This article is especially written by one of the professors from Global PC Support Center to enrich the knowledge about trovi.com and its incidental dangers whereas the increasing number of victims has been lasting for quite a period of time.
Trovi.com is not a virus at all. However being identified as PUP (potentially unwanted program) does make people concerned. Without vicious infiltration routine trovi.com still manages to stick to a target machine just like what haunting infections do, which imputes to BHO technique and JS technique.
From the two techniques, its propagation way can be figured out and the inference fits the fact. Trovi.com can be detected after web vulnerability being made and drive-by download. Worming through web vulnerability was originally the most principle means. After obtaining large amount of traffic, its propagation way has changed into the latter one due to the fact that high traffic equals high exposure rate, which brings in a lot more potential transactions.
Also with the two techniques, trovi.com is enabled to perform the following baleful deeds:
All these are meant to intercept traffic and redirect it to its partners. By doing so, the maker behind trovi.com manages to gain commission. It is inevitable that additional advertisements appear whenever and wherever possible as trovi.com is a freeware. It needs fund to keep its operation. Also it is unavoidable to encounter spam sites most of the time. To defraud people into handing over money or to get soaring number of visitors for more potential transactions, operators will pay heavily to be trovi.com’s partners. With additional items being brought in, dysfunctions and uncertainties would occur. You are welcome to finish reading and get to know about dangers lurking beneath its calm surface. Should you meet difficulties, please feel free to resort help from VilmaTech Online Support.
By implanting its components into startup configuration and service with BHO and JS technique, trovi.com manages to redirect targets to partners’ sites without being interfered by installed anti-virus program due to the functions of the two techniques are originally used to customize surfing experience. When modified DNS settings becoming susceptible to more types of online spam including pop-up ads, more unknown items accumulate in browser settings, causing tardy performance and response.
What makes targets concerned is that such obvious phenomenon can be easily detected by infections concealed in the Internet. Being modified randomly by trovi.com with BHO technique, a target machine becomes readily to be affected as BHO can be utilized to help download .dll/.exe file (the type that almost all infections employ) without being examined. At the moment of settlement, JS technique will be soon exploited to help redirect to designated DNS, making invisible backdoor easily and possible; it can impose a lot more trouble to the target since backdoor has long been applied in helping with infiltration. What’s worse, JS technique, as a part of web browsers to allow client-side scripts for interaction with users, control the browser, communicate asynchronously, and alter the document content that is displayed, can be utilized to record log-in credentials, which can be fatal sometimes when online bank was once used on the target machine. With recorded log-in credential, attacker becomes able to distribute vicious code through instant chat tools, emails to all contacts and empty out bank accounts.
Mechanical damages also come with these security risks:
It is wise to remove trovi.com as soon as possible so as to stop further damages and risks. Due to the fact that anti-virus programs are not programmed to deal with items that are not virus, it is recommended to employ manual removal method for a complete removal. Follow up the below steps only when sufficient computer knowledge is available; otherwise, get professional help timely to prevent potential mistake that could complex the removal procedure.
A
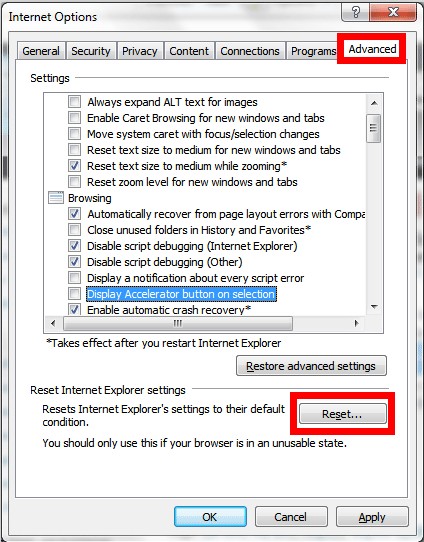
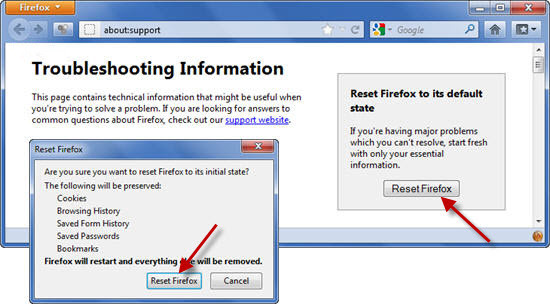
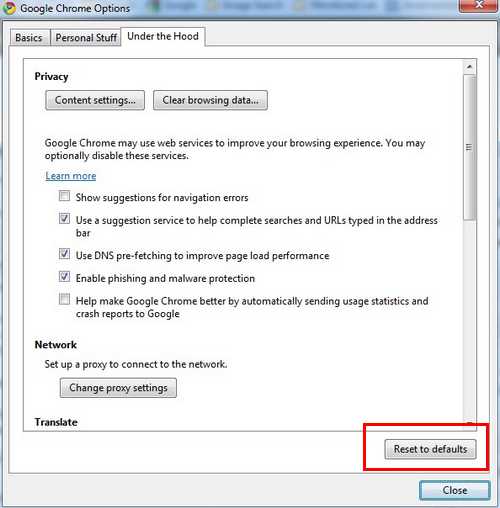
If you don’t want to check all sections to remove trovi.com one by one, it is recommended to reset browser settings.
