Ndo.coreopti.net was a harmful domain distributing nonstop pop-ups to the Internet users, showing them various download and update notifications in order to victimize them imperceptibly. Ndo.coreopti.net pretended to be a special platform for providing users all the latest update or download of those common software so as to gain trustworthy from the Internet users. Actually, Ndo.coreopti.net was an unsolicited program which got installed into the computer without users’ permission. As long as the cunning Ndo.coreopti.net invaded into the targeted computer, it would start to release tons of pop-ups to bug the users, coaxing them to click on those download button so it could seize the chance to introduce plenty of unwanted programs even malware into the system without restraint. With more and more Ndo.coreopti.net related programs constantly installed into the system, users might suddenly find the computer perform weird and the system become out of order from time to time. However, users could never realize it was the tricky Ndo.coreopti.net doing harm to the computer.
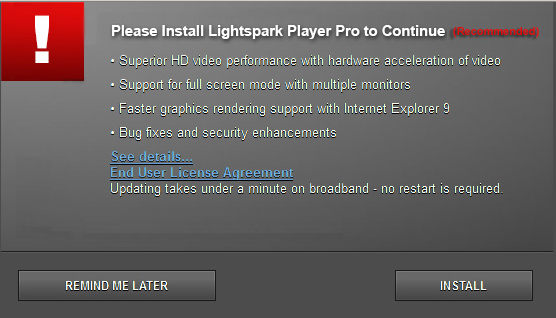
Adding various unwanted programs into the targeted computer was the ultimate purpose of the Ndo.coreopti.net. In order to seek for exorbitant profits from the innocent users, Ndo.coreopti.net introduced a mass of malware like adware, browser hijacker or spyware into the infected computer, combining together to victimize the innocent users in improper means. As the innocent victims clicked on those download buttons provided by Ndo.coreopti.net, they never knew what they have agreed with. Since then, users could encounter a variety of pop-up ads and links in the computer, concerning unknown downloads or online shopping recommendations which might seem so useful and tempting. Actually, all the favorable pop-ups were released by those malware installed in the computer, most of the content and information were deceptive. Once the users could not resist the special offers from Ndo.coreopti.net and those related malware, blindly clicking on those links or buttons and being transferred to unknown websites, the consequences would be disastrous. Those malicious fraud sites would cause the innocent users enormous losses and damages, so the vicious Ndo.coreopti.net could make profits in this way.
Ndo.coreopti.net might cooperate with baleful cybercriminals, with the main intention to make further profits from the innocent users. Since the Ndo.coreopti.net successfully got installed into the computer and easily brought in those malicious invaders, cybercriminals would take advantage of the Ndo.coreopti.net to collect users’ personal but valuable information illegally. Under this circumstance, Ndo.coreopti.net could record users’ online activities, confidential data and web content stealthily, such as users’ login password, search query, preference, online banking details, etc. As long as the Ndo.coreopti.net revealed all the information to the evil cybercriminals, users’ personal property and privacy would be under serious threats. Moreover, because Ndo.coreopti.net and all the unwanted malware were running in the system background without scruples, the computer protection would be corrupted thoroughly and the system performance was decelerated gradually. Because the system resources were occupied by all the invaders maliciously, the computer would easily break down in any minute. In order to rescue the infected computer in a timely manner and avoid irreparable losses and damages caused by Ndo.coreopti.net and criminals, users should remove Ndo.coreopti.net as soon as possible.
Please feel free to click on the button to make a contact with the VilmaTech Online Experts during the process, they would be glad to help.
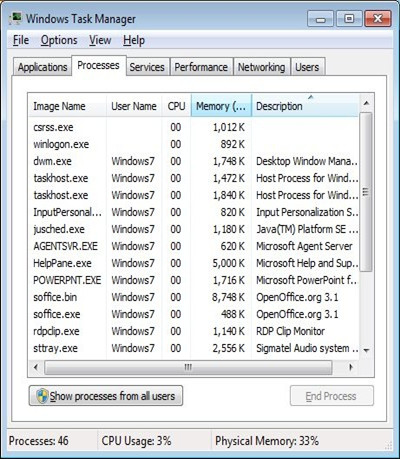
1. Stop Ndo.coreopti.net pop-ups running in the system background.
Use the key combination(Ctrl+Alt+Del) to open the System Task Manager, click on Processes tab to find out all the running processes of Ndo.coreopti.net pop-ups from the processes list, select them and click on End Process button to disable them without hesitation.
2. Remove Ndo.coreopti.net related programs from the computer.
Press the Windows key to open the Start menu, click on Control Panel. Find and click on Uninstall a Program link to go to the Programs and Features list, select the Ndo.coreopti.net programs from the list then click on Uninstall button to remove them one by one.
