Have you find that your computer appears some of those following hijacking problems, if answer is yes, according to VilmaTech Security Team, you may consider if your browser and Internet suffer from Jogostempo.com Browser Hijacking.
1.If opening browser, you find that there is the unknown website called Jogostempo.com or your homepage has been replaced by it.
2.If using your default search engine to enter the key words to find what you need, you notice that the search results come from the unauthorized Jogostempo.com engine and the default search provider has been modified to another.
3.When you open a new tab or click on a new link, there is not the target page but Jogostempo.com or a blocking pop-up.
4.If opening your bookmarks or favorite website menu, you find that some unknown pages have been added onto the menu without permission.
5.When check toolbar panel, you discover that your browser has been installed unlike Jogostempo.com, but other extensions or plug-ins.

These typical symptoms are all attributed to such a kind of Internet threat called hijacking. Hijacking, also is same to browser hijacker, web page hijacking, DNS hijacking and redirect virus, which is not a technical virus but a malware. It is designed by cyber crooks and group who want to make profits from it. Though this browser hijacker is not as malicious as Trojan, virus or worm, it would damage your system gradually and then cause series of troubles, you should remove Jogostempo.com as soon as possible.
Victims of Jogostempo.com Browser Hijacker have reported that hijacker really caused a lot of troubles like home page replacement, search engine modification, unlike redirections, different bookmarks and favorite websites menu, plenty pop-ups, unwanted extensions and plug-ins installation. However, harm is too early to come to an end. Jogostempo.com, with its malicious aim, can access the target browser and Internet setting system. It will implant malicious codes to install many unwanted programs, most of which are adware and spyware, and then, available space will be occupied with rubbish files. Those malicious programs also have sponsor links, which is risky and leads to malware, spyware and virus infection. The hijacking browser would collect user’s confidence information quietly, such as, identity information, passwords, browsing history, shopping records and so on. Then it will offer those private information to the third party, according to data, who can give more pop-up advertisements to user when they surf the Internet. In addition, Jogostempo.com would block the access to security sites, like Kaspersky, Microsoft or others to prevent removing. Once system is broken, the infected computer is easy to be hacked and faced poor performance of program conflicts or errors.
Note: Although many users find their own ways to remove Jogostempo.com browser hijacker, it is not easy for you to remove Jogostempo.com completely from your computer. If other methods cannot help you to get a complete Jogostempo.com browser hijacker removal, please follow steps below to manually clean it up. If there is any question or something wrong, feel free to chat with our VilmaTech experts for help to remove Jogostempo.com browser hijacker.
In most cases, victims have no idea that how the nasty process enters their browser and computer. Most of hijacker infection like Jogostempo.com are because of users’ drive-by-download. In a word, the hijacker can implant into the computer without permission and notification. Jogostempo.com browser hijacker may be embedded into potential unwanted program from third party like adware that users download free from program website or undetected share ware from unsafe and suspected site. Jogostempo.com browser hijacker can be hidden in the entry files and launched when the certain program is installed.
Also, it can take full advantage of browser helper object which is a legal interactive interface where programmers can use code to access and add buttons. As a part of browser, browser helper object can be utilized by cyber criminals to take to their activities. In addition, Jogostempo.com browser hijacker can be distributed by hook. Hook is programmed as DLL file that it is able to block the message of solicitation to a desirable site and achieve redirection. In addition, the cyber criminals may use Windows Socket Layer Service Provider associated with SPI to get user’s transmitting data no matter you are using Firefox or IE. After successfully entering computer, Jogostempo.com browser hijacker will create its code, reside in related folders and temper with entries. Besides that Windows system is easy to be the aim of hijacking, according the global cases, Safari browser is possible to get it.
1.First, quit from the current browser and click on the X button on the display window.