IE users:
Firefox users:
Chrome users:
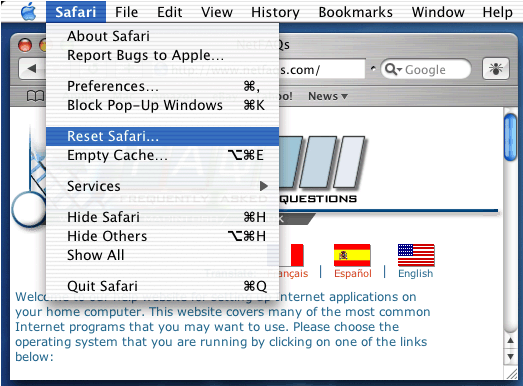
Safari users:
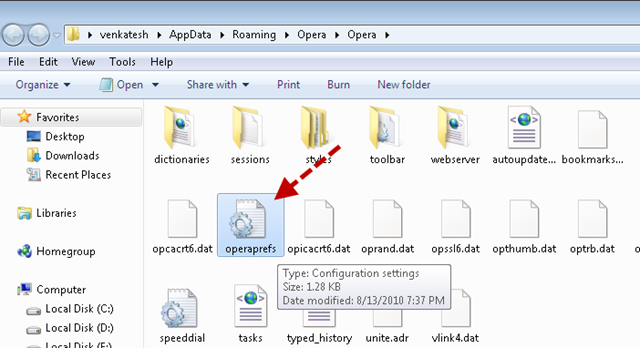
Opera users:
steps to show hidden items:
Windows 8
1. Access Windows Explorer from Start screen and hit View tab.
2. Tick ‘File name extensions’ and ‘Hidden items’ to press “OK” button.
Windows 7/XP/Vista
1. Access ‘Folder Options’ from ‘user accounts and family safety’ in ‘Control Panel’ window.
2. Hit View tab to tick ‘Show hidden files and folders and non-tick ‘Hide protected operating system files (Recommended)’.
Mac OS X
1. Access Finder to click open Utilities folder.
2. Activate terminal to copy and paste “defaults write com.apple.Finder AppleShowAllFiles YES”.
3. Hit Return button, then hold ‘alt’ key and right click on the Finder icon at once to press Relaunch button.
B
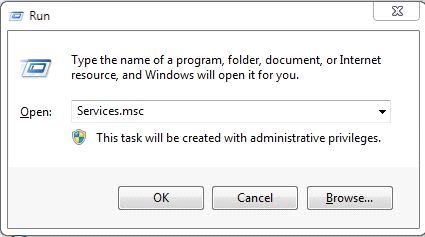
Close down the affected browser and use Win+R key combination to access Database to remove the following key values started with “Run”:
(tip: there’s no need for victims owning Macs to do so)
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\Curren Version
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders Startup=”C:\windows\start menu\programs\startup
C
Go to system service to disable/remove trovi.com’s service, if any.
