Jxf.mappingzone.net, which is a category of pop-up malware, plays a crucial role in the cyber malware. Jxf.mappingzone.net pop-up malware displays similar search engine interface, and done by this way Jxf.mappingzone.net aims at luring online users into being tricked. Cybercriminal gangs have revealed a lot of such Jxf.mappingzone.net browser hijacker, always effort to spot and exploit vulnerabilities then they can be used in cyber attacks. The Jxf.mappingzone.net pop-up malware will not be limited to any kind of Internet browsers – It is able to compromise Internet Explorer, Google Chrome, Mozilla Firefox and more in all versions of Windows Operating System. Even include the Mac OS. Jxf.mappingzone.net is interesting in reducing the security of any software that’s used to run the web, as doing so can it infiltrate on increasingly Internet users’ computers for abundant benefit-making. For the essential purpose, the Jxf.mappingzone.net pop-up malware is used to acquire money and steal confidential information from the victimized systems. You may refer to the screenshot of the Jxf.mappingzone.net as following.
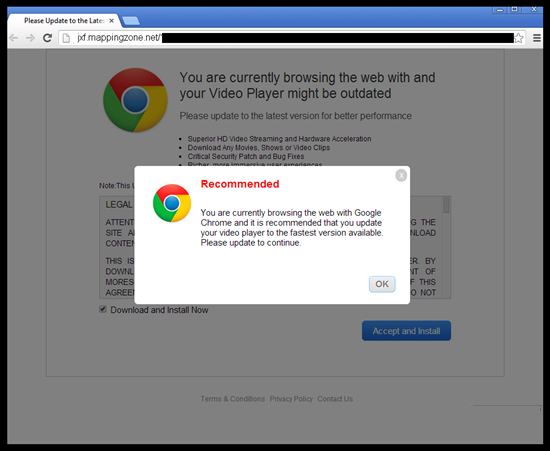
Jxf.mappingzone.net also refers to the so-called browser hijacker, one of the most perilous cyber attacks, just alike the previously released Websearch.flyandsearch.info malware. The Jxf.mappingzone.net pop-up malware always attempts to get Internet users been trapped by some proficient online fraud tactics – efforts to make potentially harmful content accessible through those third-party Windows programs including freeware, shareware, web plugin and more. In most cases, Jxf.mappingzone.net site offers pop-up indicated users should update their video player to the latest version available. Persuade targeted users to download programs. This can be believed by most of doubtless Internet users that this is a normal update. Once those Internet users downloaded the program recommended on the Jxf.mappingzone.net pop-up, their computers will be dropped down with virus payloads simultaneously. Jxf.mappingzone.net then can take over the infectious Internet browsers and even completely govern the infectious system for malicious activities. Jxf.mappingzone.net virus then allows attackers accessing to the victimized machine and steal all sensitive information stored on web browsers and hard drives.
It is highly recommended of you removing the Jxf.mappingzone.net pop-up malware as quick as possible. Otherwise, you have to face incredible damage including system damage and confidential information exposure. If need professional help to remove the Jxf.mappingzone.net virus, you can Live Chat with VilmaTech 24/7 Online Experts now.
