IsDownload.net was considered as an unsolicited web service showing in the targeted computer abruptly, coming with the name of IsDownload in order to make the computer users believe the IsDownload.net was dedicated to provided software download services, so it could gain more trusts from the users and avoid being removed from the system. Because the IsDownload.net installed in the targeted computer by using improper means, in most cases, the users could not notice the infection in the first place and mistakenly considered IsDownload.net was coming with the current search engine. For this case, IsDownload.net would get the chance to carry on its evil deeds in the infected system. Since the unwanted IsDownload.net successfully got installed in the computer, it would suddenly get the right to display tons of unknown software download prompts to the users, getting their attention with the nonstop pop-ups showing in the browser and intending to lure them to permit the download requests unwittingly.
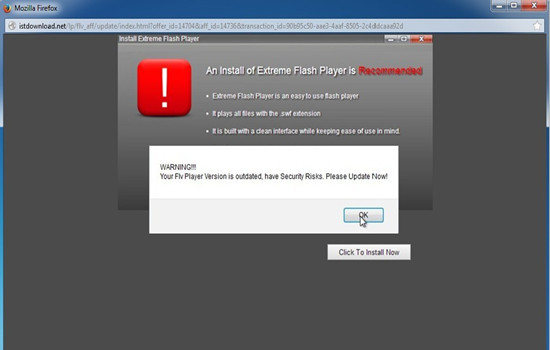
Generally, once seeing software download or update notifications, most of the computer users would choose to approve the requests without thinking through. Just for this reason, the cunning IsDownload.net would take advantage of this occasion to set the innocent users up so as to achieve its evil purposes. Most of the downloads requests released by IsDownload.net were actually traps for the innocent users. Under the cover of the software downloads, IsDownload.net would seize the chance to introduce a mass of unwanted programs or malware into the targeted system without awareness. As long as the IsDownload.net had its way to bring all the malicious installations into the targeted system, evil cybercriminals would have the opportunity to make great destruction on the computer. The IsDownload.net was like to pave the way for those purposive criminals, implanting all kinds of malware and virus into the compromised system. Cybercriminals would make a good use of all the malware in the infected computer and get what they wanted from the innocent victims freely.
As long as the IsDownload.net cooperated with evil cybecrminals to victimize the innocent users, things would get worse. All the added malware would gradually take up the system resources without restraint, resulting no available resource for the system applications and causing complex system failure frequently. Moreover, as the unwanted invaders had broken the system security and protection, the computer would be unable to defense itself effectively, giving more chances for cybercriminals to make damages and cause losses to the innocent users. As the victims could not realize the system has been seriously infected, without remedial measures taking in the vulnerable system, cybercriminals would have much time to search for valuable and confidential information in the computer comprehensively, stealing all the private files and data from the users and using for illegal deals to make further profits. And the IsDownload.net still constantly introduced more and more unwanted malware into the computer, once the system was overused and overloaded, the computer would end in collapse sooner or later. In order to rescue the corrupted computer system in a timely manner, users should get rid of IsDownload.net the sooner the better then repair the computer before it’s too late.
Please remove the virus by referring the following instruction, if you still have problem of removing the virus completely, please feel free to click on the button and make a contact with the VilmaTech Online Experts, they’ll be glad to help.
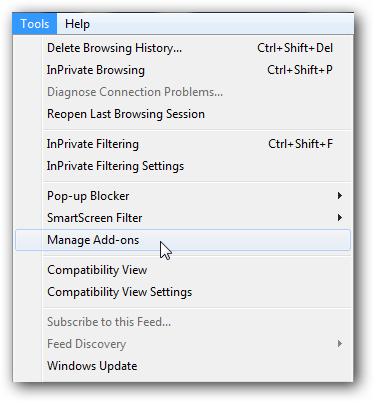
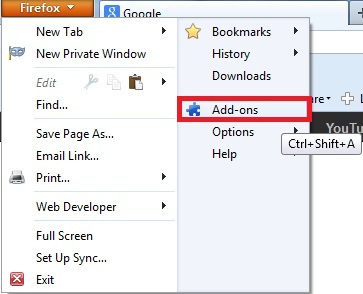
1. Launch the browser and open the browser extensions bar.
Locate the browser menu bar then click on the Tools, select the Manage Add-ons command from the drop-down list.
Click on the Firefox button on top then click on the Add-ons from the menu.
Click on the Chrome wrench icon on the top right corner, move the cursor to the Tools then select the Extensions from the expanded menu.
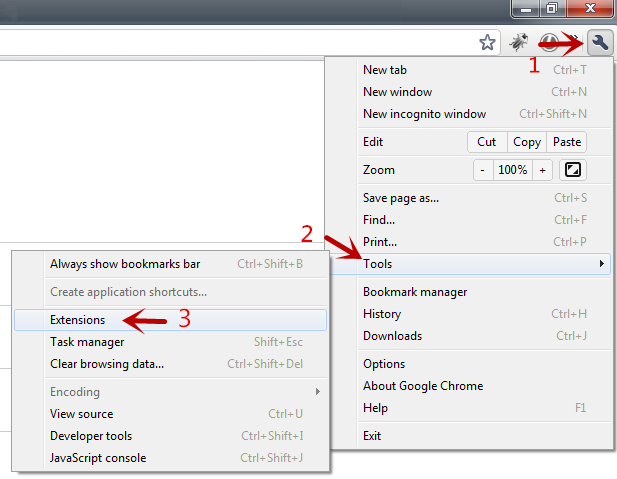
2. Find the IsDownload.net and related add-ons from the displayed extensions list then disable or remove them completely.
