HEUR:Exploit.SWF.Agent.id currently assaults individuals using Windows operating system (OS), especially those are short of appropriate security protection. It is considered as an emblematic Trojan infection designed by cyber criminals, which often acts as Backdoor. As a matter of fact, HEUR:Exploit.SWF.Agent.id, in computing is a non-self-replicating type of malware program which specializes in make destruction on affected machine with the aid of its in-built malevolent codes. To get common knowledge about HEUR:Exploit.SWF.Agent.id, it can regularly infiltrate a targeted computer through a variety of tricks. The malicious payload is being delivered to a computer by means of the infamous BlackHole exploit kit, which has the capability to excavate the security vulnerabilities in OS. Apart from the approach, malware distributors may spread the backdoor Trojan by making use of SEO poisoning techniques, which refer to the infected URLs related to recent hot events or news.
Stealthy as HEUR:Exploit.SWF.Agent.id is, it is also adept at utilizing social engineering tactics to diffuse the components of itself widely. To be specific, HEUR:Exploit.SWF.Agent.id may be distributed by compromised websites such as some P2P file sharing web pages, SPAM email offering links or attachments, infected applications carrying the activation code the virus. No matter how HEUR:Exploit.SWF.Agent.id sneaks into a PC, abnormal symptoms will be triggered without any expectation. Most commonly HEUR:Exploit.SWF.Agent.id may be used by attackers to conduct distributed denial of service (DDoS) attacks on affected machine. Serves as a backdoor Trojan, it may also have the possibility to install additional Trojans like Trojan.Win32.Bublik.cfgi (Removal Guide), or other forms of malicious software in system to lead to worse results. PC users who are stuck with HEUR:Exploit.SWF.Agent.id may also notice the slow performance of system caused by the virus. This is because HEUR:Exploit.SWF.Agent.id can often occupy high CPU utilization through make modification to Windows registry. One worst complication related to HEUR:Exploit.SWF.Agent.id should be the unauthorized access to the computer that it infects for remote hackers. This way not only user’s PC but also privacy will be at high risk.
Note: The following manual removal requires certain expertise. No single mistake is allowed. If you cannot remove HEUR:Exploit.SWF.Agent.id from PC on your own, please feel free to contact VilmaTech Certified 24/7 online experts here to help you fix the problem properly in a short time.
1. HEUR:Exploit.SWF.Agent.id may come without user’s permission or knowledge and disguises itself in root of the affected system once being installed.
2. HEUR:Exploit.SWF.Agent.id may drop and install additional threats in OS to do further harm. This may include related Trojan, worm, browser hijack virus, fake antivirus application, etc.
3. HEUR:Exploit.SWF.Agent.id may take up high system resources to slow down the performance of system.
4. HEUR:Exploit.SWF.Agent.id may help cyber criminals to track targeted machine and steal valuable information off PC user.
5. HEUR:Exploit.SWF.Agent.id may permit remote attackers to access compromised PC without any authorization.
Many PC users may notice the existence of HEUR:Exploit.SWF.Agent.id with the help of their antivirus application. However, it may fail to completely get rid of HEUR:Exploit.SWF.Agent.id infection, due to the advanced hiding techniques of the virus. Even if you have updated to the latest version of antivirus, it may still have a very low chance to terminate HEUR:Exploit.SWF.Agent.id virus totally. As a result, the helpful manual removal is strongly recommended for users to clean up all the components of the virus effectively. If you are not familiar with the process, you may start a live chat with VilmaTech 24/7 Online Experts here to resolve your problems safely and completely.
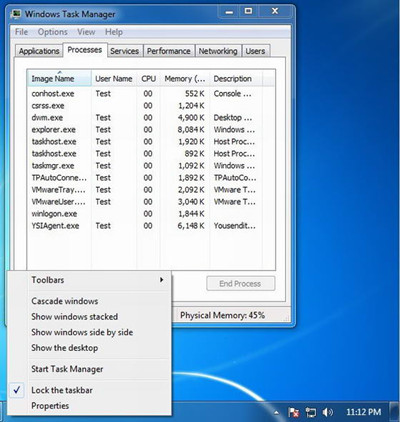
1.Kill HEUR:Exploit.SWF.Agent.id’s process in Windows Task Manager.