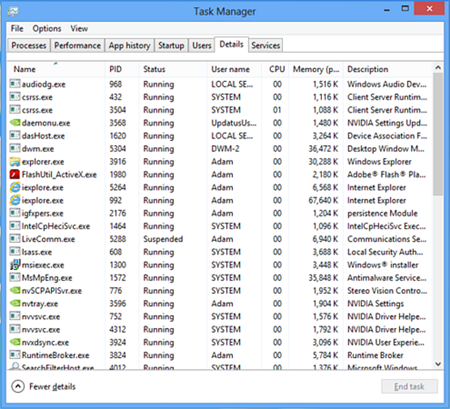
2.Hold a combination of “Alt” “Ctrl” and “Del” three keys on the keyboard to open Task Manager and choose Process tab. Select the running process of your browser and other processes related about Jogostempo.com. And then click OK to save the change. If this step is not very effctive to stop the hijacking browser, please follow steps below continuously.
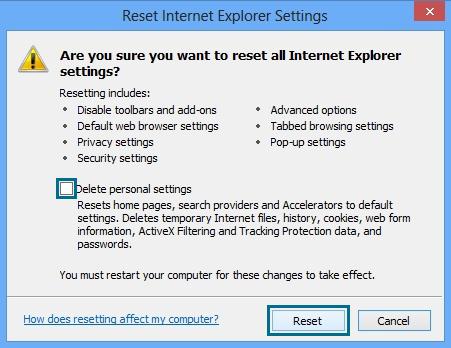
Open Control Panel and choose Internet Options image. With the open window, choose Advanced tab and then hit “Reset” button. When it pops up a window ask if there wants to reset all IE settings, check the term “delete personal settings” and click on the reset button of the current window.
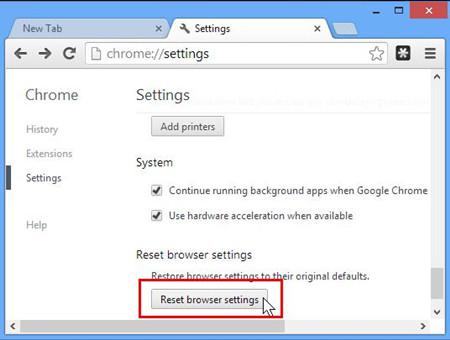
Click on the gear icon or open the button of three strips at the top right of Chrome, open the drop-down menu to choose Settings option. In the showing window, move to the bottom and click on underlined “show advanced settings” in blue. Then click “Reset Browser Settings” button in the next pop-up window. There will be a new display window to ask if you want to reset all settings, and click “Reset” to agree.
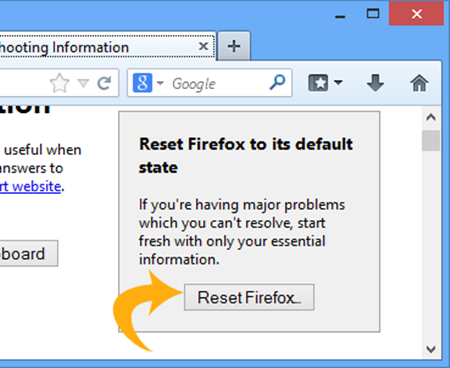
Click on the Firefox orange button to open the drop-down menu, and choose “Help” option. Then choose the term labeled “Troubleshooting Information”. In display window, it has a shading part of “resetting Firefox to its default state” on the right, so you can click on “Reset Firefox” button. When it shows a pop-up window to ask you to ensure the action, click on “Reset Firefox” in showing window. Then click on Finish button when it end the whole resetting.
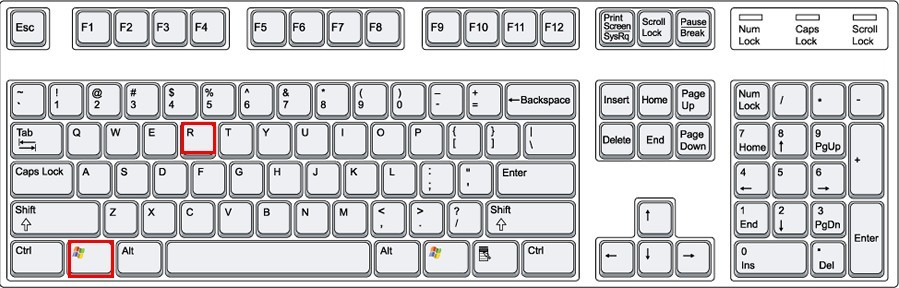
1.Hold a combination of “Windows” plus “R” two keys on the keyboard to open Run Command Box and then type “C:\Windows\System32\drivers\etc\” and click OK button to search for Hosts file. Or, you can access to Windows search blank and type in “hosts” to find Hosts file.
