Warn1now.com was definitely an unauthentic websites which provided lots of fake warnings for the innocent users. Deceptive cybercriminals used this fraud site intending to make more and more victims fall for the scam and gain ill-gotten money their own. Once this tricky rogue virus infected the targeted computer, users would receive appalling messages all the time, telling them that their computer has been infected with dangerous virus or malware, which needed to be solved at once. Then the Warn1now.com would provide the specified number as the so-called hot line, encouraging the innocent users to make a contact with the service. In this case, the deceptive service would ask the users for lots of money, promising them to deal with the infections but in fact there was nothing to be solved.
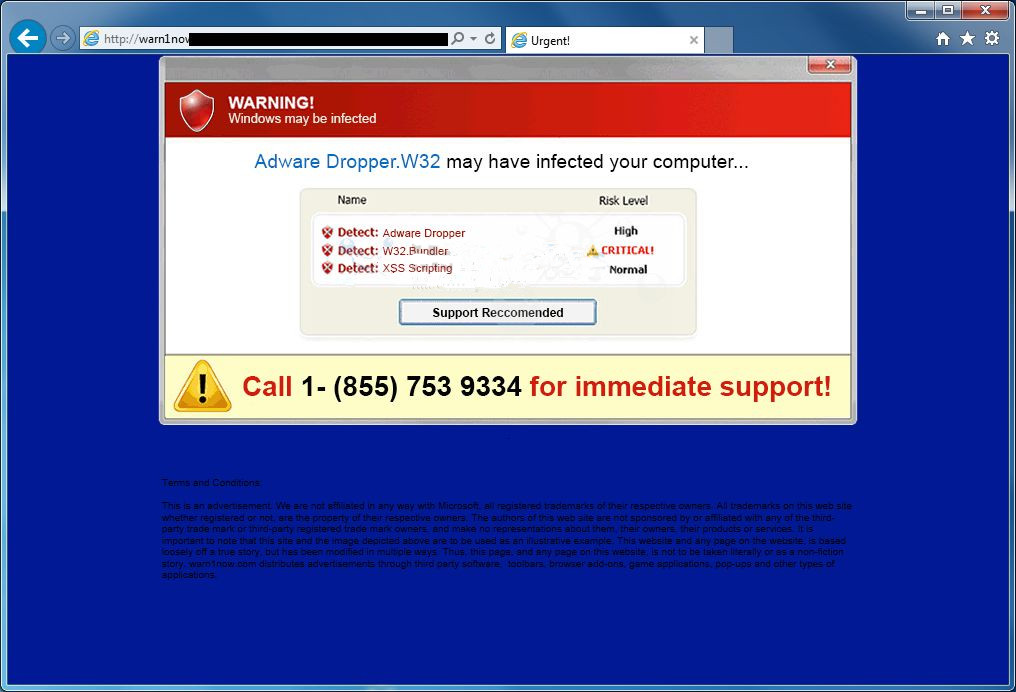
The hot line provided by Warn1now.com was actually connected to baleful cybercriminals, not just the call could charge the users a lot, the counterfeit solution for the fake infections would also cost the users much money. As most of the computer users were not so good at dealing with virus infection or protecting the security, so they would rather pay money then ask the others for help. In this case, the innocent users would easily trust the Warn1now.com warning and do whatever it said without knowing they were defrauded. And the hot line trick was not so simple, once the evil criminals successfully cheated the users for illegal payment, they would also get to know their private financial information naturally, such as their credit number, authentication codes or something likes that. In that way, user’s personal property would be in danger.
With the Warn1now.com remaining in the computer, there would be lots of potential safety hazards coming along. In order to display plenty of false warnings in the computer without resistant, the cunning Warn1now.com would have to modify the default system settings which would also lower the defense of the computer security. Under this circumstance, various unwanted virus and malware would love to seize the chance and invade into the system without user’s permission and awareness. In this case, the system would be infected without lots of malicious invaders and easily crashed or collapsed soon. Cybercriminals once captured the targeted computer, it would be easily for them to break into the system freely, making damages to the system and ruin all the critical files in it, the consequences would be disastrous for users. So, the best solution for users is to remove Warn1now.com as soon as possible and repair the computer before it is too late.
Please follow the instructions while doing the removal. If you encounter any trouble during the process, please click on the button then ask the VilmaTech Online Experts for more help.
