The above listed three variants are the most notorious ones to interfere with users’ experience. Usually, getting one of the three items will end up with the other two and people would suffer from more unpleasant scenarios:
With all the unpleasant scenes and its sticky feature, most people would consider it as a virus. However, the fact is just on the contrary. Trojan.Win32.Bromngr is not technically a virus. Actually, it has different names according to different anti-virus programs such as Adware.Win32.Bromngr, Not-a-virus:Adware.Win32.Bromngr. It is obvious an adware but with malicious traits (which can be achieved with some slight modifications):
According to Global PC Support Center, any sticky program (especially the one like Trojan.Win32.Bromngr) imposes potential dangers as the default configuration is designed to ward off basic threats. As a matter of fact, Trojan.Win32.Bromngr’s affection could give fat chance for vicious infiltration.
First of all, there are thousands of such adware alive on the Internet, and it is quite easy to build Trojan.Win32.Bromngr with BHO and JS technique; to get money out of the item as soon as possible, the adware doesn’t deserve fine work and bug thus is unveiled to infections embedded on the Internet.
Second, to make itself popular rapidly and to gain wide coverage, Trojan.Win32.Bromngr would bundle with other programs; in other word, additional items will be loaded onto the target machine, the limited space will be then taken up a lot to leave little CPU for full play, which would compromise the machine and make it much more susceptible to infections.
The last but not least, once Trojan.Win32.Bromngr is captured by virus, BHO technique will preload the vicious codes into DataBase without being examined strictly and JS technique will be utilized to record any in-put information, which could finally result in identity theft and money loss. Therefore, it is highly recommended to hurry up in removing Trojan.Win32.Bromngr. Below is the removal thread offered by VilmaTech Online Support. On the occurrence of confusion or difficulties, please start a live chat for exclusive help according to your concrete situation.
A
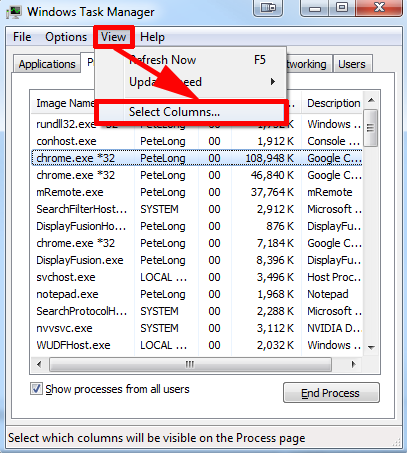
Access Task Manager to remove/end the items with the path directing to Trojan.Win32.Bromngr’s according to the report by the installed anti-virus program.
(tip: it is recommended to combined with the path name shown in Running Tasks – start menu (start screen for Windows8 users > All Programs (All Apps for Windows8 users) > Accessories > System Tools > System Information > Software Environment)
B
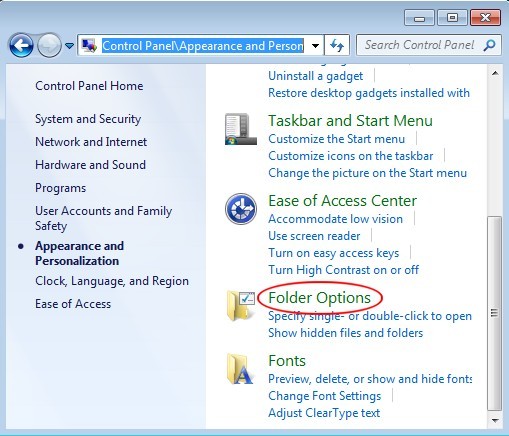
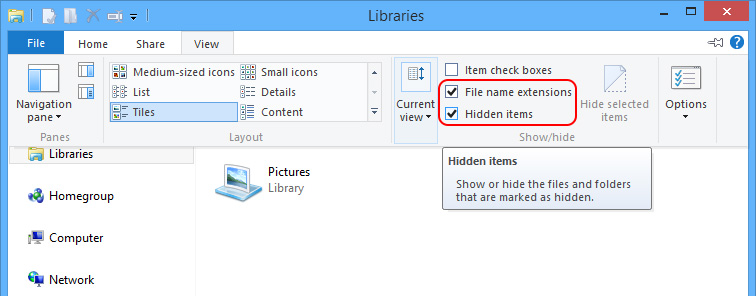
Show hidden files and folders to remove the items created by Trojan.Win32.Bromngr as well as the generated Temp items.