2.When the window show Host icon, right click on it and choose “open with notepad” option in the menu.
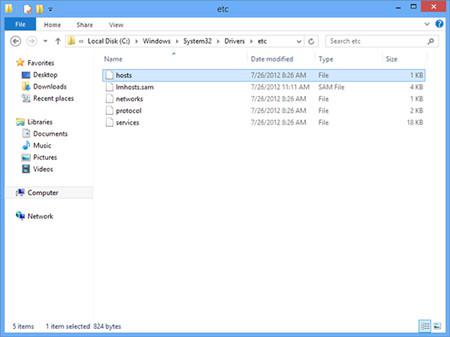
3.Then, it appears as note Format. Find out the line of Jogostempo.com website, and delete the line.
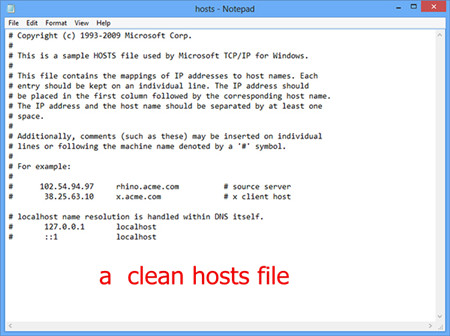
4.After the above steps, open File tab of the window and choose Save option to end the change.
1.Access to the desktop or File Explorer, find out the icon of hijacked browser. Right click on the image and open a menu, and then choose Properties option.
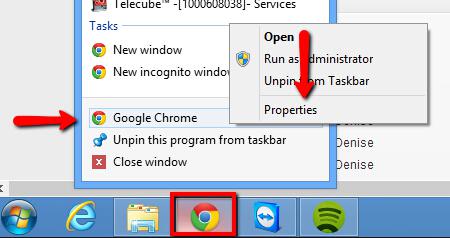
2.In the showing window, select Shortcut tab and navigate “Target” line. If you find there is hijacker address, highlight the website address and right click on it. When it appears a menu, choose Delete option.
3.Next, select General tab and check the term “read-only”. Finally, click OK to save the change.
1.Open the Control Panel and click on the “Uninstall a program” in Program Section.

2. Navigate the list of the programs and select suspicious programs like adware, search provider, plug-in related or those installing in system without your permission. Click on Uninstall button.
3.A pop-up window appears to ask if you want to uninstall the programs, just click Yes to agree.
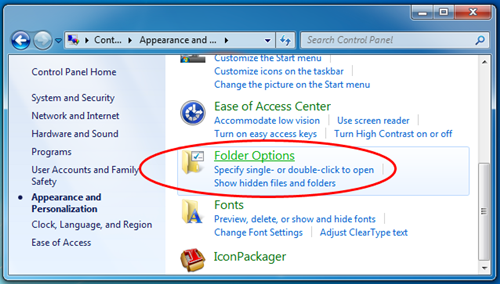
1.Access to Control Panel to find out Appearance and Personalization icon, then click on it and then choose Folder Options.
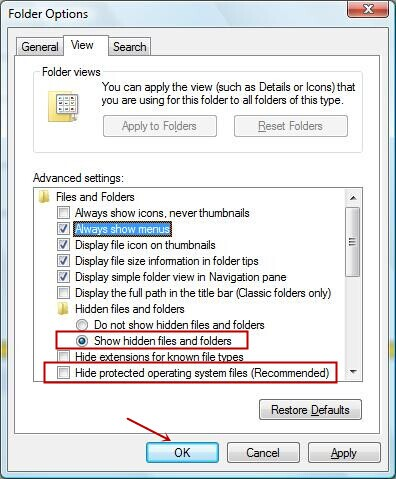
2.In displaying window, choose View tab and scroll down to check the term “show hidden files, folders and driver”. And then click OK to save change.
