Mywebsearch.com is a browser hijacker that can be traced back to 2010. It was firstly found to appear to be default homepage all of a sudden and default search engine. With connivance given by wide range of PC users due to several removing steps were sufficient to take it down, more of mywebsearch variants are coming into being, such as home.mywebsearch.com, mywebsearch toolbar, and PUP.MyWebSearch, to complex infiltration in an attempt to help mywebsearch virus survive longer on a computer for the goal of obtaining money as more traffic being intercepted will bring about more co-operations with operators/promoters.
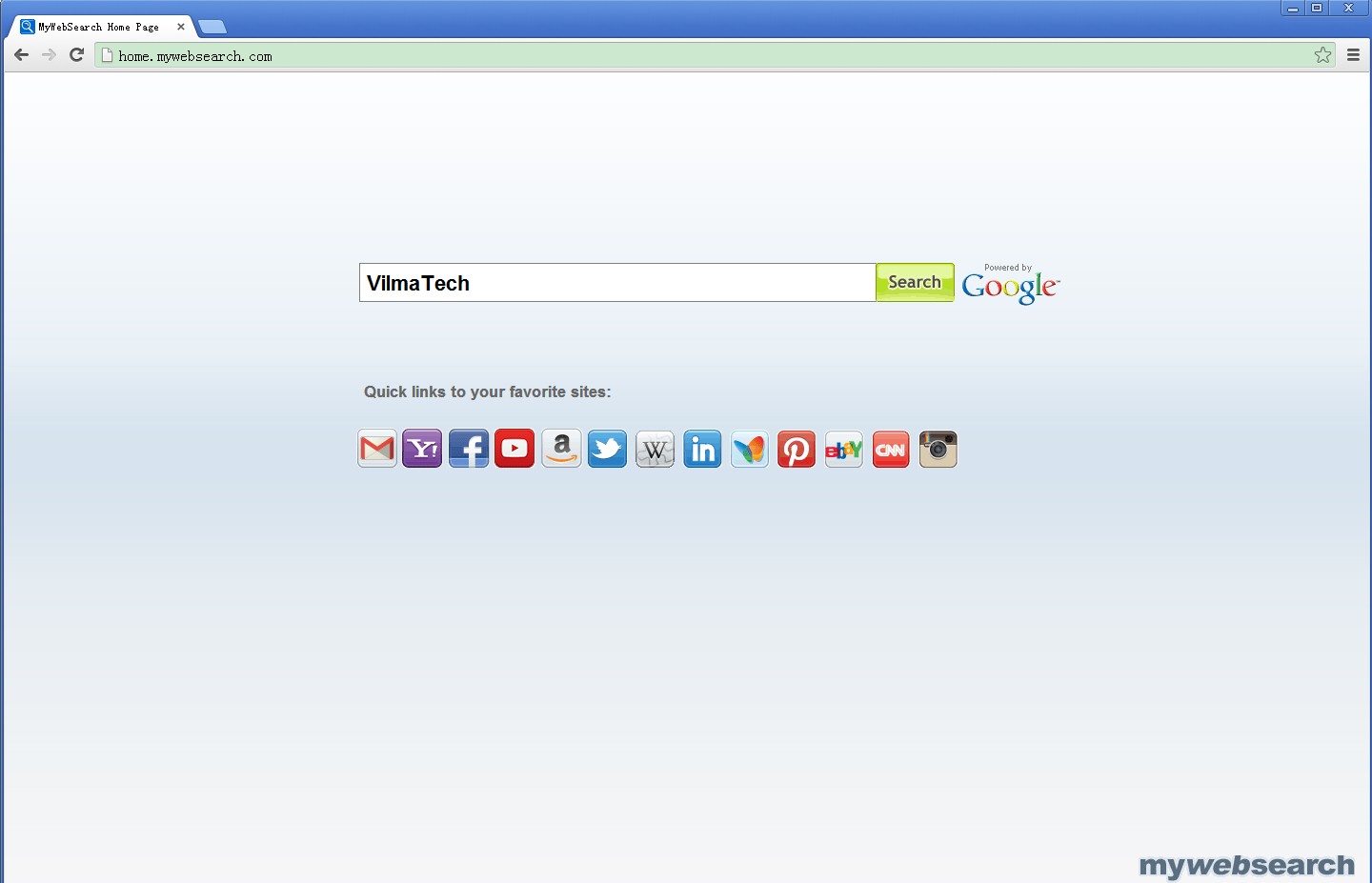
There’s interaction effect among mywebsearch.com and its detected variants. Any one of them emerges on a target machine, others may very well be introduced on the same machine. That’s the reason why some victims who got infected by mywebsearch.com finally got infected with mywebsearch toolbar and who got infected by PUP.MyWebSearch finally got infected with mywebsearch.com. Therefore, it is wise to remove mywebsearch.com virus as soon as possible. Provided that more incidental issues happen to cause failure in removing mywebsearch.com virus, you are welcome to get instant help from professionals with rich experience working for VilmaTech Online Support.