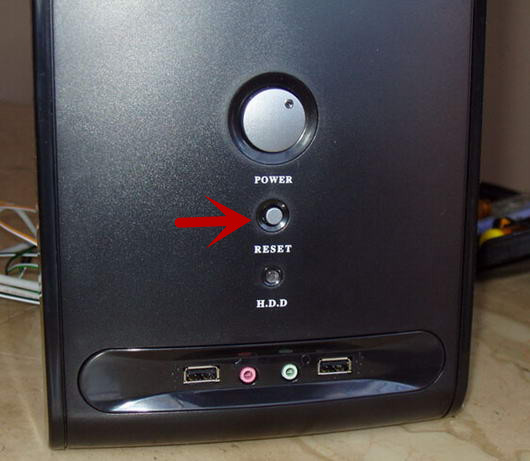
1) Press the Reset button on the computer case to restart the computer.
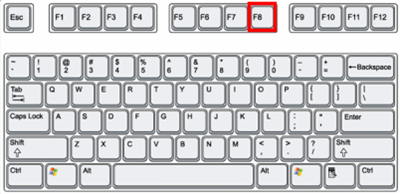
2) Constantly press the F8 key on the keyboard to enter the Windows Advanced Options, if it fails, just reboot the machine and try again.
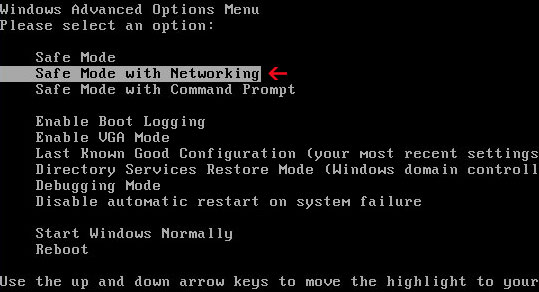
3) Select the Safe Mode with Networking with the arrow key then hit the Enter key.
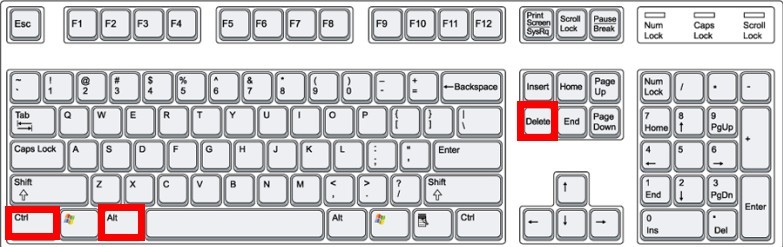
4) Open the System Task Manager by pressing Ctrl+Alt+Del keys concurrently.
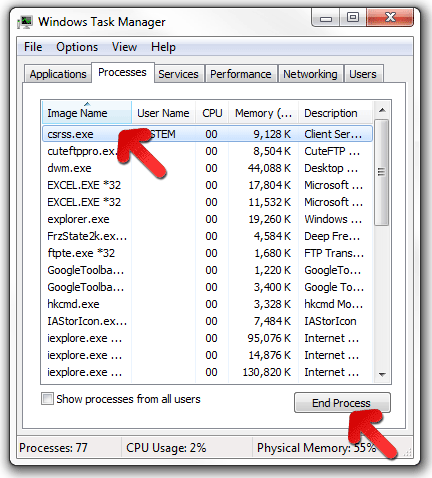
5) Search for the running processes of Warn1now.com in the Processes tab then disable them immediately.
6) Close the current window.
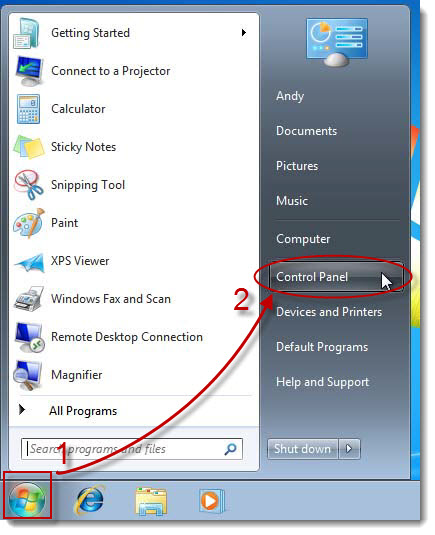
1) Click on the Start then open the Control Panel from the menu.
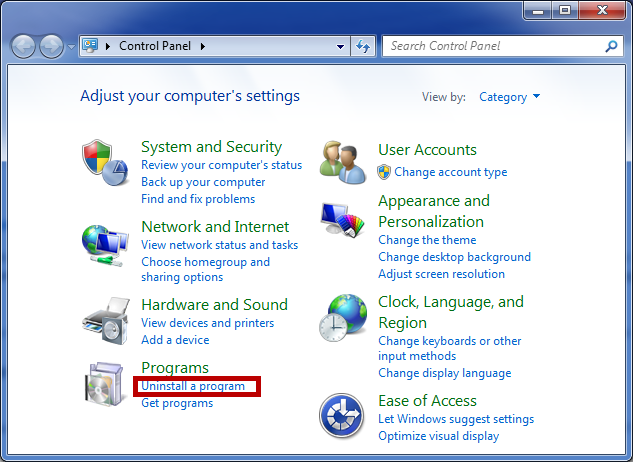
2) Click on the Uninstall a Program link in the pop-up window.