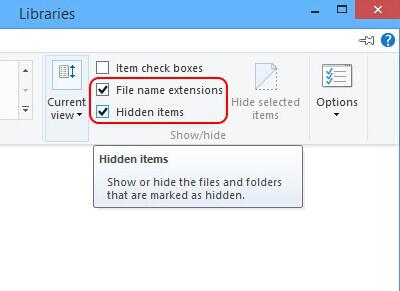
3.If you are Windows 8 user, you need to access to File/Windows Explorer. In showing window, choose File tab and check the term “show hidden items” and “file name extensions” as “show hidden file” operation. Click OK to save change.
4.Access to C:\ disk and navigate the malicious and infected files of Win32/Toolbar.MyWebSearch.W hijacker. Check following reference to delete all related files and folders.
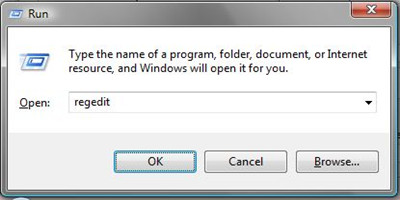
1.Hold a combination of “Windows” and “R” two keys on the keyboard to open Run Command Box, and then type “regedit” in the search blank and press Enter to access to Registry Editor operating window.
2.Unfold the HKEY in the left pane and navigate the subkeys related and the values named random characters. Right click on them and choose “Delete” option in the menu.
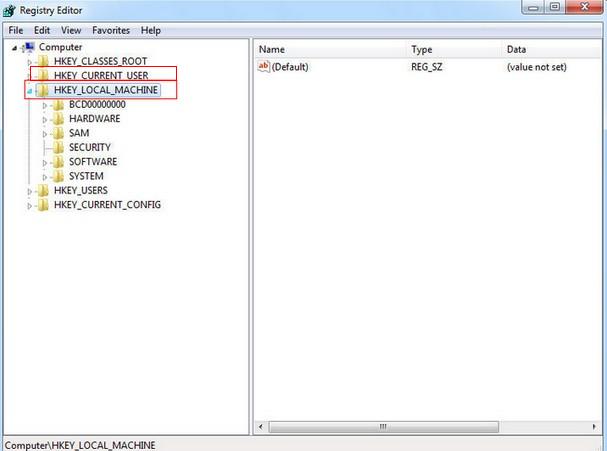
3.Finally, empty Recycle Bin and reboot computer and browser to check if it works.
Tips: This step refer to the key part of system. One wrongly deleting operation may attribute to system termination or crash down, so we suggest you to back up the entries if you can’t ensure.
If you still have any trouble of removing the Jogostempo.com, you can click on the button and ask the VilmaTech Expert for some help.
Having mentioned the Jogostempo.com Browser Hijacker, we have some tips for you to avoid malware. Firstly, users should set up safety conscious and must know that the Jogostempo.com Browser Hijacker can enter browser and computer by drive-by-download, which means that any suspicious program installation from third party can lead to hijacking attack. So it is essential to develop a good and discreet browsing habit. When you want to install an application, it is important to read the terms and policy carefully and be cautious to the installation options. Secondly, pay attention to those pop-up banners or with attractive information such as reward and coupons, also the recommendation of a certain plug-in and program from third party. Thirdly, never get the illegal copyright software or applications, and don not click any unknown-source link or doubted website. At last, users have better to install reliable and reputable antivirus program.
Now, browser hijacker is an common cyber threat to Internet security, so users need to know more about it and take actions to prevent from in daily browsing. Jogostempo.com Browser Hijacker spread in a sneak way and implant into computer without users’ permission. Jogostempo.com Browser Hijacker would slowdown the speed of computer, cause private information exposure and even other infection like virus, Trojan and spyware. However, it is not a simple job for unfamiliar user to get a complete removal off the Jogostempo.com Browser Hijacker,. Then, there is the method can deal with this hijacker and users can take it easy. Only need to do is following the instructions from VilmaTech Experts or having chat with the online technicians to get assistance. Take the danger of Jogostempo.com Browser Hijacker into consideration, it is advisable to get rid of it completely as soon as possible.
* Here is an extra help to create a restore point all by yourself easily.