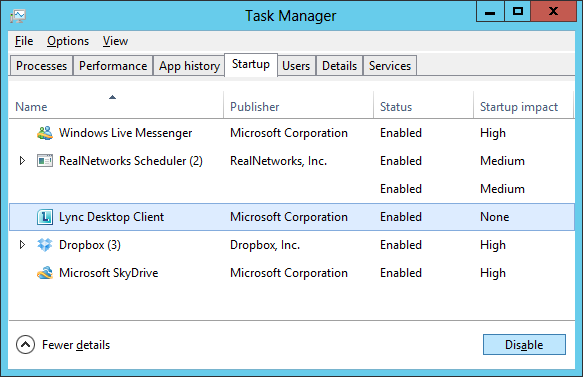
For Windows 8 users:
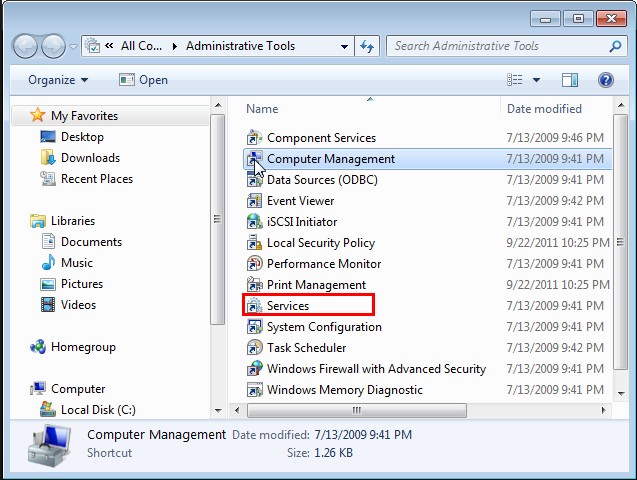
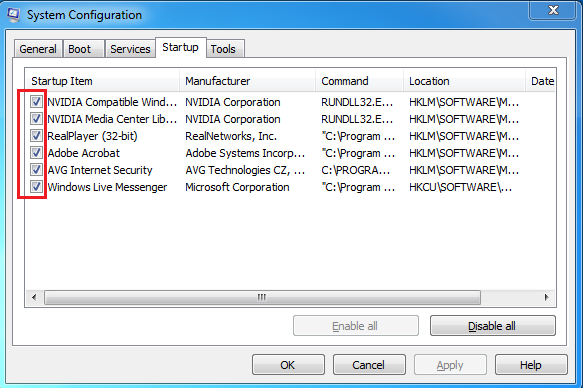
For Windows7/vista/XP users:
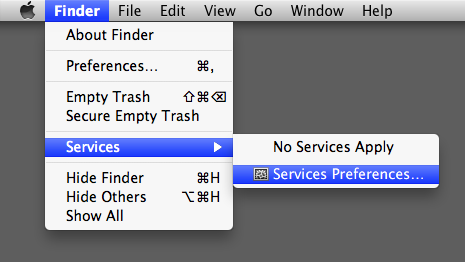
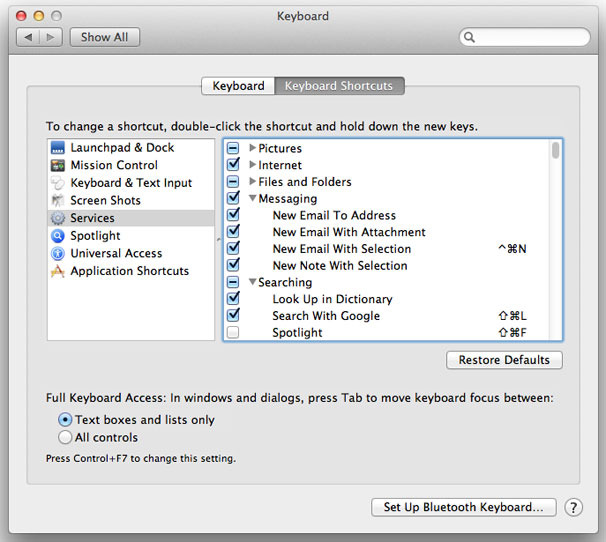
For Mac OS X users:
D
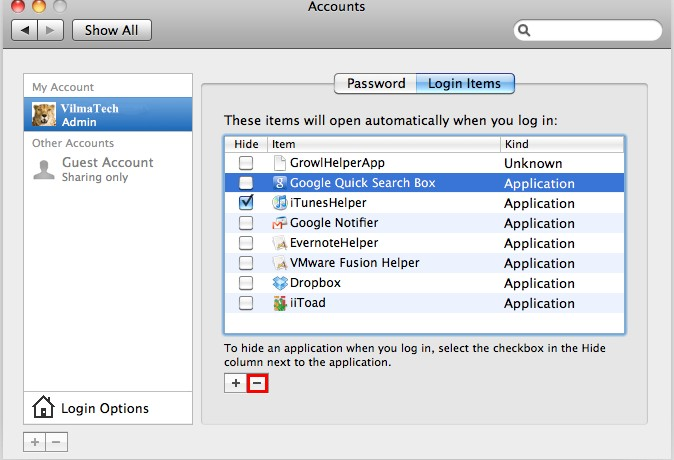
Enable startup window so as to stop trovi.com from appearing and operating on your browser.
Windows 7/XP/Vista
Windows 8
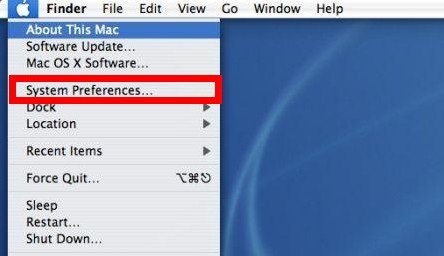
Mac OS X
Attention:
Complete removal is appealed so that no unexpected issues such as error codes will happen subsequently to keep stirring up the system. Ignorance of tiny piece of associated item may conflict with third-party program that is planned on installing in the future and even worse, there was a case where incomplete removal led to re-emergence of trovi.com. VilmaTech Online Support would like to kindly remind you of removing additional vicious items, if any, during the removing procedure since web vulnerability makes additional infiltration possible. One should remove trovi.com complying with the order as offered above; otherwise, incomplete removal can arise. Finally, you are welcome to seek specialized technical help in the event of unexpected problems.