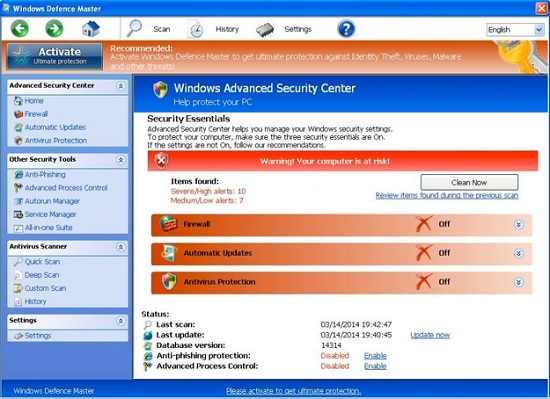
Windows Defence Master is not a legitimate security program, which generally appears to users in the form of a fake Windows warning on a targeted computer that it infects, purportedly claiming that a specific number of PC threats existed on compromised machine that should be terminated imminently. From the aspects of technology, Windows Defence Master can be categorized as a form of Internet fraud tool or Rogue security software utilized by scammers, as it always attempts to mislead users into purchasing its bogus full licensed version in order for the simulated removal of detected malware. The common measure Windows Defence Master used to increase its authenticity is to imitate basic operating principle and GUI (Graphical User Interface) from standard antivirus software, which has made a good impression for users. When initialized, this type of rogue virus will render installed security application inoperable for the sake of protect itself from auto removal.
Upon its complete installation, Windows Defence Master may immediately infiltrate into kernel system by technically implanting its malevolent codes and files. This may directly lead to the modification in default system configuration, including Master Boot Record (MBR), which takes control of the operating system bootloader and the storage device’s partition table. Thereupon, Windows Defence Master threat could be loaded up and executed automatically whenever Windows is launched. While running in affected computer, Windows Defence Master may significantly reduce the overall PC performance speed by taking up high computing resources. Similar as the Activeris Antimalware Rogue-AV infection, Windows Defence Master threat may make use of found system security vulnerabilities so that to open a backdoor for remote hackers. If this is the case, this type of rogue virus may be utilized by hackers to drop additional threats on compromised machine for further harm, and obtain unauthorized access to corrupted system. As a result, to safeguard affected computer as well as user’s privacy, it is urgent to get rid of Windows Defence Master as long as being informed of its existence.
Note: The following manual removal requires certain computer expertise. If you cannot handle the operation alone and do no want to make mistake, you’d better live chat with VilmaTech Certified 24/7 Online Experts to help you remove the virus manually without mistake.
1. Windows Defence Master may sneak into a targeted computer by attaching itself on some malicious websites or other legitimate web pages that have been assaulted by the developers of malware.
2. Windows Defence Master may spread via Trojan, which has the capability to exploit system vulnerabilities to drop and install the malware on compromised machine without any permission or knowledge.
3. Windows Defence Master may emanate from downloads or updates of certain applications, some of which are pirated or illegally acquired software programs.
4. Windows Defence Master may be propagated by some infected email, which contains sponsor links or other attachments.
Many PC users want to figure out the most effective and simple way to get rid of Windows Defence Master rogue virus. Most commonly they may attempt to have a full scan with their installed and trusted antivirus software in order to terminate Windows Defence Master virus effectively. However, different from other common PC threats, Windows Defence Master is capable of blocking standard antivirus software or other security utilities from running to avoid their auto eradication. Auto removal may be difficult to deal with this type of rogue infection effectively. In this case, it is strongly recommended to adopt the almighty manual removal, which is able to clean up all malicious components of Windows Defence Master from computer.
Please be aware that manual removal is only suggested for advanced users, as it is related to parts of kernel system. Any single mistake may lead to worse results. If you are not familiar with the process, you’d better back up Windows registry first in case of incautious mistake, or you may ask help from VilmaTech 24/7 Online Experts to avoid any mistake and remove the virus completely.
*Video Guide on How to Backup Windows Registry in Windows 8
Method for Windows 7, XP and Vista:
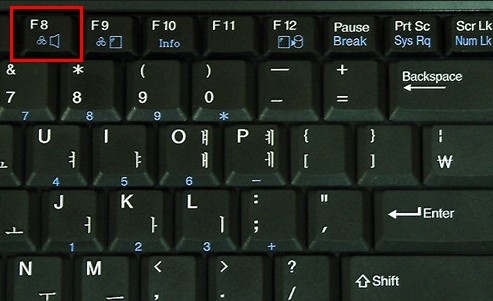
1. Start up infected PC. Keep hitting F8 key before Windows logo appears.
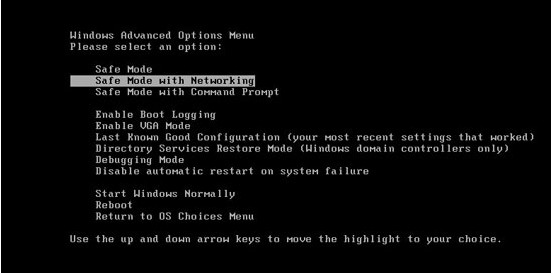
2. Advanced Boot Options will pop up later.
3. Select Safe Mode with networking and Enter.
Method for Widnows 8 users:
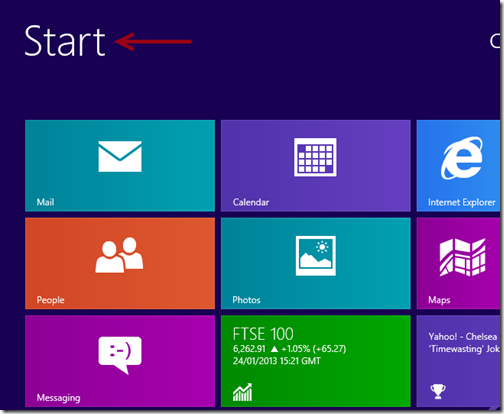
1. Reboot PC, and log in affected account.
2. When you see the desktop, click Start menu.
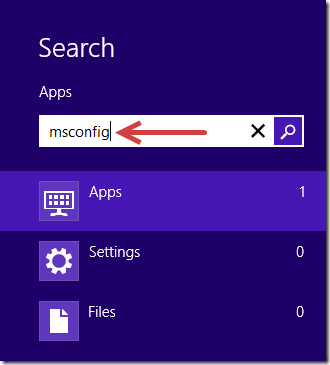
3. In the opened Search box, type msconfig in it and Enter.
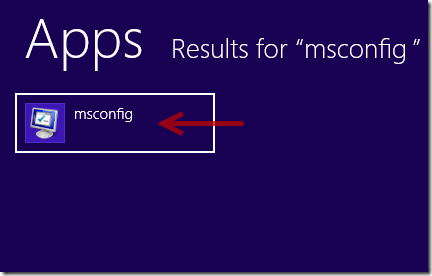
4. Next, click on msconfig icon from the search results.
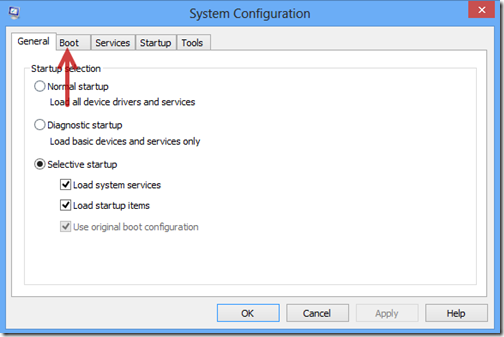
5. In System Configuration menu window, choose Boot tab.
6. Check the box for Safe Boot and choose Network option below. It will offer Internet services for you in safe mode.
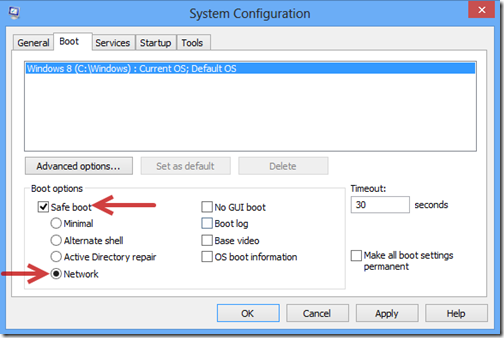
7. Select Restart.
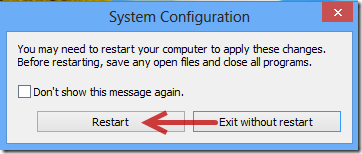
8. Later, Windows will boot into Sade Mode with Networking automatically.
1. End up the process of Windows Defence Master by opening Windows Task Manager.

2. Get rid of the files related to Windows Defence Master.
%AppData%\NPSWF32.dll
%AppData%\Protector-{random}.exe
%AppData%\result.db
%Desktop%\Windows Defence Master.lnk
%StartMenu%\Programs\Windows Defence Master.lnk
3. Clean up all the registry entries of Windows Defence Master.
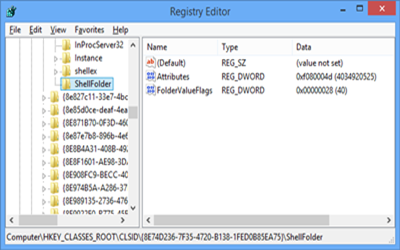
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings “WarnOnHTTPSToHTTPRedirect” = 0
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System “DisableRegedit” = 0
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System “DisableRegistryTools” = 0
1. Windows Defence Master may be lurked into user’s computer without any authorization or knowledge.
2. Windows Defence Master may keep scanning a targeted PC that it infects, and deceive user into paying money on its fake full version for money extortion.
3. Windows Defence Master may generate website traffic, regardless of browser you are using. This may have impact on Internet Explorer, Mozilla Firefox and Google Chrome.
4. Windows Defence Master may slow down the performance of computer via occupying large amounts of system resources.
5. Windows Defence Master may open a backdoor for attackers using found system vulnerabilities. This may lead to additional infection on compromised machine and allow hackers to access targeted PC freely.
Windows Defence Master is a typical Rogue security software program which is designed by cyber criminals to mess up affected computer and gain from victims. It can always sneak into a targeted machine with the aid of various social engineering tactics. Once being installed, Windows Defence Master infection will generally perform an auto scan for affected computer, stating that a mass of detected PC threats are required to be removed with its full licensed version. It can easily tell that the main purpose of Windows Defence Master is to mislead users into registering and purchasing for its alleged eliminated protection for those imaginary PC security threats. Apart from the basic symptoms, Windows Defence Master may slow down the performance of computer via taking up high system resource and keep CPU running at 100%. Provided users are not able to remove Windows Defence Master from computer timely, it may even open a backdoor for attackers to bring up additional danger for corrupted system. It is certain that Windows Defence Master should be terminated timely as long as being informed of its symptoms to safeguard PC as well as user’s privacy against potential threats. However, Windows Defence Master has the capability to protect itself by blocking standard antivirus software from running. In this case, you may consider the helpful manual removal to terminate Windows Defence Master entirely.
Please be aware that manual removal is a high-level process that is required for certain tech skills. If you cannot deal with the operation alone, it is recommended to ask help from the VilmaTech 24/7 Online Experts to resolve your problem completely.