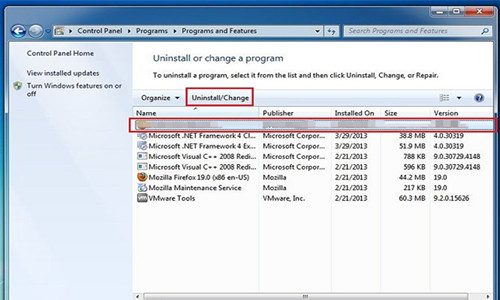
3. Refresh the programs list after the Ndo.coreopti.net removal, make sure all the unwanted programs have been removed.
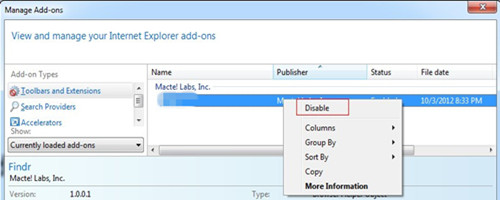
1. Open the Browser to remove Ndo.coreopti.net related extensions from the browser.
Click on Tools-> click on Manage Add-ons-> right-click on Ndo.coreopti.net related items from the Toolbars and Extensions list-> select Disable option.
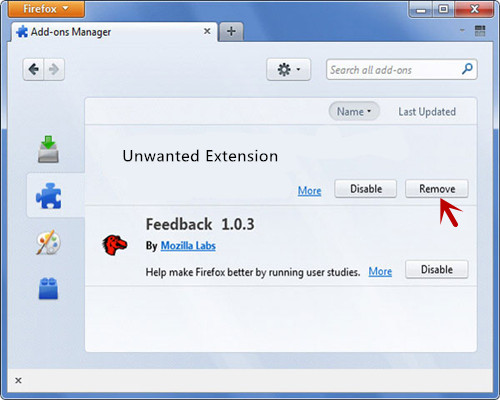
Click on Firefox button-> click on Add-ons-> search for all the extensions of Ndo.coreopti.net from the list-> click on the Remove button on each line.
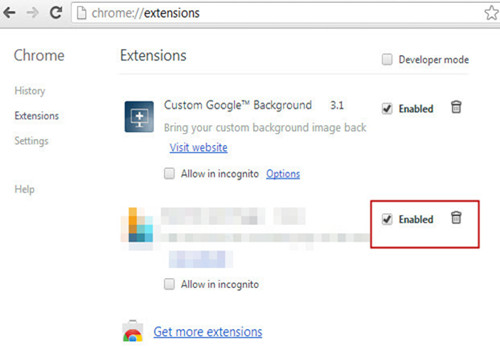
Click on wrench icon-> locate Tools-> click on Extensions-> click on the bin icon or uncheck the items related to Ndo.coreopti.net.
2. Restart the browser to let the removal take effect.
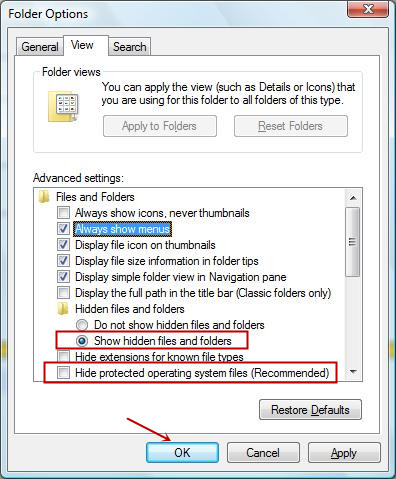
1. Modify the folder properties settings before removing the files of Ndo.coreopti.net.
Click on Start-> click on Control Panel-> click on Appearance and Features-> click on Folder Options-> click on View tab-> select Show hidden files and folders-> remove the check mark from the Hide protected operating system files(Recommended)-> click on OK button.
2. Search for all the remaining files and folders of Ndo.coreopti.net in the computer then remove them completely.
3. Restart the computer once finished the Ndo.coreopti.net pop-ups removal.
Even the Ndo.coreopti.net was not a high-risk infection for the computer, it is still necessary to be prepared to prevent it effectively. Because this kind of malware could lead to irreparable consequences for users. In order to avoid being victimized by virus and malware in the future, all the computer users should learn more useful methods to against with them. As most of the cunning malware are coming from unknown downloads or bundled third-party software updates, users should always stay vigilant while downloading software into the computer. The best way is to go to visit those official websites and get the needful download, and always detect the new downloads before using them. Furthermore, in the installation process, users should always pay attention on those terms just in case to let those malware have their way, mixing in those installation items and getting into the computer easily. If you want to find out a better way to prevent virus infections, please click on the button to have a chat with the VilmaTech Online Experts and get more help there.
*Easy Steps to create a restore point on your own.