Mywebsearch.com virus does not seemingly impose damages on a target machine except irritating surfing experience. However, one may finally detect lagging PC performance as well as stuck browsers (e.g. Safari, Firefox, Chrome, IE and Opera). The problems are simply caused by increasing junks loaded down through backdoor formed by mywebsearch.com virus, which consumes considerable computer resource.
Be noted that sticky programs including mywebsearch.com virus indicate random modifications deep in computer’s kernel part. In general, build-in antivirus programs are capable of picking up any vicious items unless Rootkit is involved or related system configurations are modified to be the carriers of virus. With loose secure defense, more infections stand a chance to easily affect a computer.
It should also come to your awareness that backdoor is now the major way utilized by various types of infections for infiltration. But to mywebsearch.com virus only, the backdoor also serve to transfer collected information to designated remote server. The writer backstage can thus generate extra money by reselling the collected information that can be personal data, pictures, online whereabouts. Those information can either be spammed or used to help spammers locate mostly visited sites, making ready to obtain more money by affecting more PC users at a time after they successfully attack those sites.
Mywebsearch.com virus has been on the list of making PC users suffered for several years. With improved techniques, the virus manages to survive removal guide offered by online computer experts constantly. Below is the latest instruction to help remove improved mywebsearch.com virus. Considering the possibility that additional infections/ junks might be introduced in to bring about an aborted removal, VilmaTech online experts are always staying online to offer on-demand help.
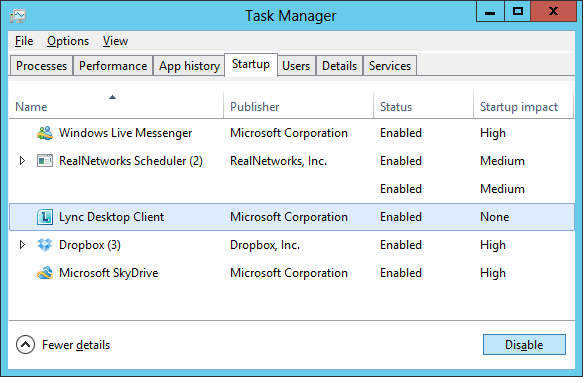
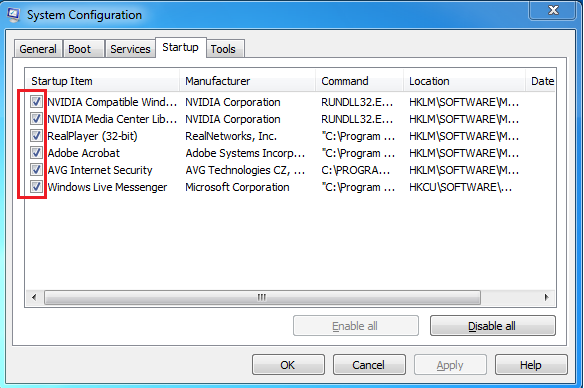
Step one – remove items associated with mywebsearch.com virus from build-in Startup functionality.