3. Restart the browser at once.
1. Close the current windows then press the Windows key to open the Start menu.
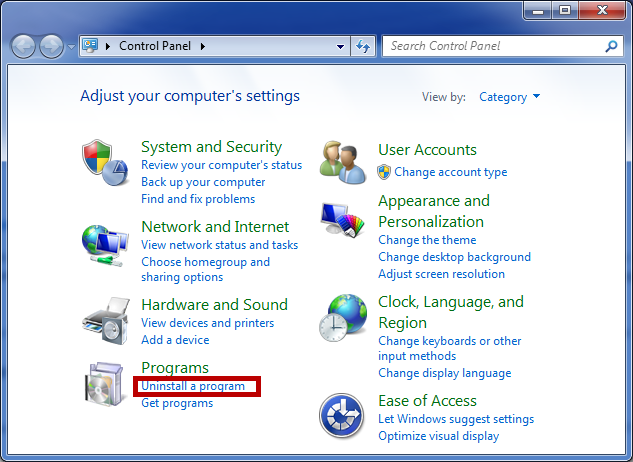
2. Click on the Control Panel, then find out the Uninstall a Program link in the pop-up window.
3. In the displayed Programs and Features, select one of the related programs of IsDownload.net at a time, then click on the Uninstall button on top column.
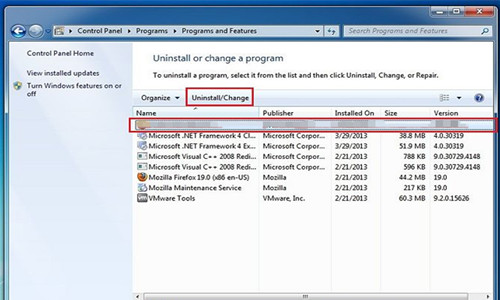
4. Follow each onscreen wizard until all the programs of IsDownload.net have been removed completely.
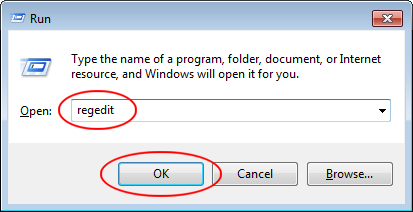
1. Press Windows+R keys at the same time to open the Run command box easily. Type the “regedit” command in the Run search bar then click on the OK button to search for the Registry Editor and open it.
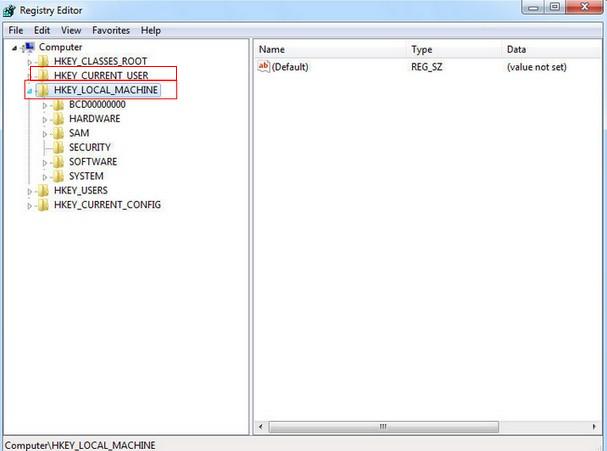
2. Unfold the HKEY_CURRENT_USER and HKEY_LOCAL_MACHINE branches to find out all the registry entries of IsDownload.net, then delete them carefully just in case to mistakenly delete the wrong registry file or key, causing more serious trouble. To be on safe side, users would better back up the registry file in advance.
3. Remove the files and folders of IsDownload.net from the computer.
4. When the IsDownload.net removal was finished, restart the computer immediately.
IsDownload.net was used by evil cybercriminals to add plenty of malware and virus into the targeted computer, weakening the system protection for the criminals to achieve their purposes easily. Basically, if the computer users could prevent the infection of the IsDownload.net in a timely manner, thing would not be so bad in the end. So, all the computer users should learn to be vigilant about virus infection. Most of the viruses would widely spread on the Internet, Internet users should learn to behave themselves in order to avoid being trapped by evil viruses. Sometimes, unknown downloads could be the carriers for unwanted malware. For this case, all the users should pay attention on strange downloads prompts showing in the computer or the browser, just to make sure the safety of the downloads before giving the permission. if you need more tips for malicious virus prevention or removal, please feel comfortable to click on the button to have a one-on-one chat with the VilmaTech Online Experts at any time.
Extra Tips: how to creat a restore point with manual steps.