is not detected by anti-virus programs even in Safe Mode when it is blocking the whole screen. So now let’s learn some potential dangers by dm.startnow.com browser hijacker.
As we learned from the above section that dm.startnow.com is one of the many promotional tools, it is not therefore strictly built. In other word, its structure is loose and bug can be easily detected to give chance for malicious infiltration. It could be even worse once the bug is exploited by infections embedded on the Internet due to the technologies dm.startnow.com adopts.
BHO technology helps to preload data file into system configuration to ensure automatic launch at each Windows start for saving internal storage while JS technology is utilized to re-configure HTMLs for the warranty of easy access to accounts by remembering the log-in information and shortcut to certain sites, like google.com homepage. Once the technologies are taken advantage by infections, they’ll assist in launching vicious codes automatically for continuous evil deeds and recording log-in credentials for identity theft.
Note: after reading this section, one should be now clear that it is better to remove dm.startnow.com as soon as possible. It’ll be complicated when dm.startnow.com is captured by infections and the removal will become much more cumbersome accordingly. As anti-virus programs are not going to help deal with dm.startnow.com issues, manual removal thread is offered below. Stick to the steps and help yourself and please do feel free to contact VilmaTech Online Support for specialized technical help if you run into difficulty and confusion due to deficient computer knowledge.
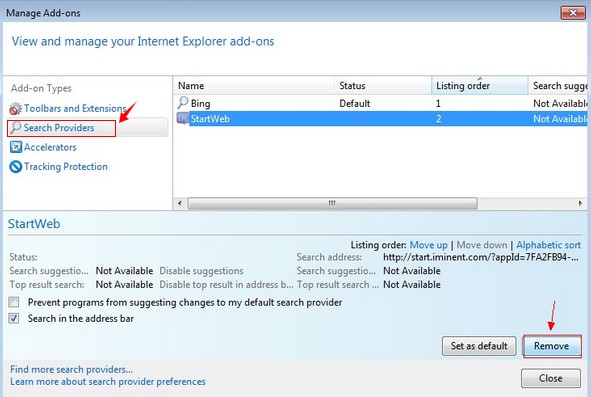
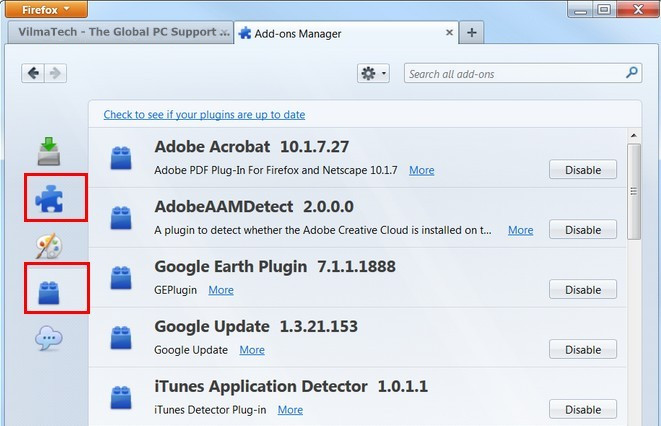
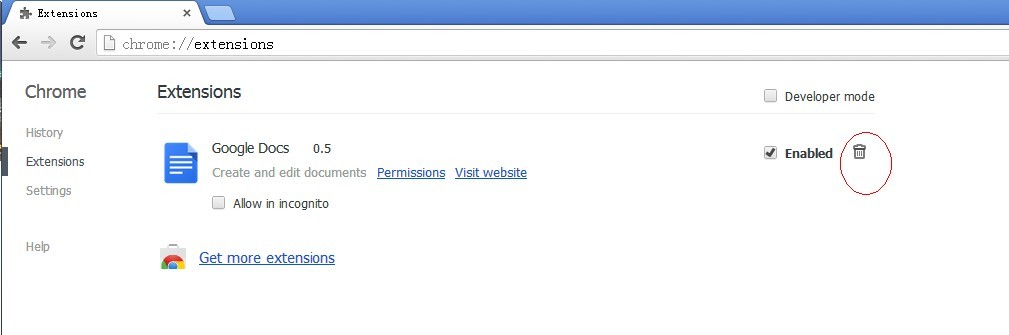
A – Remove dm.startnow.com search engine from browser setting.