3) In the Programs and Feature, find out the related programs in the list then click on the Uninstall on the top column.
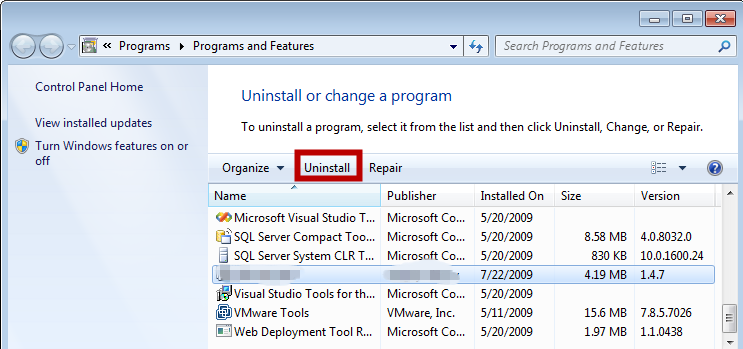
4) Approve the uninstall request then follow the wizard.
5) When finished the removal, refresh the programs list to check if all the unwanted programs has been removed.
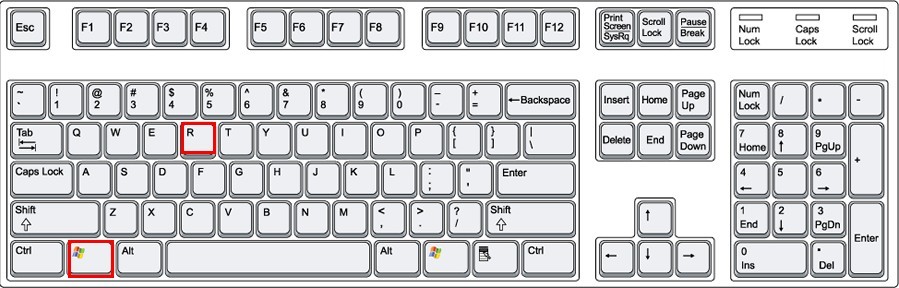
1) Press Windows+R keys at the same time to open the Run box.
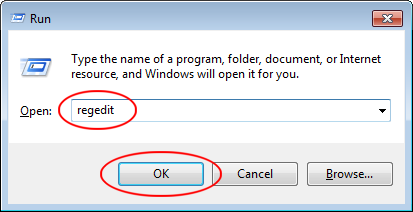
2) Input “regedit” in the search bar then click on OK button.
3) When the Registry Editor pop out, search for the related registry entries of Warn1now.com in the branches HKEY_LOCAL_MACHINE and HKEY_CURRENT_USER.
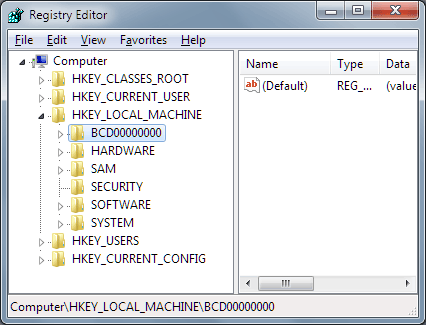
4) Clean the registry keys of the Warn1now.com.
5) Find out the files of Warn1now.com then remove them completely.
6) Restart the computer once finished the removal.
Warn1now.com was a classic fraud site with the main intention to coax the innocent users to call the deceptive hot line and charge for lots of money. Cybercriminals just take advantage of the opportunity to make profits from the users, making them concern about the computer security with fake alerts. Once encounter this kind of similar situation, users should run the installed antivirus or antimalware in the system to detect if there was any malicious virus or malware in the computer so that it could take remedial measures timely and correctly, instead of calling any unknown number or paying without scruples, otherwise, it is easily for users to fall for the trap set by evil criminals.
Moreover, users have to learn to prevent the computer from being infected with tricky malware. As cunning virus could always victimize the targeted computer without awareness, users have to stop it on the route of transmission. Most of the unwanted malware would often be bundled in freeware or shareware, once the users downloaded and installed them into the system, it would be disguised as some kind of necessary and useful applications for the system so that the users could trustingly approve their installation requests and let them have their way. Some times, virus would also hide in some corrupted websites, displaying tempting pop-ups to induce the users to click on them and be framed naturally. So, users have to build a good precaution consciousness to against with all the malicious infections effectively.
If you are interested in more methods to against with virus, you are welcome to click on the button then have a one-on-one chat with the VilmaTech Online Experts, they’ll be helpful.