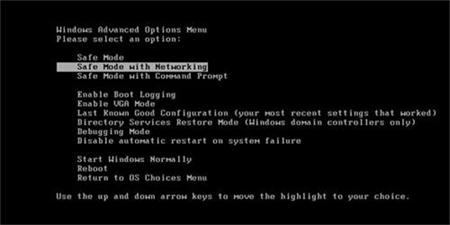
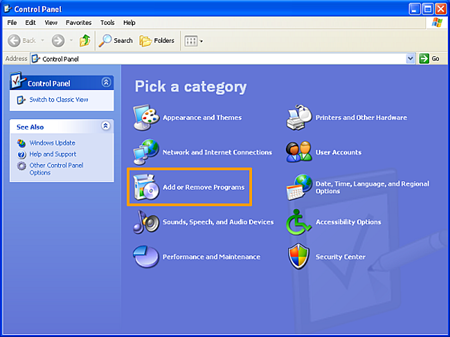
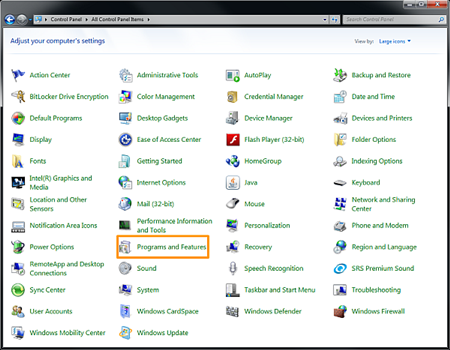
A: For Windows 7, Windows Vista
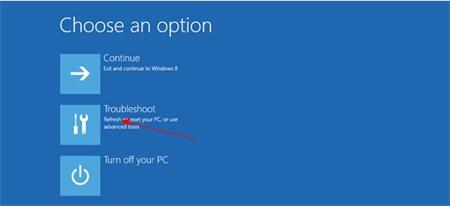
B: For Windows 8

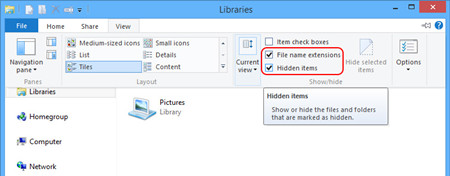
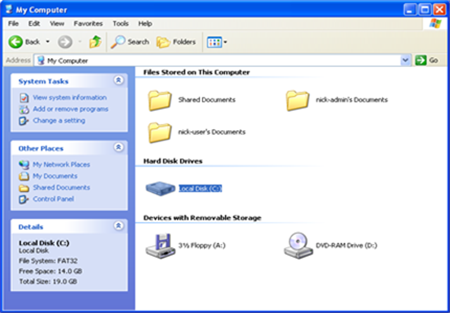
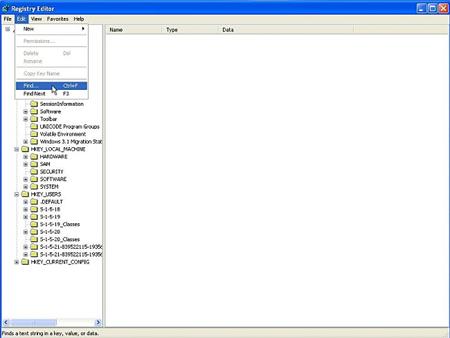
Manual way to remove the Jxf.mappingzone.net malware completely requires the virus leftovers removal. After the steps mentioned above, you still need to remove all left files about the Jxf.mappingzone.net browser hijacker. To accomplish this step, you have to show hidden files first, follow the below tips please.
A: Windows 7, Windows Vista,

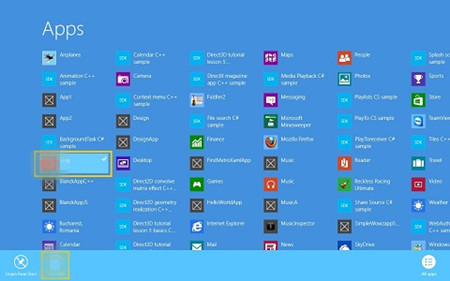
B: For Windows 8, Locate at the Metro.
C: Delete shown files about the Jxf.mappingzone.net pop-up malware.
The attackers behind the Jxf.mappingzone.net malware can target distribution network and allows them to infect victim in selected countries through multiple channels. Once Internet users become infectious, the Jxf.mappingzone.net malware can tamper with all default Internet settings, for instance, homepage, search engine, startups, new tab and more must be altered with the Jxf.mappingzone.net malicious one. Jxf.mappingzone.net pop-up malware is designed to intercept online banking transactions and steal those victimized users’ credentials including log-in credentials, online transaction data, banking data, and other financial details. The cybercriminals behind it appears to be more evil. They can take advantage of victimized users’ confidential information to participate in illegal online commercial activities. Therefore, never belittle the Jxf.mappingzone.net malware, the best way to reduce damage is to get it rid of the victimized system. Till now, if you still need more help to remove the Jxf.mappingzone.net malware, you can live chat with VilmaTech 24/7 Online Experts.