Windows 8
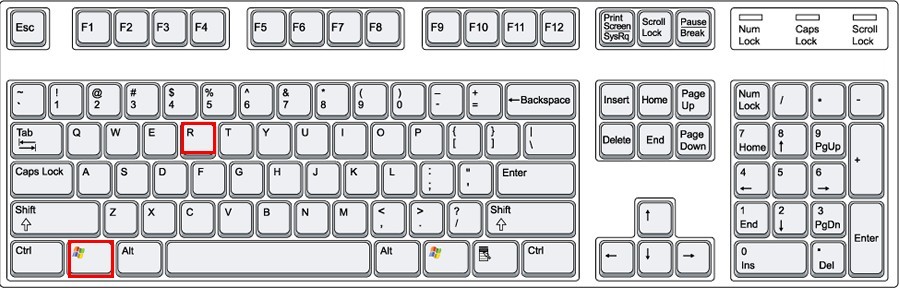
Windows 7/Vista/XP
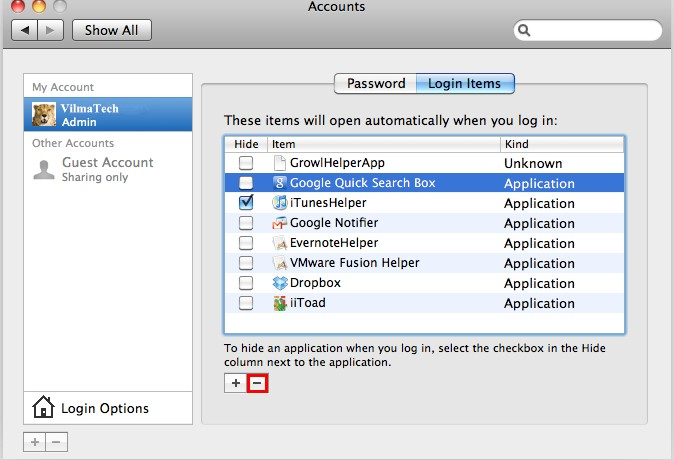
Mac
Step two – Modify browser settings to remove mywebsearch.com virus from IE, Mozilla Firefox, Google Chrome, Opera and Safari respectively.
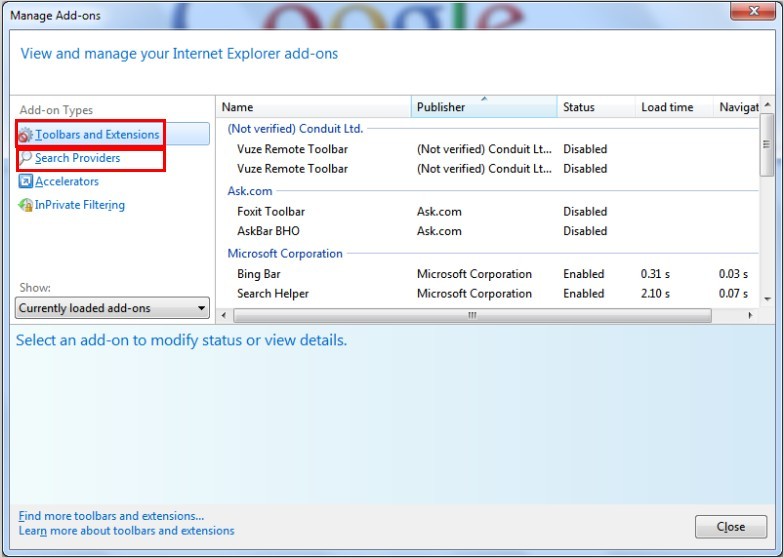
Internet Explorer
a. Remove any indication of mywebsearch.com virus from ‘Manage Add-on’ window under Search’ section.
b. Remove mywebsearch.com virus from ‘Toolbars and Extensions’.
c. Remove mywebsearch.com virus from ‘Search Providers.
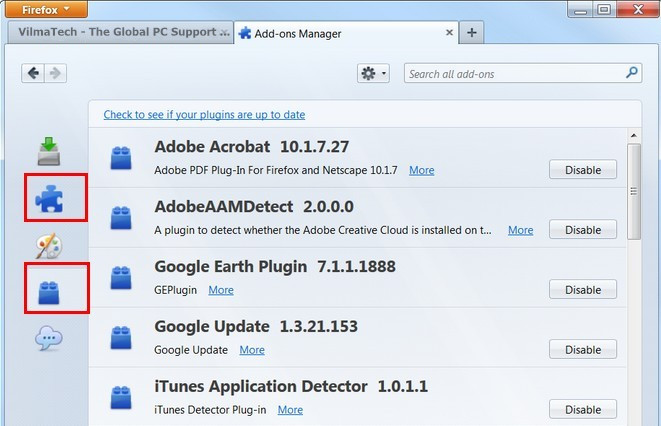
Mozilla Firefox
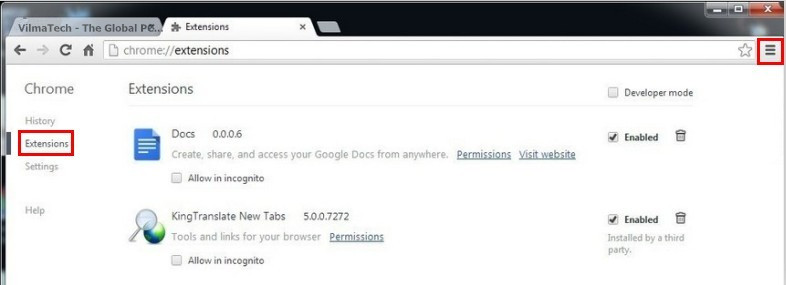
Google Chrome
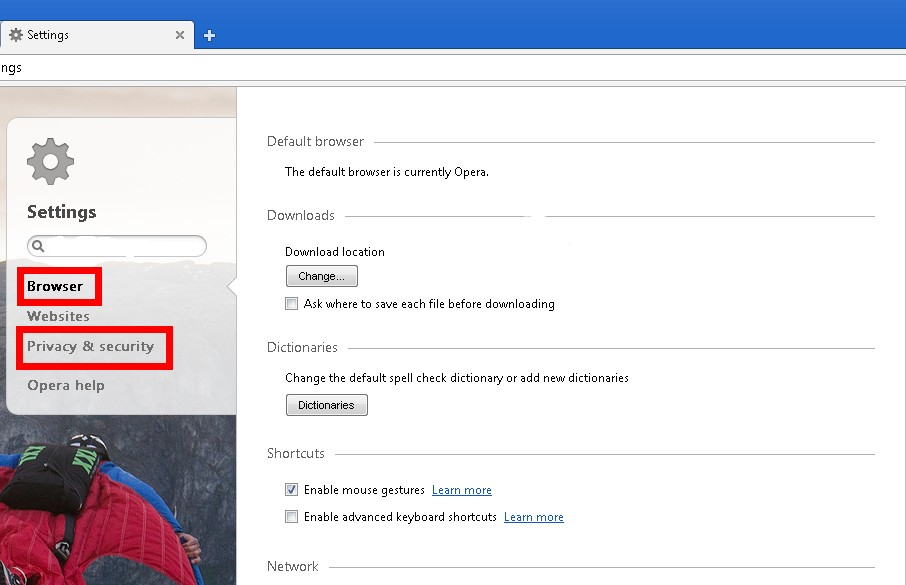
Opera
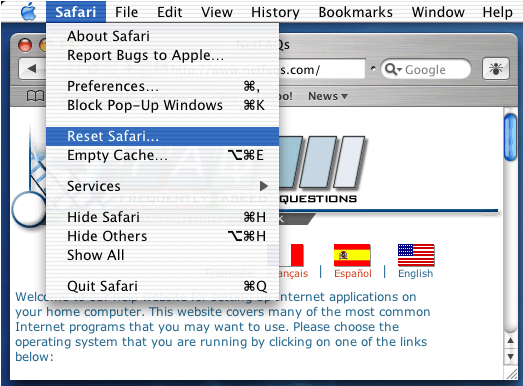
Safari
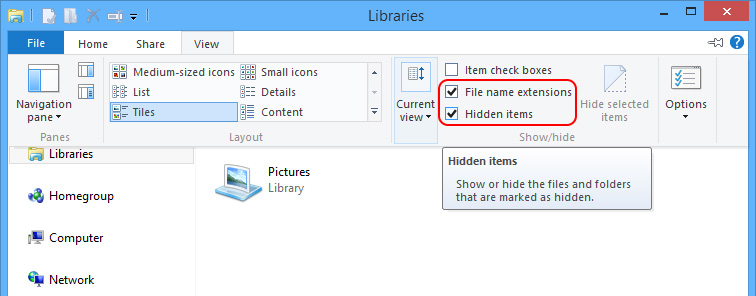
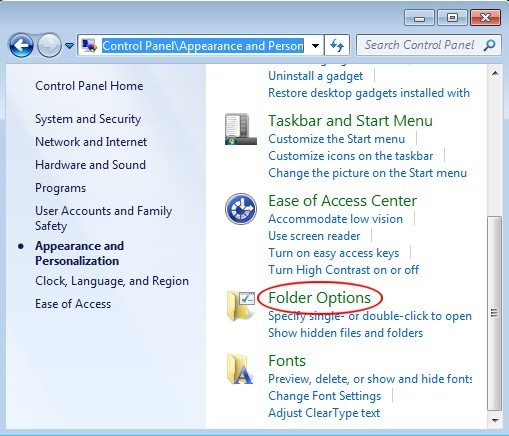
Step three – Show hidden files and folders to remove all suspicious files under C: Windows and System32 to thoroughly remove mywebsearch.com virus.
Windows 8
Windows 7/XP/Vista
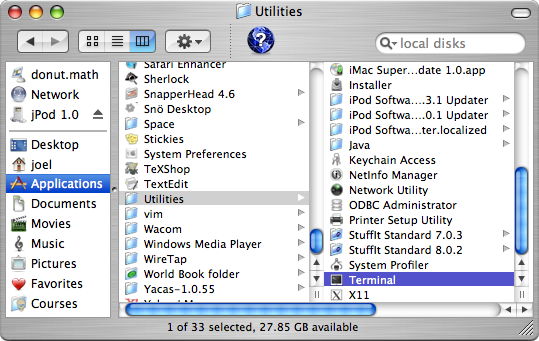
Mac
“defaults write com.apple.Finder AppleShowAllFiles YES”
“defaults write com.apple.Finder AppleShowAllFiles NO”
Conclusion:
Mywebsearch.com virus is more than an infection to give rise to browser issues. By adopting Rootkit technique, mywebsearch.com virus manages to modify Database to thereby form backdoor without disturbance. As a consequence, more potential infection can be found subsequently to prevent easy removal. Be noted that mywebsearch.com virus keeps mutating and improving. Therefore, one should remove mywebsearch.com virus as soon as possible before its spammer adds in advanced technique to overwhelm available removal guides. Be careful when removing mywebsearch.com virus with the above offered instruction as any slight discrepancy would bring about failure and might cause tangled computer issues. On the occurrence of confusion, contact VilmaTech Online Support is recommended.