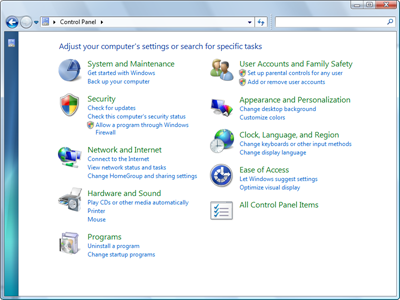
2. Show hidden files related to HEUR:Exploit.SWF.Agent.id.
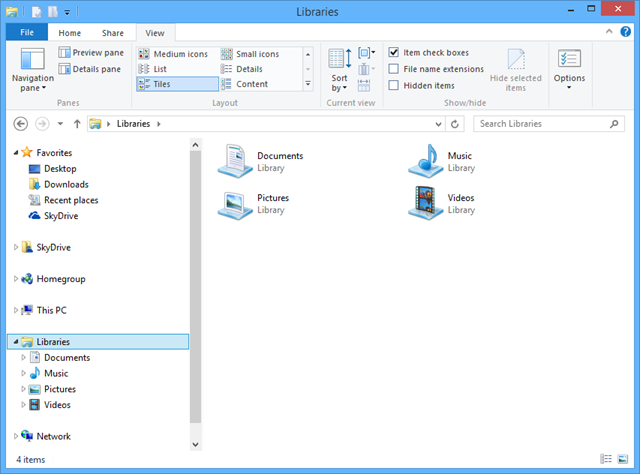
HEUR:Exploit.SWF.Agent.id will hide its files deeply in system as long as being installed. So before removing all components of the virus, it is necessary to show all hidden files of HEUR:Exploit.SWF.Agent.id. Here is how:
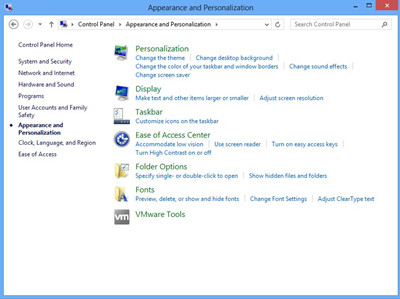
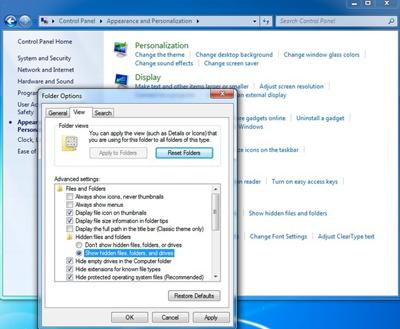
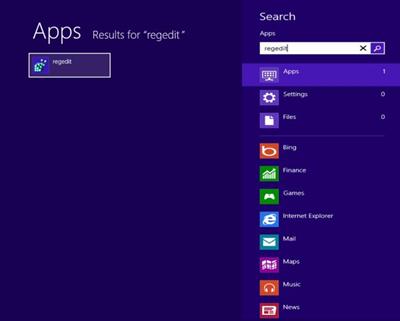
Additional steps for Windows 8:


3. Completely remove all files of HEUR:Exploit.SWF.Agent.id in hard drive.

%UserProfile%\Application Data\hotfix.exe
%UserProfile%\Application Data\thinkpoint.exe
4. Remove all registry files of Backdoor:Win32/Caphaw.AG.
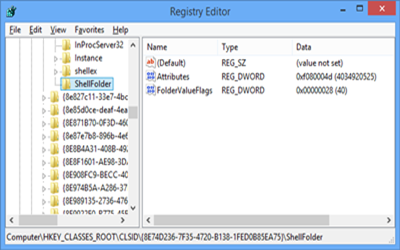
HKEY_CURRENT_USER\Software\HEUR:Exploit.SWF.Agent.id
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run “thinkpoint”
HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Winlogon “Shell” = “%Documents and Settings%\[UserName]\Application Data\hotfix.exe”
HEUR:Exploit.SWF.Agent.id is a high-risk backdoor Trojan infection designed by cyber criminals to make hazards on the computer that it infects. Similar as other common Trojan virus, HEUR:Exploit.SWF.Agent.id focuses on attacking Windows operating system (OS), including Windows 7, XP, Vista and Windows 8 (32-64bytes). According to recent security report, this type of malware can always invade a targeted computer without any permission or knowledge. By means of advanced spread tactics, HEUR:Exploit.SWF.Agent.id may be distributed by malicious websites or standard web pages that have been attacked by hackers, an infected email providing sponsored links or attachments, or some “free” applications’ downloads from unreliable Internet resources. When installed, HEUR:Exploit.SWF.Agent.id will attempt to trigger abnormal symptoms on compromised machine at an unimaginable speed. To be specific, HEUR:Exploit.SWF.Agent.id may slow down the performance of system via taking up high system resources. It can also be used by attackers to launch distributed denial of service (DDoS) attacks and drop additional threats on compromised PC by making use of found system vulnerabilities. The worse thing is, HEUR:Exploit.SWF.Agent.id may even provide unauthorized access and control to infected PC for remote hackers. This will result in unthinkable damage for user’s PC and privacy. In consequence, it is urgent to clean up HEUR:Exploit.SWF.Agent.id from computer as long as being installed. However, it may bypass the detection and auto removal by antivirus software program or other security tools. If this is the case, you may adopt the almighty manual method to get rid of HEUR:Exploit.SWF.Agent.id effectively.
Tip: Any problems during the operation, you are welcome to start a live chat with VilmaTech 24/7 Online Experts here to help you remove HEUR:Exploit.SWF.Agent.id infection manually from PC without mistake.