New tricks have been played by cyber criminals to recapture trust from PC and Android users across the world. Ransomware now jumps from mechanical damages to browser damages simply due to the fact that more personal and financial activities can be and are finished online. Bigger fish can be located to pay off all the effort to make ransomware like trustpolice.biz virus.
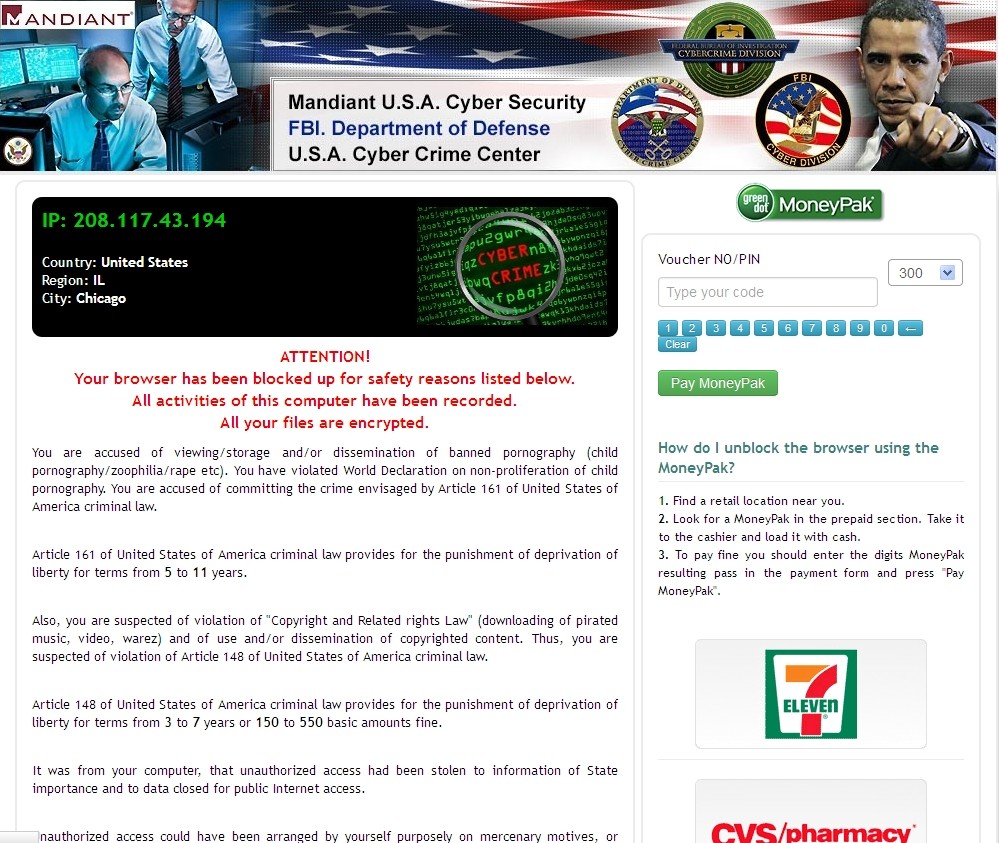
Trustpolice.biz is a newly released version of ransomware. As a matter of fact, U.S.A. Cyber Crime Center virus has been so far found to be the primary interface displayed by such version. Obviously, the virus is not the interface that is displayed. Trojan works inwardly to control the operation. Though the domain http:// trustpolice.biz looks not as formal as http://policeguardstate.org, the new form could confuse victims and make them into submitting $300 just in case trustpolice.biz is real. Global PC Support Center would like to reiterate hereby that trustpolice.biz is a virus that is made by cyber criminals for easy money, no enforcement agency will act so. VilmaTech Online Support recommends a complete reading of this article so as to get a general and clear picture of trustpolice.biz and the damages it arouses. The removal method can be reached at the end. Should there be anything you want to talk to technicians and get instant response, hit the live chat button to start off.
According to the current situation, it is believed that there are still a part of PC and Android users handing over money to cyber criminals since new version has been funded and realized. Based on the survey, people who finished the money submission only expect the return of significant documents stored on computer/ Android phone. It, again, indicates the importance to back up data regularly. Apart from the insecure online environment stemming from money submission, the information of the payment method will also be recorded. Fortunately, MoneyPak is pre-paid card that no big lost can be created.
Though trustpolice.biz virus doesn’t cause pivotal harms to system as what previous versions did, it should also make you concerned. Http:// trustpolice.biz is a vicious domain made by cyber criminals. With BHO technique, trustpolice.biz manages to load its vicious code into system’s startup section the moment web vulnerability is located by its sniffer. Due to its legitimacy, anti-virus programs will not pick it up as virus. As a consequence, victims get to believe that trustpolice.biz is genuine.
Right during the process, trustpolice.biz virus modifies DNS settings to load down additional codes from designated web sites to stop victims from leaving its counterfeit accusation message. That’s why victims can still operate a computer after quitting browsers by force but unable to surf the Internet thereafter. Be noted that the ultimate goal of trustpolice.biz virus is money. It is capable of making money even if victims do not hand over money by recording the log-in credentials stored in cookies. In other word, if one once finished finance transaction on a target machine, there’s a big chance that money lost would occur.
To regain a computer and the Android system that can surf the Internet and safeguard your online security, it is always recommended to remove trustpolice.biz virus upon its detection. To do so, some rectifications should be made deep in system configuration manually when anti-virus programs are not able to run the errand. Therefore, certain level of computer skills is required. Android users please get the help directly from VilmaTech experts. In the event of deficient skills, get experienced technician to help out at once.
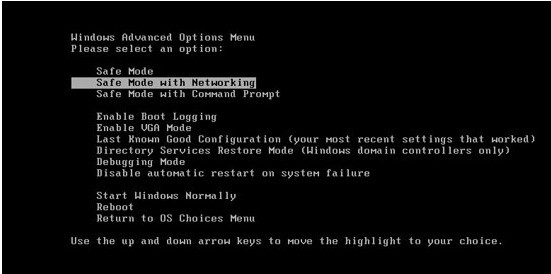
The below instruction is for Windows user. The removal guide for Macs is in the end since the guide is much simpler. To remove trustpolice.biz virus smoothly, it is recommended to carry out the instruction in Safe Mode with Networking where some vicious executable items will be exterminated. Be noted that no executable items should be launched during the removal.
A
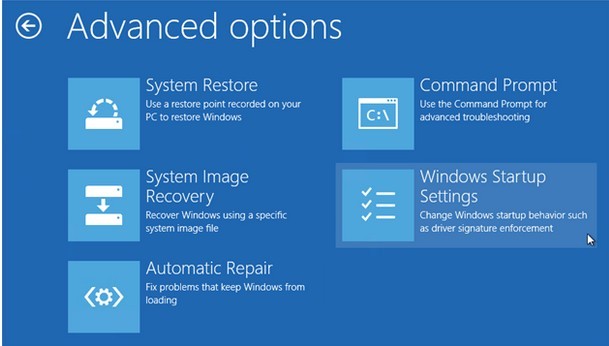
Get into Safe Mode with Networking to access desktop.
Windows 7/Vista/XP
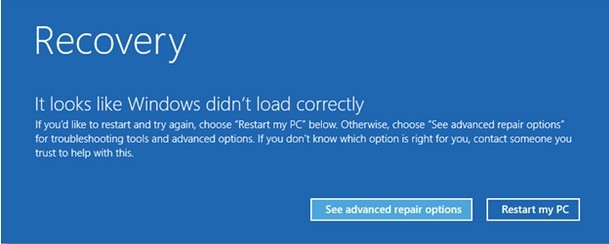
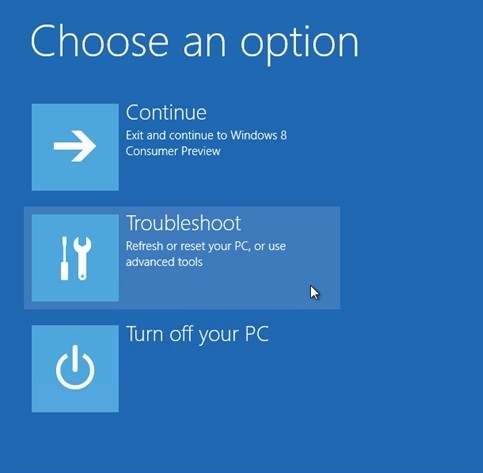
Windows 8
B
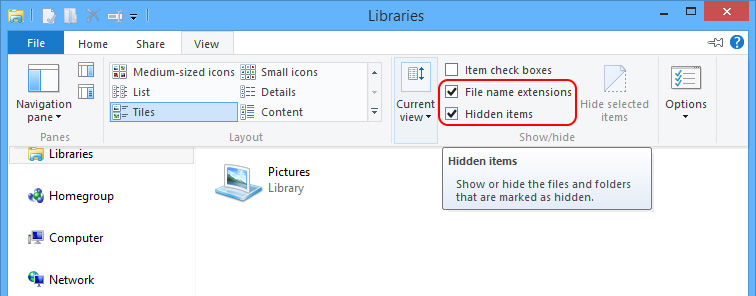
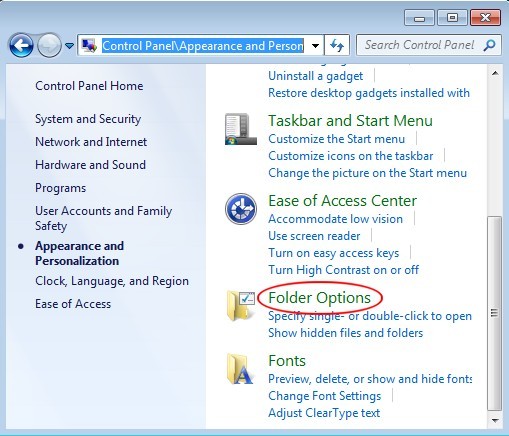
Show hidden items to remove trustpolice.biz virus and other possible vicious items from local disk.
Windows 8
Windows 7/XP/Vista
When done, navigate to C:\Windows, C:\Windows\System32\Roaming and C:\Windows\System32\Temp to remove items that are created on the date trustpolice.biz virus blocks down browsers; steps to arrange files by date:
Other files that need to be removed:
C:\Windows\system32\msconfig.com
C:\Windows\system32\regedit.com
C:\Windows\system32\dxdiag.com
C:\Windows\system32\rundll32.com
C
Some of trustpolice.biz virus’s components should be removed from Database.
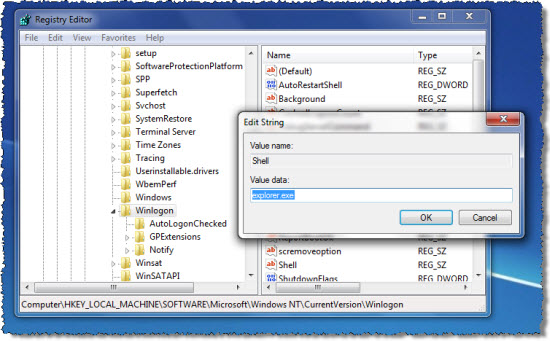
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\Current Version\Run\random.exe”
HKLM\SOFTWARE\Classes\AppID\esrv.EXE
HKLM\SOFTWARE\Classes\escort.escortIEPane
HKLM\SOFTWARE\Classes\AppID\escorTlbr.DLL
HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionRun
HKEY_CURRENT_USER\AppEvents\Schemes\Apps\Explorer\Navigating
D
Since trustpolice.biz virus mainly causes browser issue, it is necessary to rectify browser settings.
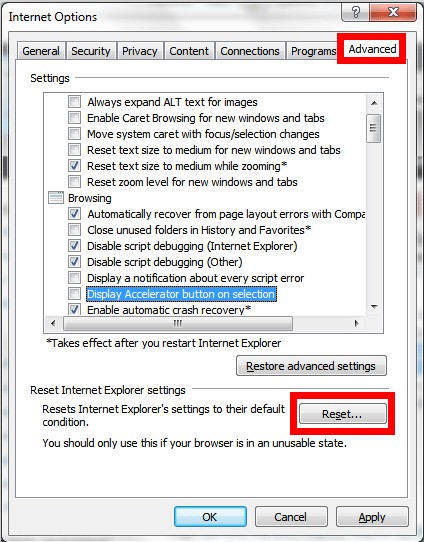
Internet Explorer
Click on the Tools menu and then select Internet Options to press Restore Defaults button under Advanced tab.
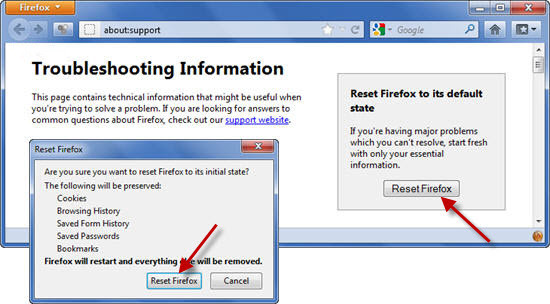
Mozilla Firefox
Click on the Firefox button to select Troubleshooting information from Help options and press ‘Reset Firefox’ button.
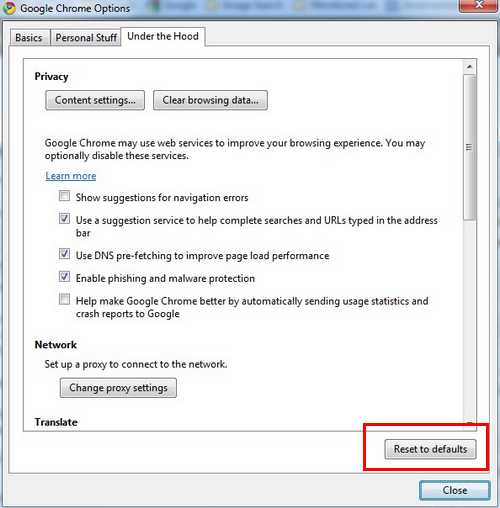
Google Chrome
Click ‘Customize and Control Google Chrome’ menu to select ‘Options’; press ‘Reset to Defaults’ button under ‘Under the Hood’ tab.
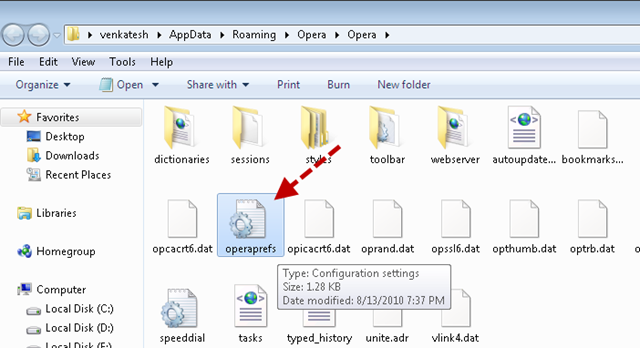
Opera
Show hidden files and folders to remove Operapref.ini file under “C:\Users\user_name\AppData\Roaming\Opera\Opera\”.
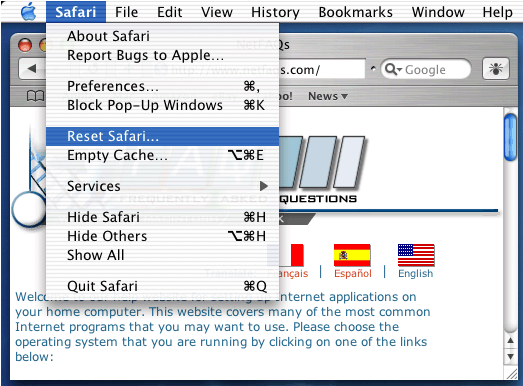
For Mac users, the only thing one should do is to reset Safari since nothing has been further developed to affect Mac destructively.

Attention:
More steps might have to be undertaken after trustpolice.biz virus is taken down with the above given instruction as web vulnerability can be easily exploited by various infections. Optimization is recommended to be carried out for sluggish PC performance afterward. Though trustpolice.biz virus locks down browser only, the problem doesn’t confine to browser, additional remedy should be made to system configuration. Considering the possibility to introduce in additional infections, VilmaTech Online Support would like to remind you of other vicious items that are not necessarily related to trustpolice.biz virus directly so that complete removal can be achieved without doubt. Stick to the manual instruction and help yourself. Android users please get help from experts here. On the occurrence of unexpected issues, exclusive help will be offered by Global PC Support Center to solve your concrete situation accordingly.