Windows 7/XP/Vista
Windows 8
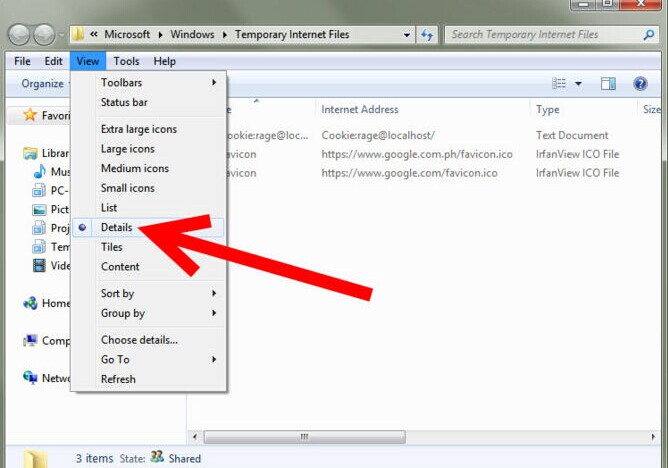
1. navigate to the following folders to remove the items generated on the day when Trojan.Win32.Bromngr was firstly detected:
%SystemDriver%\( the system division is “C:\” by default)
C:\Windows
C:\Windows\System32
C:\Users\[your username]\Documents\
C:\users\user\appdata\local\
C:\Program Files\(tip: to filter out the items generated on the day when Trojan.Win32.Bromngr appeared, please right click on the space of a window that is under inspection to select “Arrange by”; then select “day” in the drop-down list)
2. remove temp files generated by Trojan.Win32.Bromngr.
C
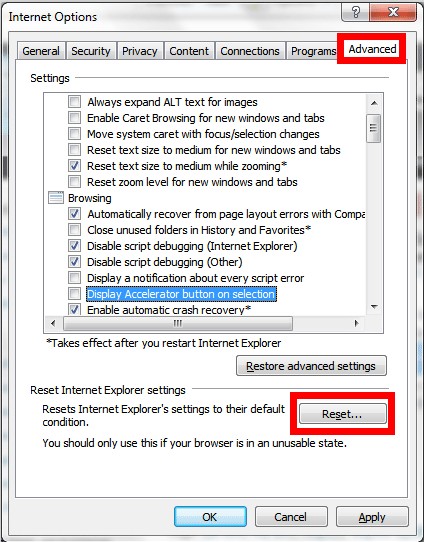
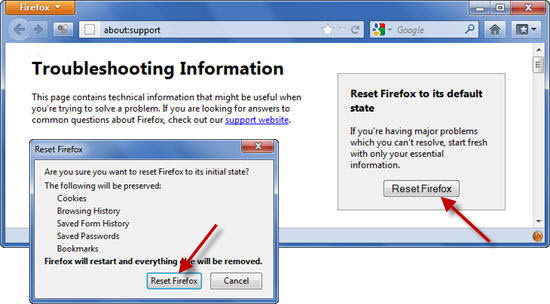
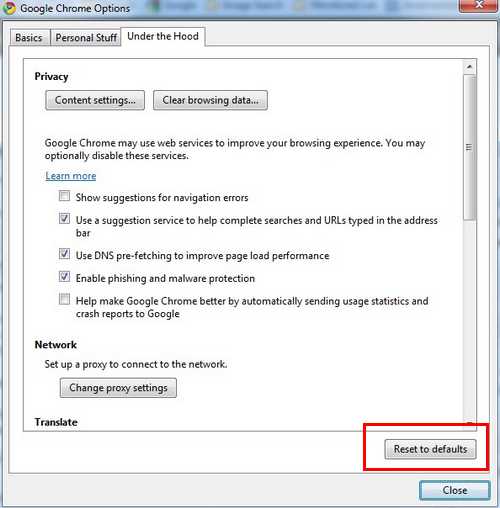
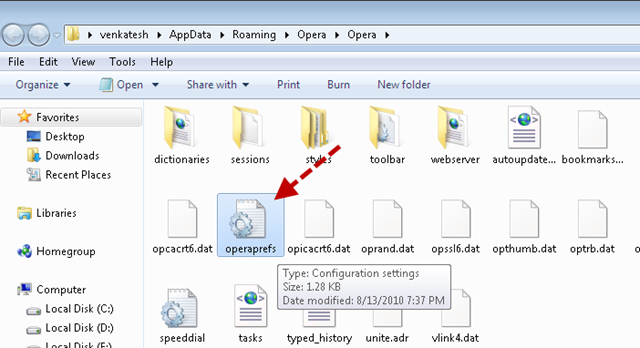
Reset browsers to clear up the items created by Trojan.Win32.Bromngr on browser settings.
IE
Firefox
Chrome
Opera
As a web application, what Trojan.Win32.Bromngr aims at is money. By hijacking a browser, Trojan.Win32.Bromngr manages to generate and augment the amount of traffic within short period of time. With the huge traffic, the Bromngr adware is capable of attract as many businesses as possible:
People should know that it is vicious attribute code that on which anti-virus programs rely to deal with detected items. Without the attribute code, anti-virus programs are not going to remove anything. As what has been made clear by VilmaTech Online Support that Trojan.Win32.Bromngr is an adware possessing some vicious traits by modifying some techniques. Therefore, manual method is recommended to remove Trojan.Win32.Bromngr completely. Also certain level of computer skills should be employed as the directory and the name and the number of dropped-down items can vary from system to system. Any help request will be gladly answered if one starts a live chat window here.
Defrag is recommended to be executed in the end of the removal to optimize PC performance. It is hard to foresee what Trojan.Win32.Bromngr might brings onto a target machine; besides, during the period of Trojan.Win32.Bromngr’s harassment, odds and ends are scattered around in the local disk to result in unreasonably utilized resource. In this case, defrag is recommended. here’s the video to show how.