Internet Explorer
Firefox
Chrome
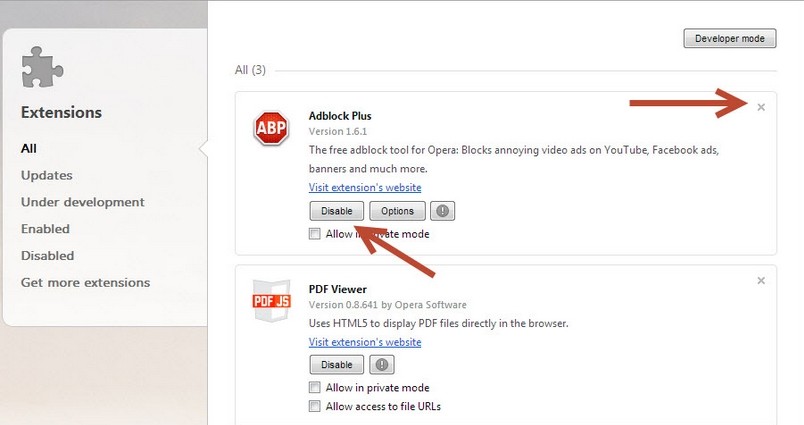
Opera
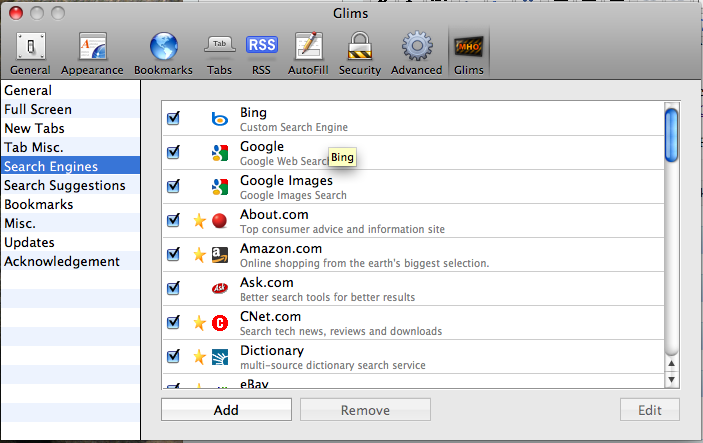
Safari
B – Change homepage URL from dm.startnow.com.
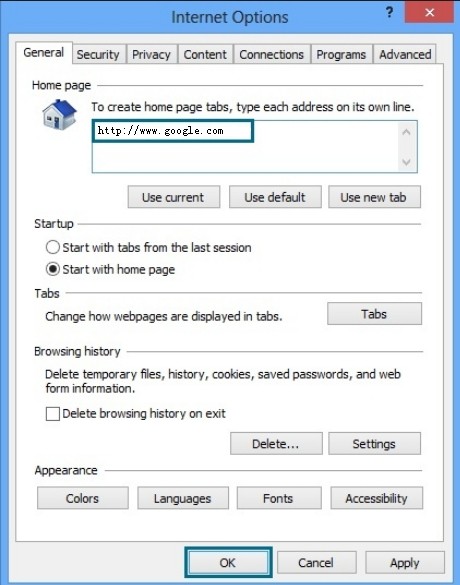
Internet Explorer
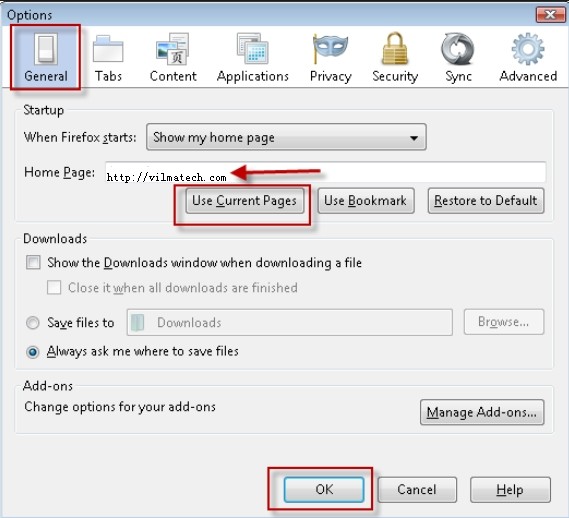
Firefox
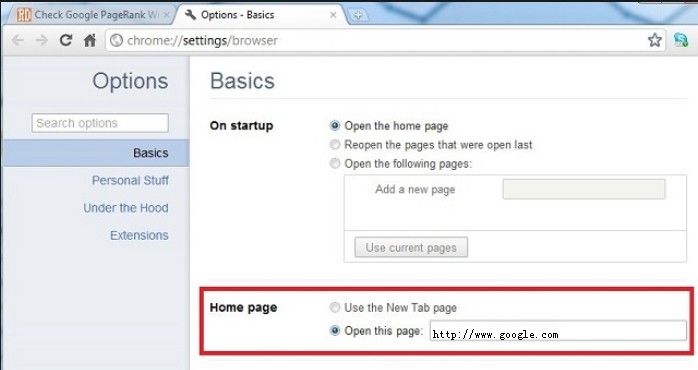
Chrome
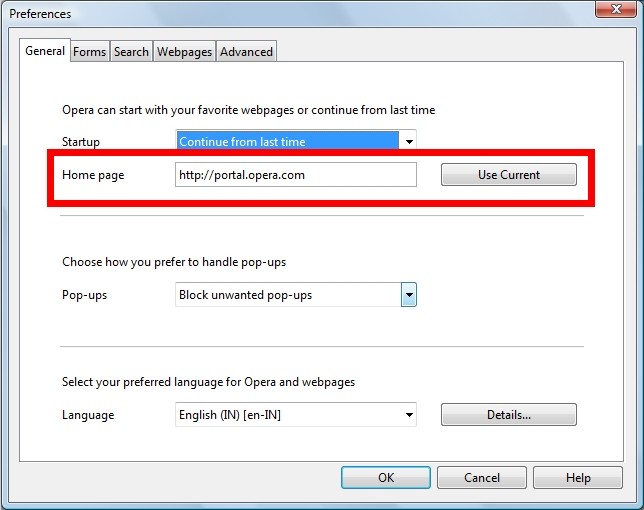
Opera
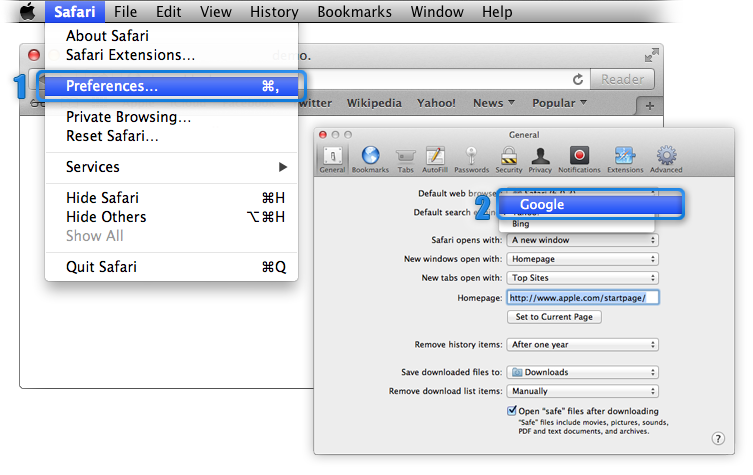
Safari
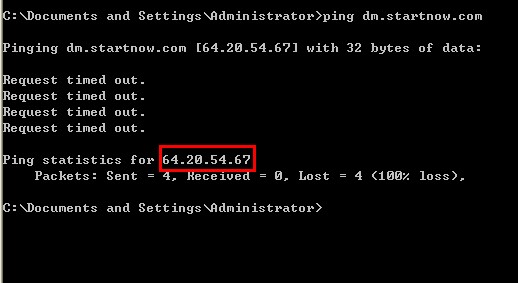
C – Modify Hosts file to block dm.startnow.com.
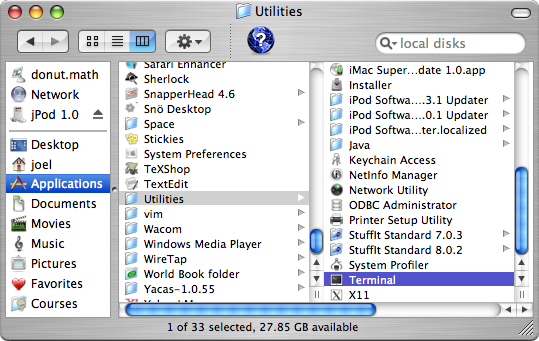
For Windows users
For Mac OS X users
Dm.StartNow.com is not a virus; instead, it is a browser hijacker (categorized as BHO) to help intercept traffic. When online shopping becomes a rage nowadays, fierce competition can be seen everywhere. With more traffic, the operator gets high rank. Then how to outshine other competitors when white SEO has been fully learned and plays by operators? Some new starters start targeting browser hijackers like dm.startnow.com. To get more traffic from one computer, dm.startnow.com utilizes BHO and JS technologies to stick to a machine. Due to the legality of the two technologies, dm.startnow.com is not picked up by security utilities.
As a piece of freeware, dm.startnow.com needs funds to keep going. With the huge traffic it intercepts, dm.startnow.com manages to attract co-operations with many freeware/shareware/adware. Therefore, installing a third-party program with “recommended” method would result in dm.startnow.com harassment as the browser hijacker would be placed as one of the sub-options in the installation package; clicking on random adware could lead to dm.startnow.com hijacking as promotional tools would cooperate together for a more aggressive promotion.
Being loosely built, dm.startnow.com has apparent bugs; directing traffic constantly to online operators’ sites, the browser hijacker will caught the attention from infections. Consequently, additional infiltration can happen if delay is ever made to the removal or the target machine is poorly protected. If it is the case, victims are advisable to remove all the infections before removing dm.startnow.com as the additional infections and damages thereby would hinder complete removal, which would not stop the appearance of vulnerability/loophole/bug to be exploited by random virus. Want solutions to the infections that worm into the vulnerable machine by dm.startnow.com? Browse to virus reservoir; or simply consult security advisers from VilmaTech Online Support for quick fix according to your concrete situation.
The mechanical damages or malfunctions caused by infections would deter quick fix to some extent. If you found your computer becomes poor in performance after getting dm.startnow.com, it is recommended to create a restore point after a complete removal so that the next time, just in case, you get a virus, simply perform a system restore will relief the troubles and enable a quick fix to rescue your computer, though the restore can’t help exterminate a virus thoroughly. Here’s the video to show how to create a restore point: